Windows Legacy Updates
legacyupdate.netGetting error 8007EFE when checking for Windows Updates on your old version of Windows? Legacy Update continues support for Windows XP, Vista, 7, 8.1, etc. where Microsoft left off.
309 links
Getting error 8007EFE when checking for Windows Updates on your old version of Windows? Legacy Update continues support for Windows XP, Vista, 7, 8.1, etc. where Microsoft left off.
Last April, I wrote a well-received article about the 13 software engineering laws - Hyrum’s, Conway’s, Zawinski’s, and 10 famous others.

Some days I get in bed after a tortuous 4-5 hour session working with Claude or Codex wondering what the heck happened. It's easy to blame the model - there'...

Tu viens de monter un nouveau serveur Linux (un VPS, une VM Proxmox, un Raspberry Pi), SSH est activé, tu t'y connectes avec ton mot de passe, ça marche, affaire classée. Sauf que si ton serveur est exposé sur internet, il se fait scanner en continu par des bots qui
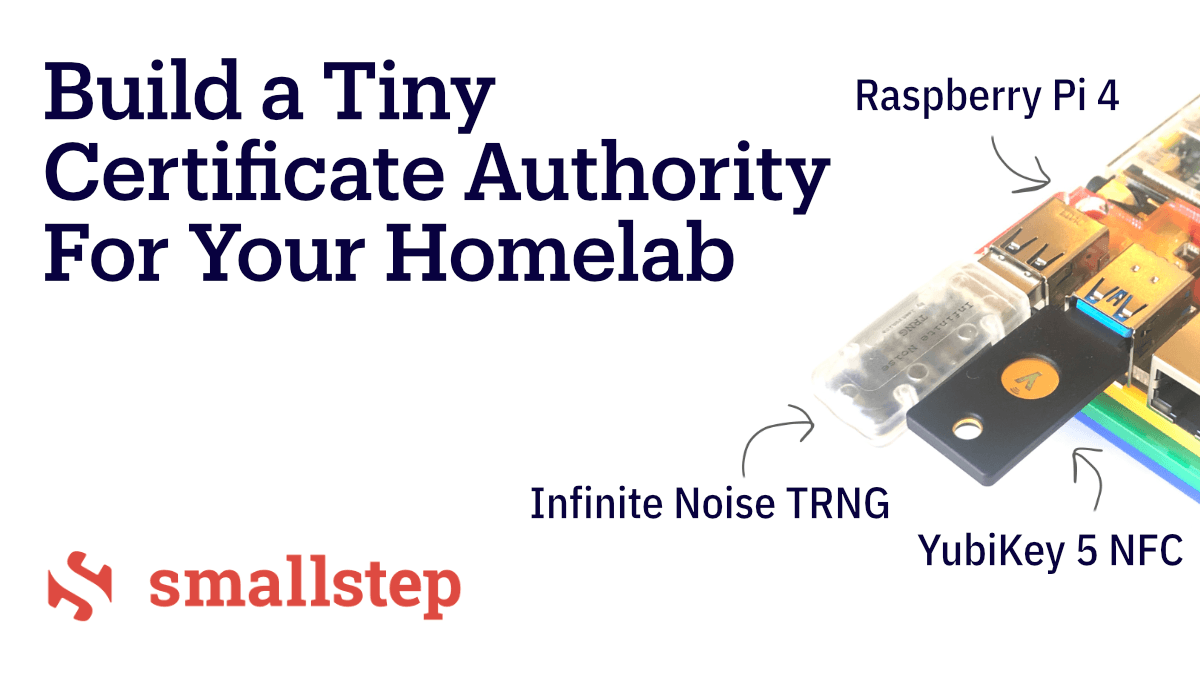
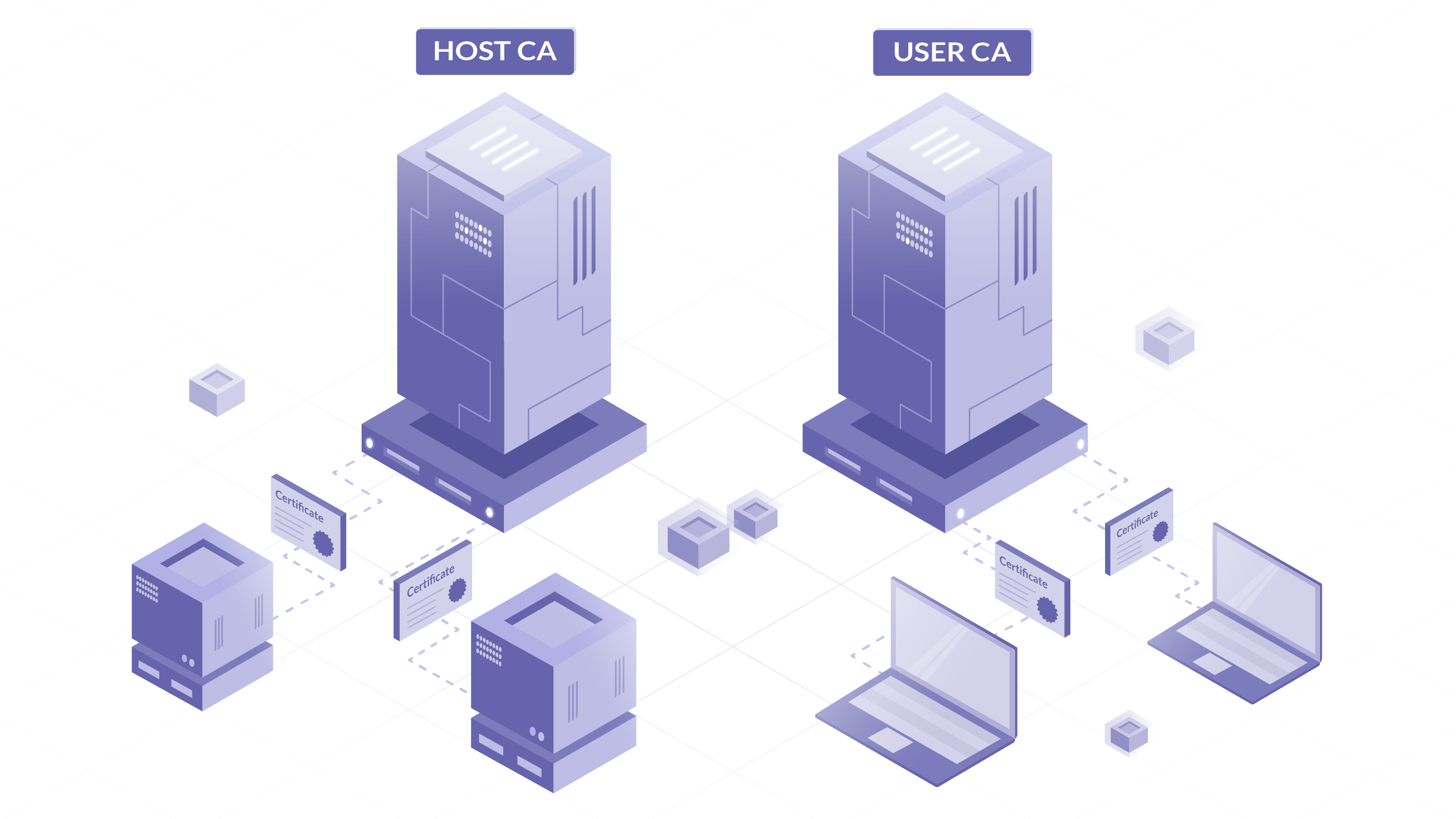
Let's make a tiny, standalone CA! We'll use a Raspberry Pi 4, YubiKey 5 NFC, and Infinite Noise TRNG.

Introduction
Knock Knock Knock ! Connaissez-vous le port knocking ?
Le tocage à la porte, ou port-knocking, est une méthode...
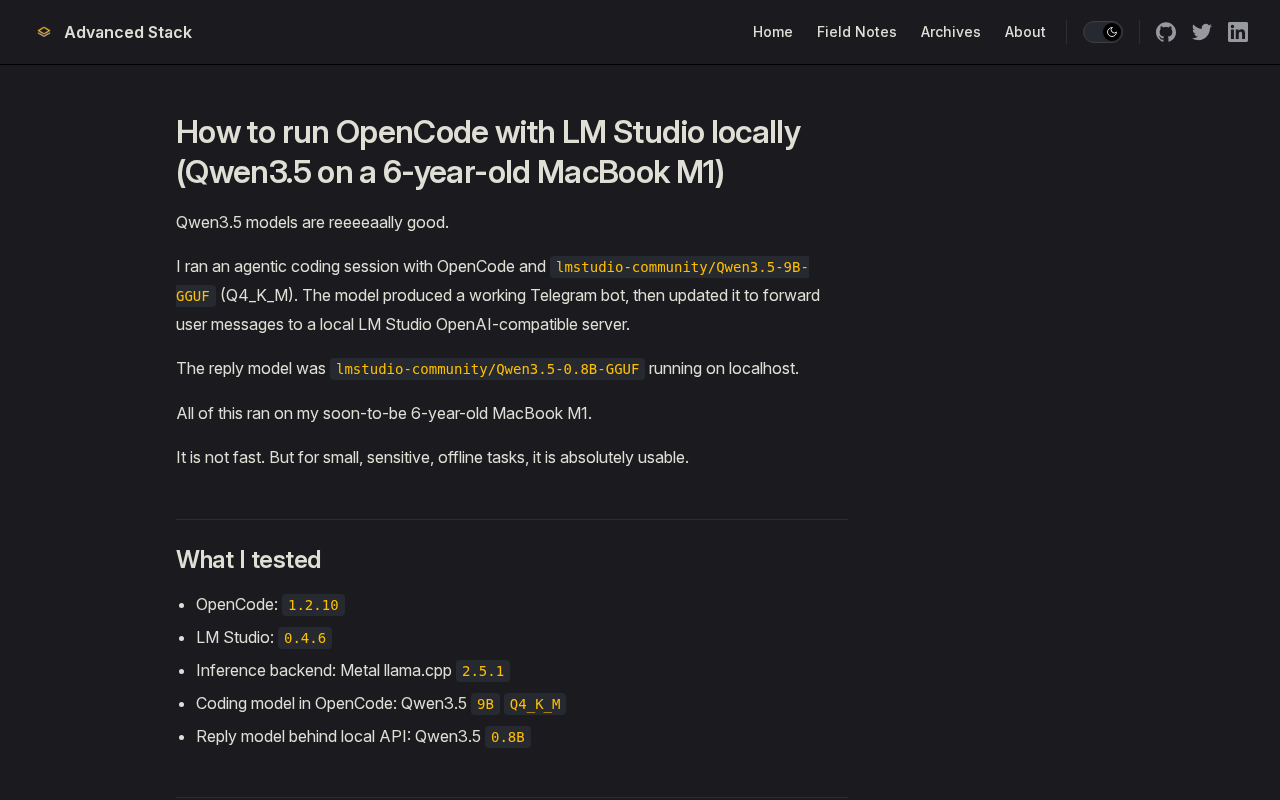
Step-by-step field note for running OpenCode with LM Studio locally using Qwen3.5 9B and 0.8B, including Telegram bot workflow, local config, and M1 performance tradeoffs.

Talk to your infrastructure in plain language, get instant answers, and keep everything on-prem if you want.

Zero-touch node patching for Proxmox clusters bygyptazy.
The biggest shock of my early career was just how much code I needed to read that others wrote. I had never dealt with this. I had a hard enough time understanding my own code. The idea of understandi
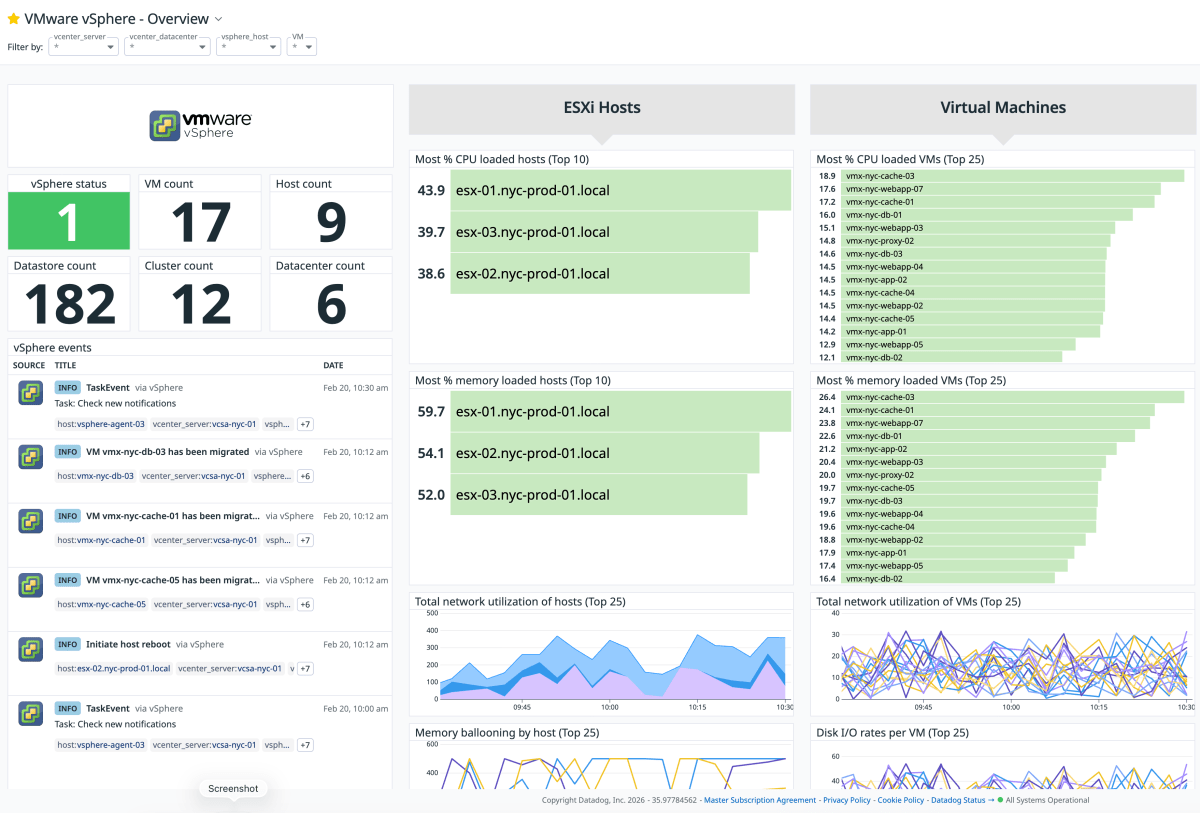
Installer Datadog sur un homelab vSphere peut sembler contre-intuitif à cause du coût habituel de la plateforme, mais cela présente des avantages réels en termes de gain de temps et de fonctionnali…
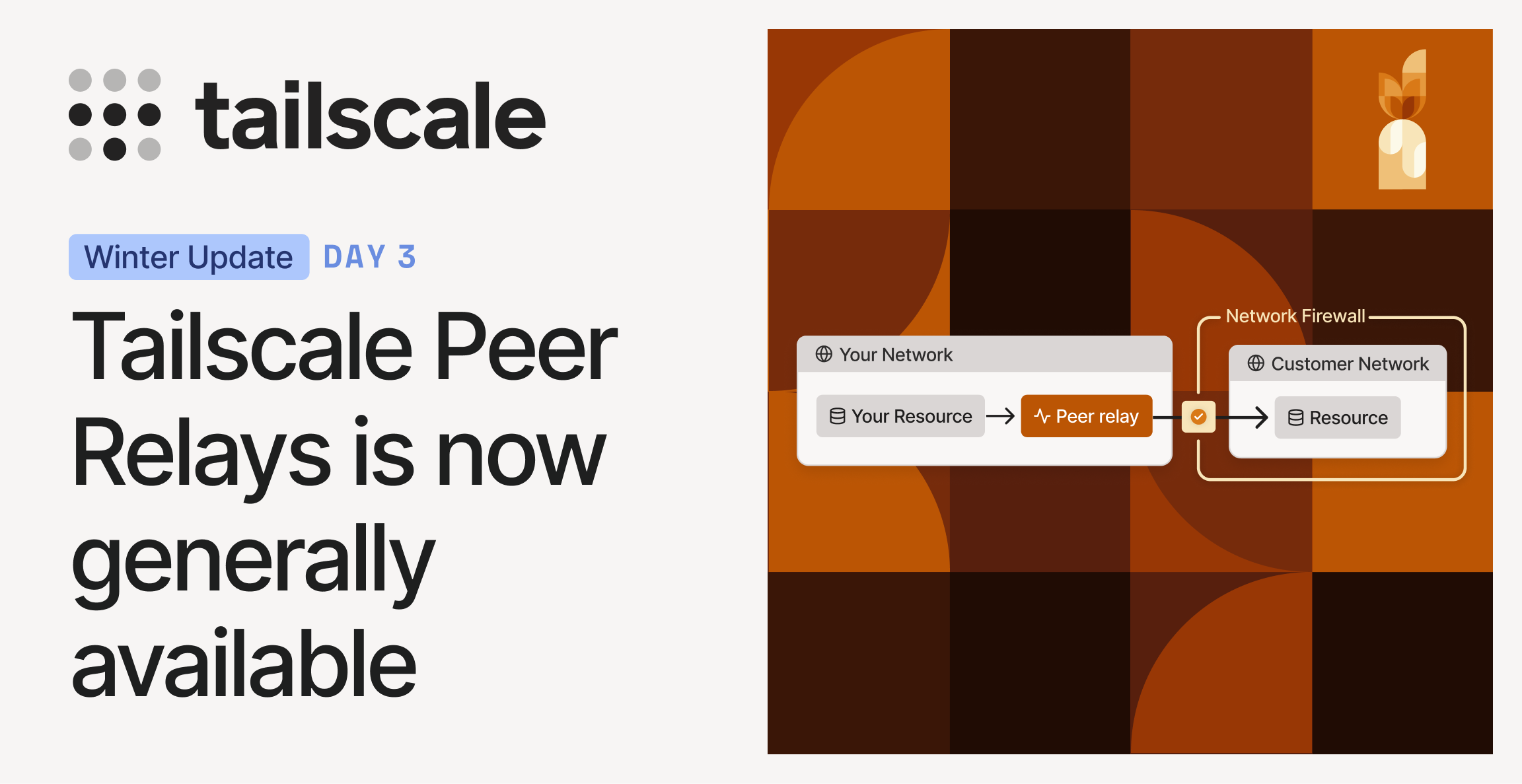
Work around hard NATs and tricky networks with production-grade connectivity nodes you control

An open-source Windows and Office activator featuring HWID, Ohook, TSforge, and Online KMS activation methods, along with advanced troubleshooting.
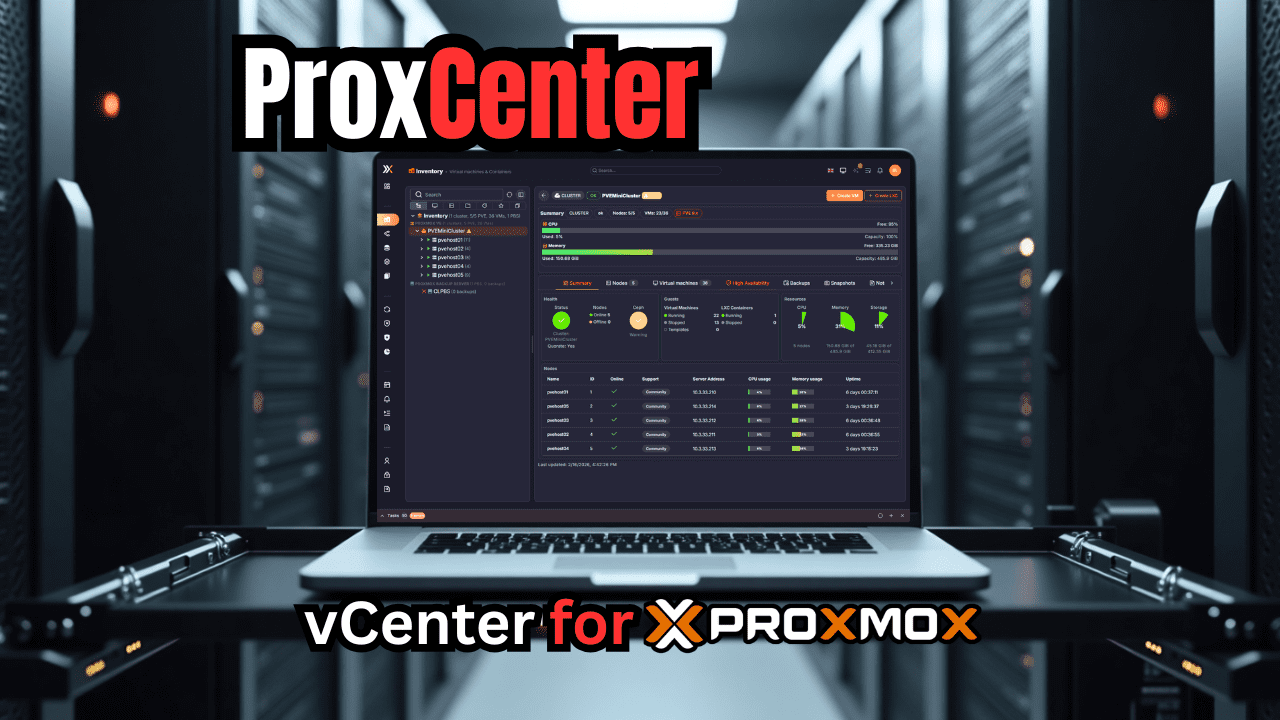
Is ProxCenter the vCenter for Proxmox? A deep look at ProxCenter for Proxmox, including DRS, HA, rolling updates, and multi-cluster management.

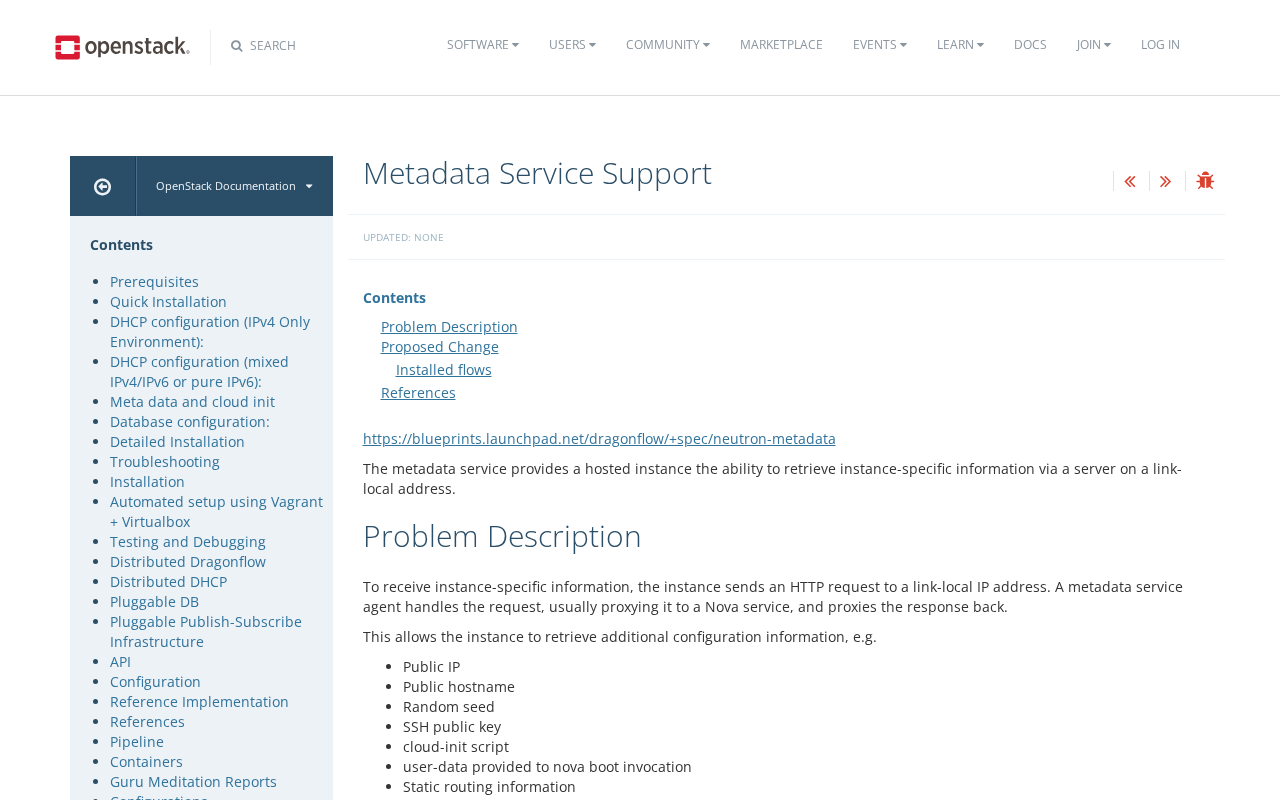
When you request a certificate from Let’s Encrypt, our servers validate that you control the hostnames in that certificate using ACME challenges. For subscribers who need wildcard certificates or who prefer not to expose infrastructure to the public Internet, the DNS-01 challenge type has long been the only choice. DNS-01 works well. It is widely supported and battle-tested, but it comes with operational costs: DNS propagation delays, recurring DNS updates at renewal time, and automation that often requires distributing DNS credentials throughout your infrastructure.
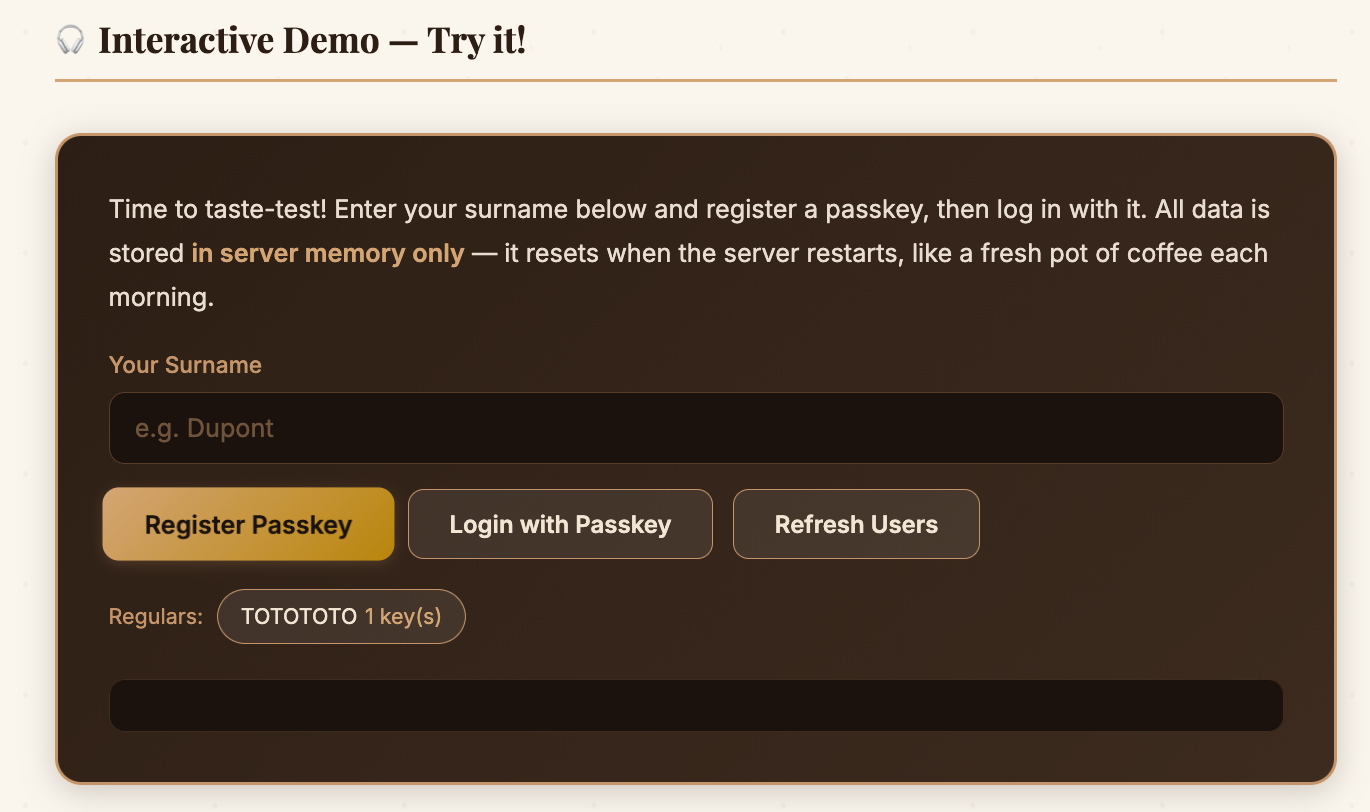
Learn how passkeys work with interactive diagrams and a hands-on WebAuthn demo. From cryptography to code, all explained over a cup of coffee.
Deploy More Resilient Apps. Hatchet is a platform for building distributed web apps that solves scaling problems like concurrency, fairness, and rate limiting.
You never have to see comments again if you don't want to.
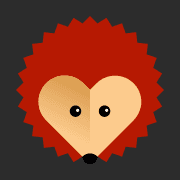
Give LLM agents shell access without risking your host system. A practical libvirt guide covering VM creation, snapshots for safe experimentation, and remote access options.
On January 14, 2026, global telnet traffic observed by GreyNoise sensors fell off a cliff. A 59% sustained reduction, eighteen ASNs going completely silent, five countries vanishing from our data entirely. Six days later, CVE-2026-24061 dropped. Coincidence is one explanation.
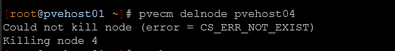
If you work with Proxmox clusters long enough, you will likely have a cluster that you need to remove a node from. This is a fairly easy process using...
Comment j'ai obtenu mon propre ASN et utilisé BGP pour annoncer des routes IPv6 depuis chez moi.

Crack, splash, boom! In 2024, the VMware ecosystem endured a seismic shift. Broadcom acquired VMware and quickly introduced a controversial change in its pricing model — shifting from a vRAM-based system to one centered on per physical core (pCore) licensing — and shaking the veritable ground users stood upon. What once allowed customers to pay for […]
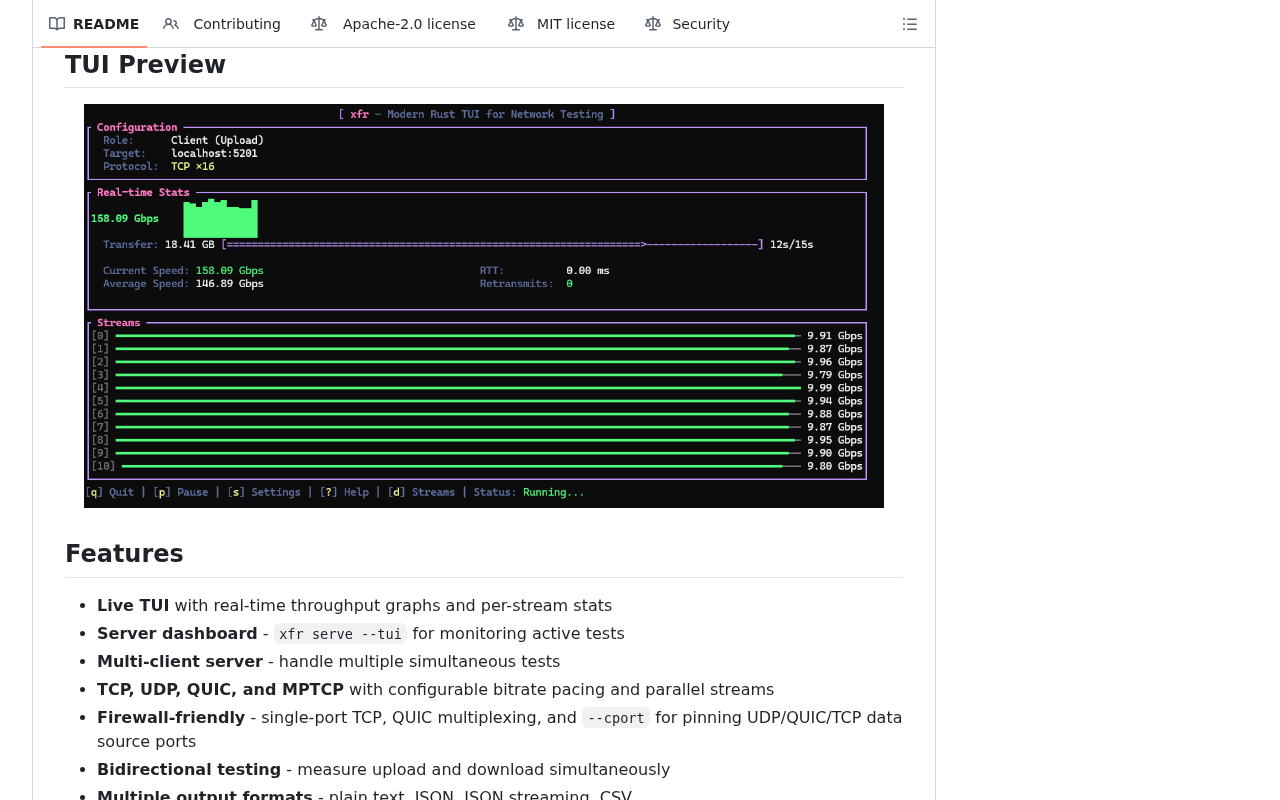
A modern iperf3 alternative with a live TUI, multi-client server, and QUIC support. Built in Rust. - lance0/xfr
Author: Nemanja Ilic
We built an open-source proxy that adds tenant isolation to Prometheus, Loki, and Tempo by rewriting queries based on user identity.
A gentle introduction to the Pi coding agent and why I think it’s a glimpse into the future of software.
Accurate vNIC-to-IP mapping is fundamental for virtual networking visibility, security, and troubleshooting. On the Nutanix AHV hypervisor, this mapping becomes especially important for services like Flow Virtual Networking, microsegmentation,...
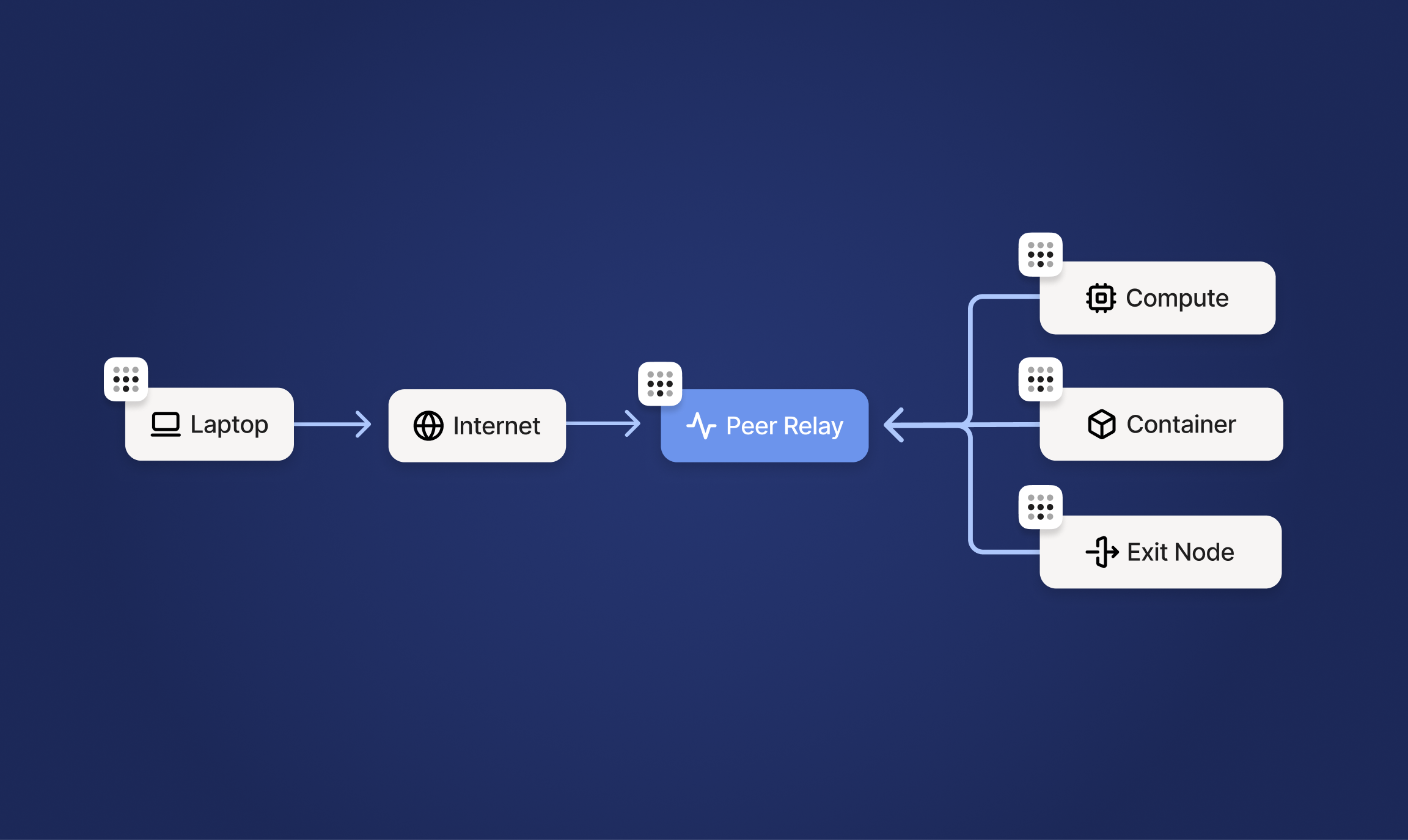
Getting from Delhi back to a Minnesota meant unforgiving networks. Tailscale Peer Relays offered a massive improvement.
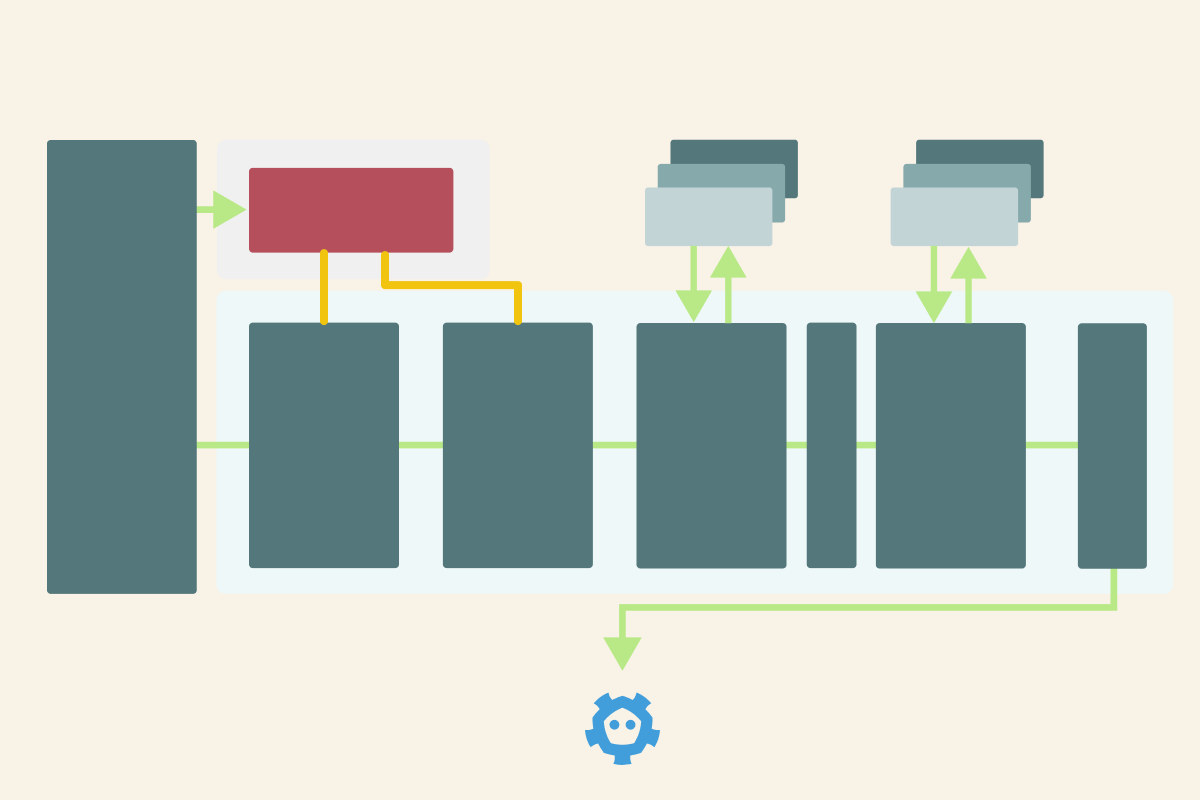
Learn how requests flow through the Kubernetes API server — from authentication to etcd storage.

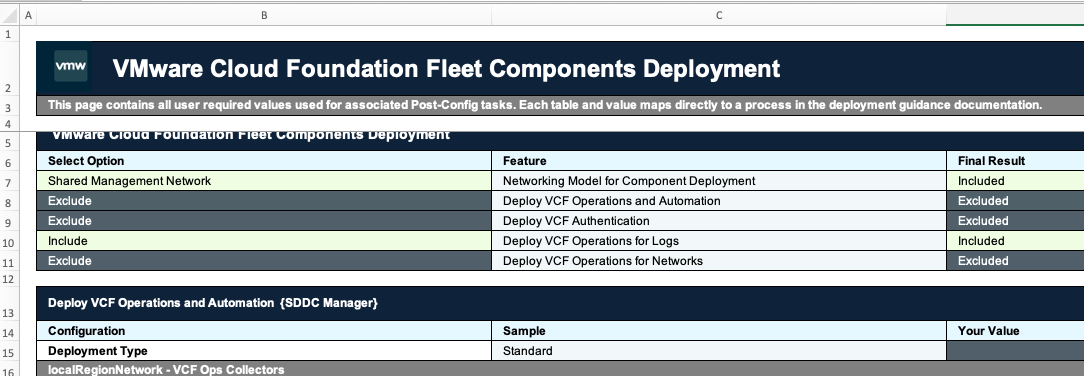
This guide covers patching the entire VCF 9 platform including all fleet level and domain level components with a full end to end guide

Today is a big day for us, and for everyone who cares about transparency, privacy, and having full control over their own traffic. We’re finally open-sourcing the protocol that powers AdGuard VPN. And it now has a name: TrustTunnel.
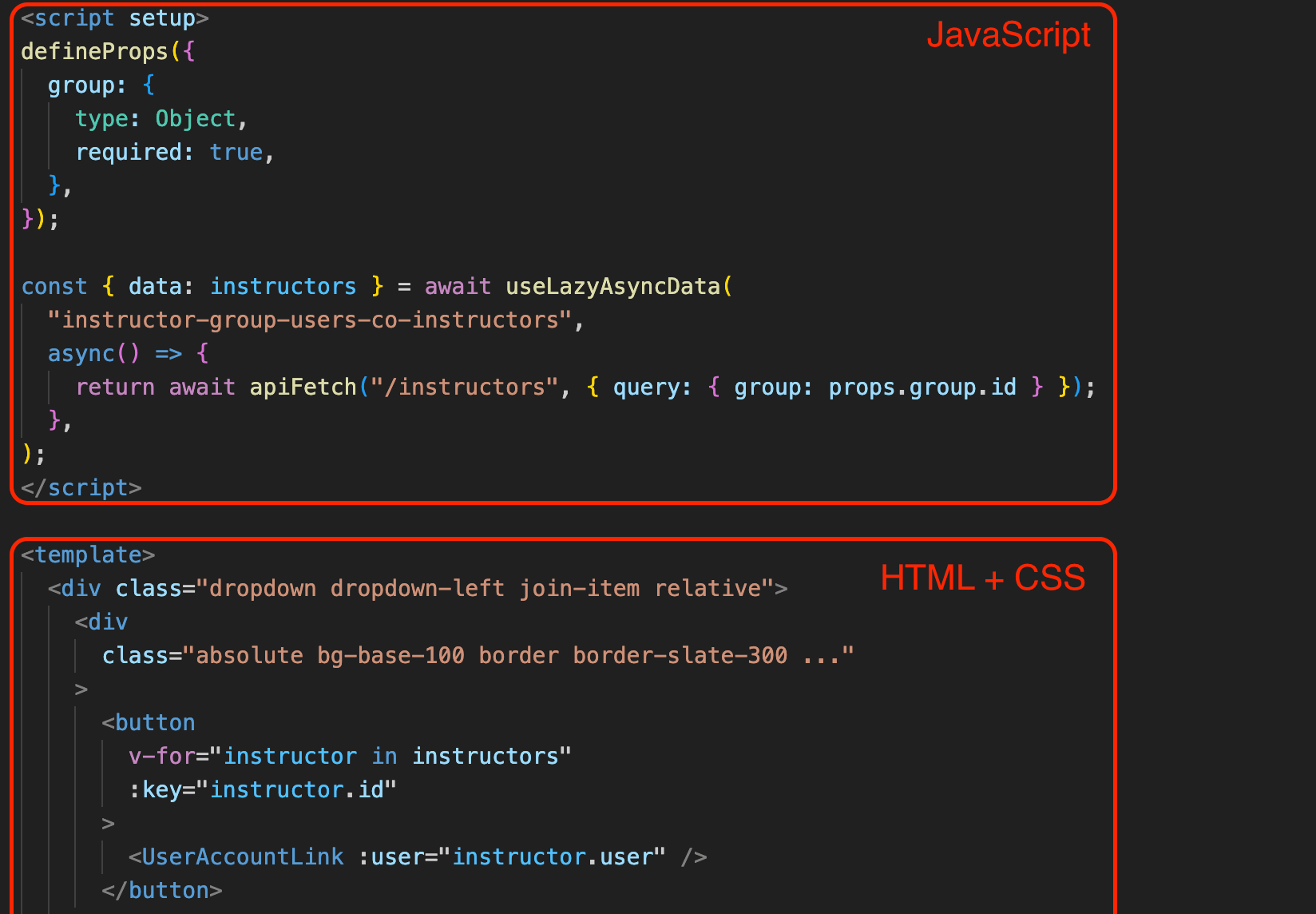
iximiuz Labs founder shares a grounded, hands-on look at agentic coding in a real production codebase: massive speedups, surprising failures, and why domain knowledge still matters most.
| Small Office/Home Office (SOHO)| Small-to medium-sized business (SMB)| Medium-to large-sized enterprises (MLE)
●
Litestar | Effortlessly Build Performant APIs
GoReplay is a versatile open-source tool designed to capture and replay live HTTP traffic. Perfect for replay production traffic and conducting comprehensive traffic replay testing, it allows you to seamlessly record and replay traffic in staging environments for effective debugging and quality assurance.
A modern, unofficial ProtonVPN Terminal User Interface (TUI) for Linux, written in Rust. - cdump/proton-tui
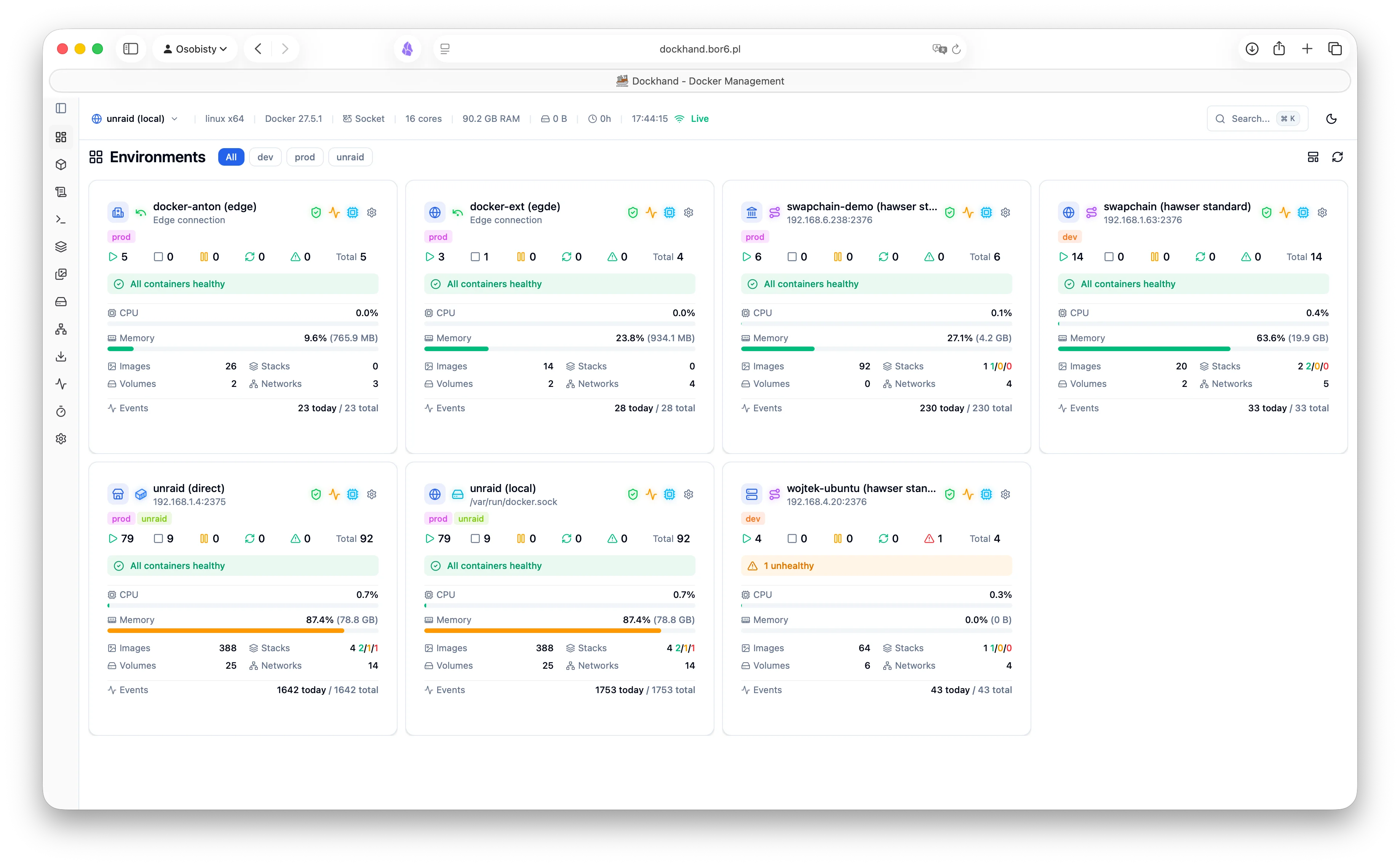
A powerful, intuitive Docker platform for everyone. Real-time container management, Compose stacks, Git deployments, and SSO - all free.

Datadog cut off our observability overnight. We migrated to an open Grafana stack in 48 hours. Here’s why vendor lock-in is fading in an AI-native world.
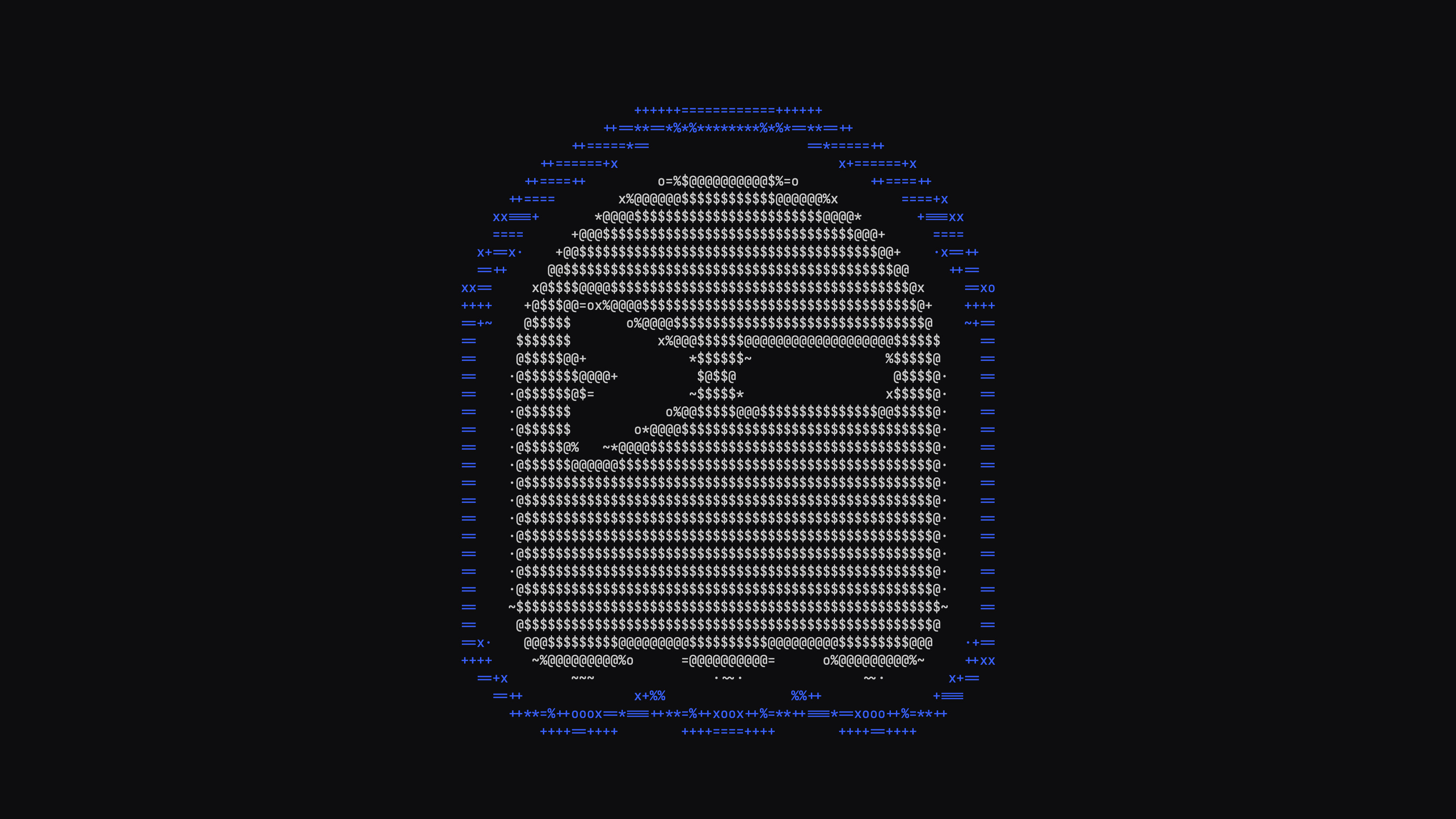
A look at how I used shape vectors to achieve sharp, high-quality ASCII rendering.
Terra is the community Fedora repository which makes it easy to install and maintain software packages.
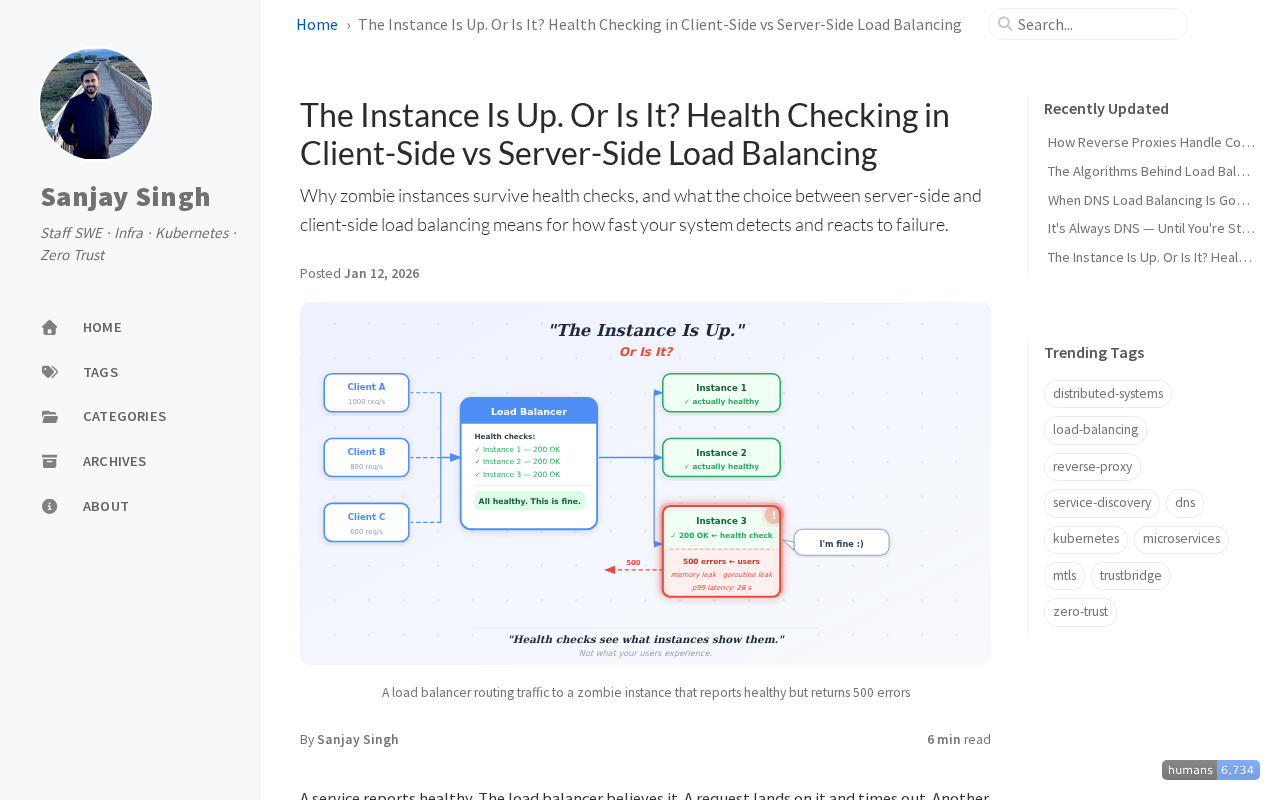
Why zombie instances survive health checks, and what the choice between server-side and client-side load balancing means for how fast your system detects and reacts to failure.
An inspection of Claude Code's network requests, system prompt, and context handling by intercepting real traffic.
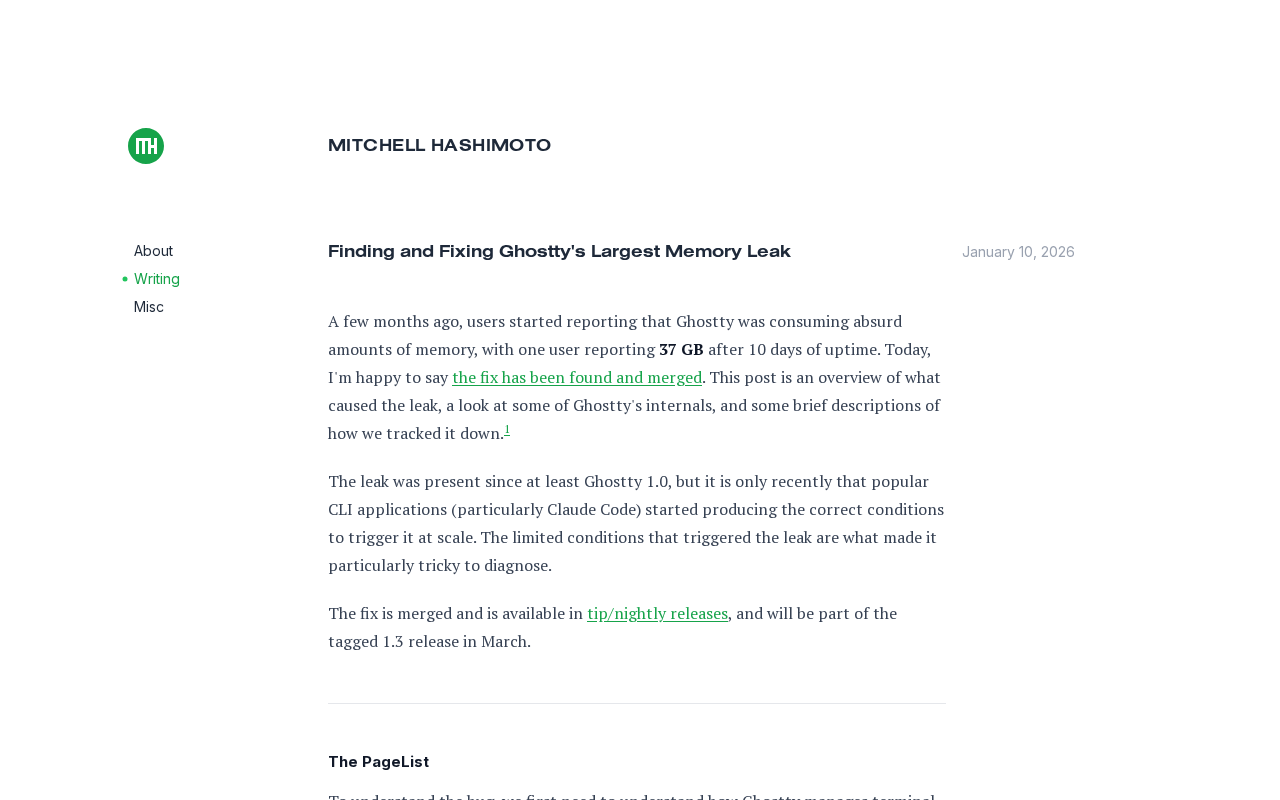
A few months ago, users started reporting that Ghostty was consuming absurd
amounts of memory, with one user reporting37 GBafter 10 days of uptime.
Today, I'm happy to saythe fix has been found and me

We usually learn that 1 kilobyte is 1024 bytes, 1 MB is 1024 kilobytes, etc. But is this true or a kilobyte is precisely 1000 bytes?
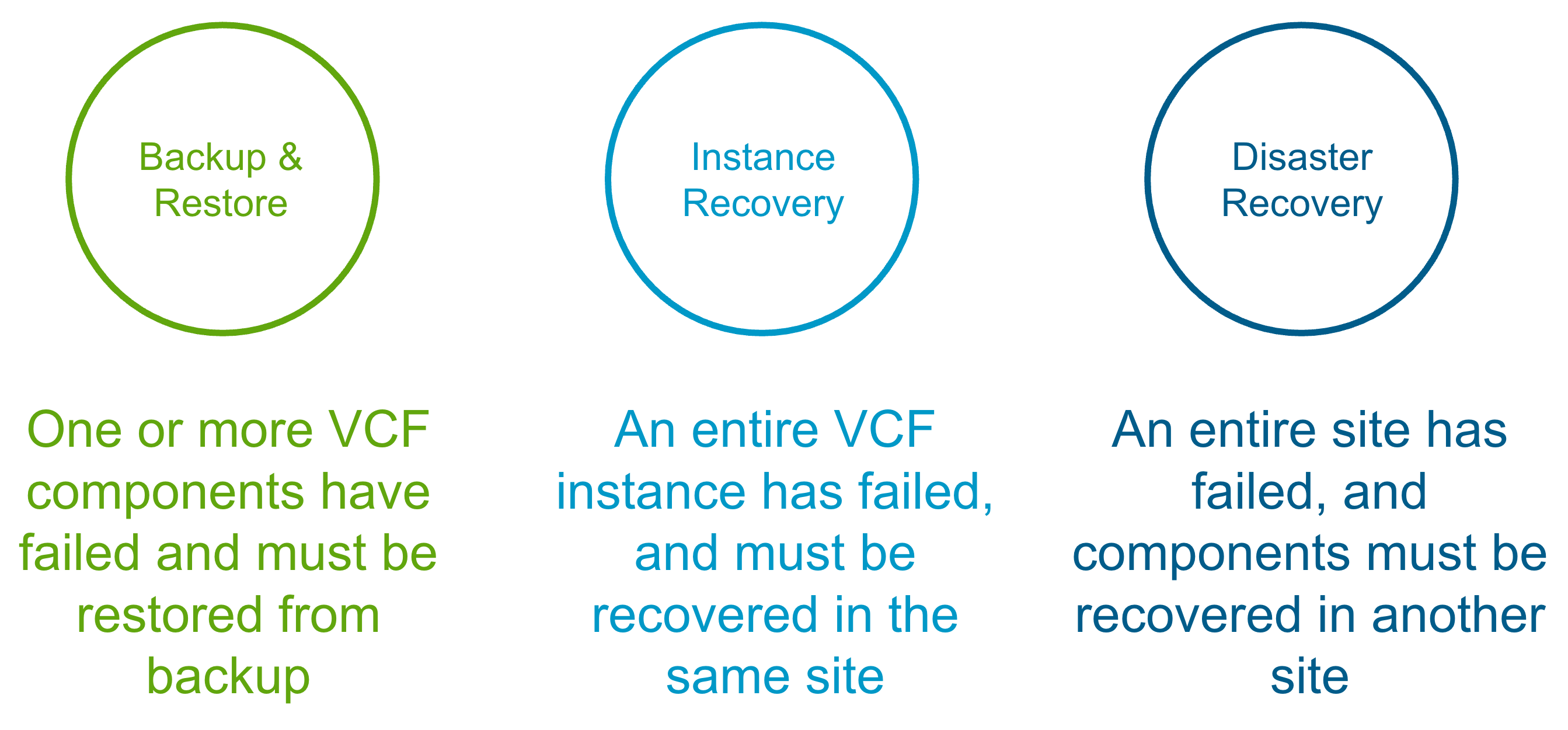
Protection & more importantly, recovery of VMware Cloud Foundation (VCF) is something I and Ken Gould have worked closely on for a number of years now. Whether it was a VVD based deployment or …
In VMware Cloud Foundation (VCF) 9.0, identity management takes a leap forward with the introduction of the VCF Identity Broker (VIDB)—a modern, flexible solution for enabling Single Sign-On (SSO) …

Lessons learned from 14 years of engineering at Google, focusing on what truly matters beyond just writing great code.
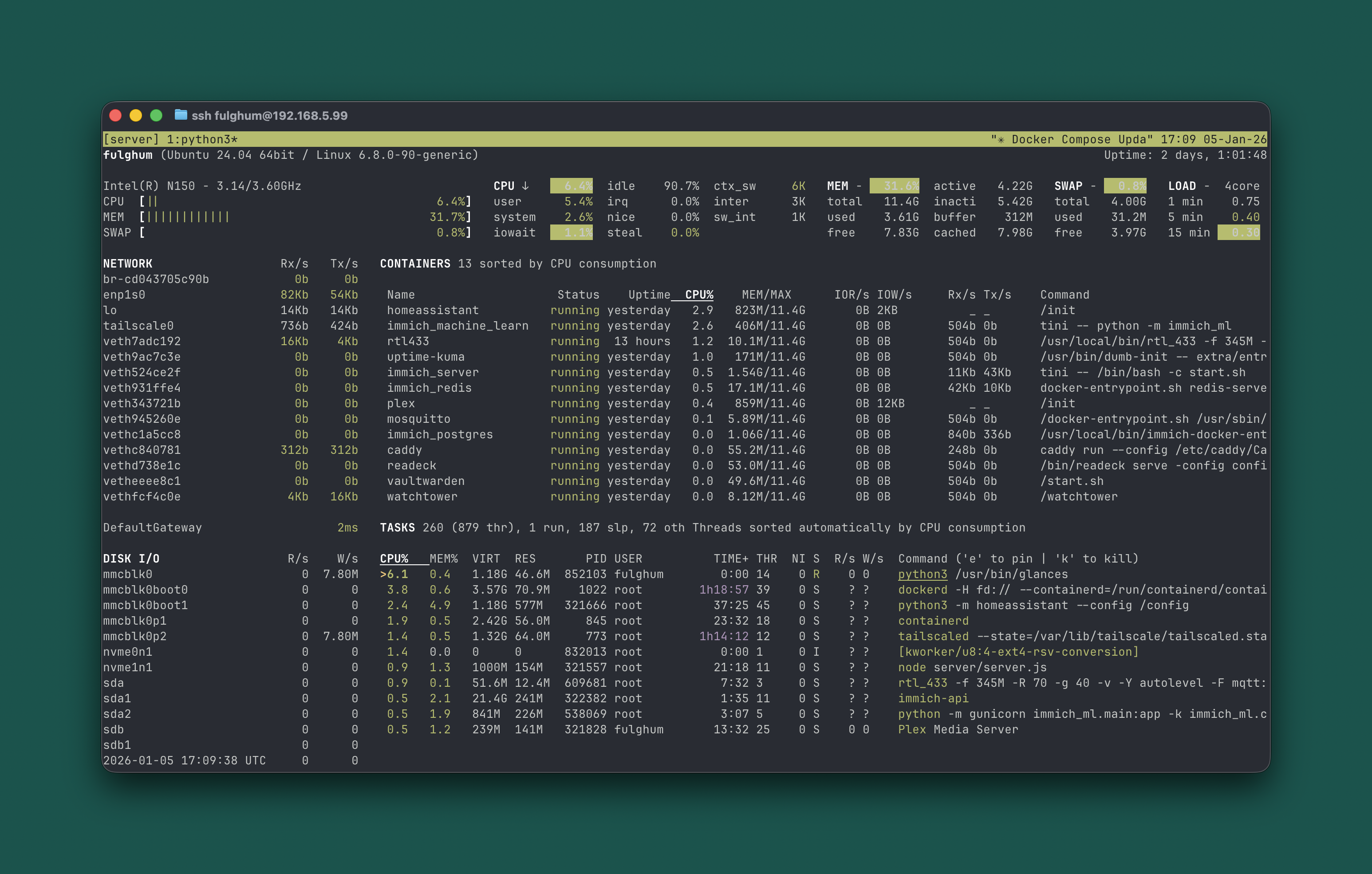
CLI agents like Claude Code make self-hosting dramatically easier and actually fun. This is the first time I would recommend it to normal software-literate people.
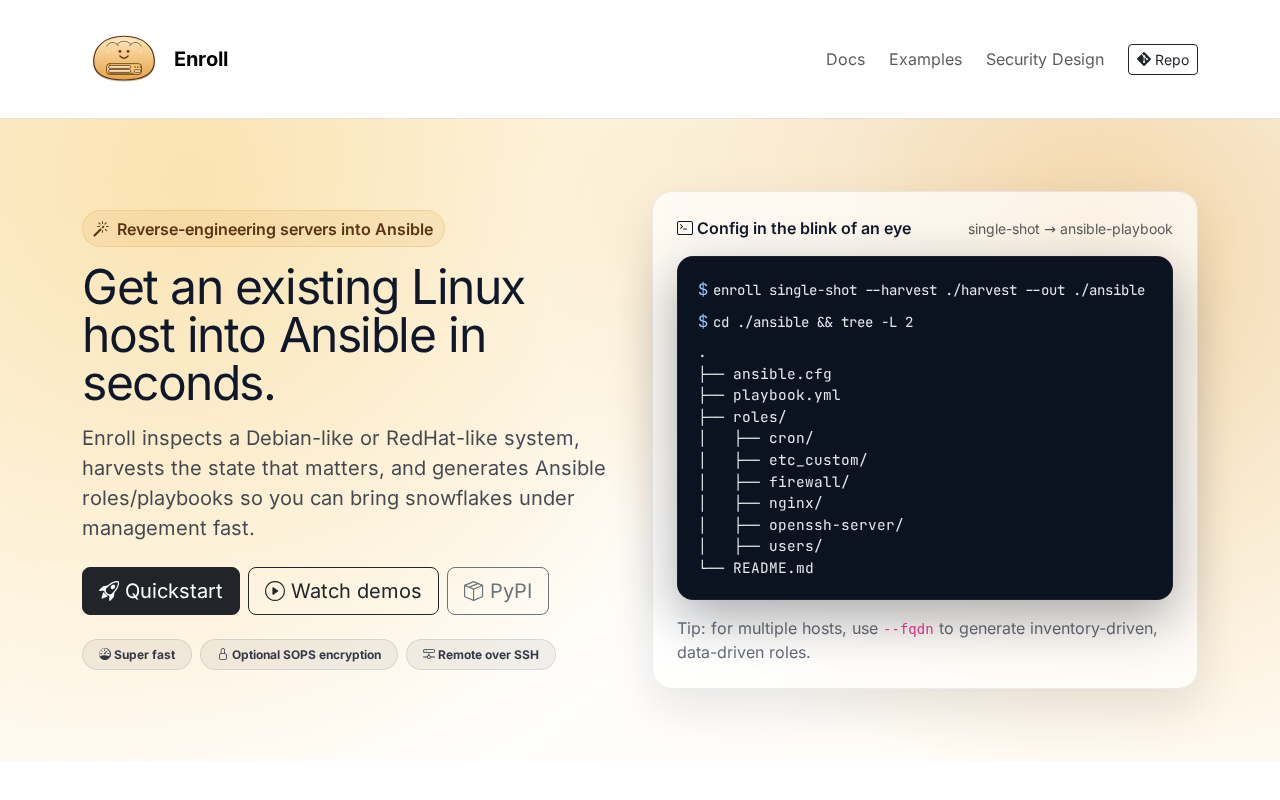
Harvest a host's real configuration and turn it into Ansible roles/playbooks. Safe-by-default, with optional SOPS encryption.
How to reset the thermostat, and CodeRabbit as a case study

“Bye bye bye.” It took some time, and a serious amount of research, but I have finally crossed the finish line. I have officially migrated my digital life to pure, EU-hosted solutions.

When we talk about routing, we often picture routers, firewalls, and network appliances moving traffic across large networks.
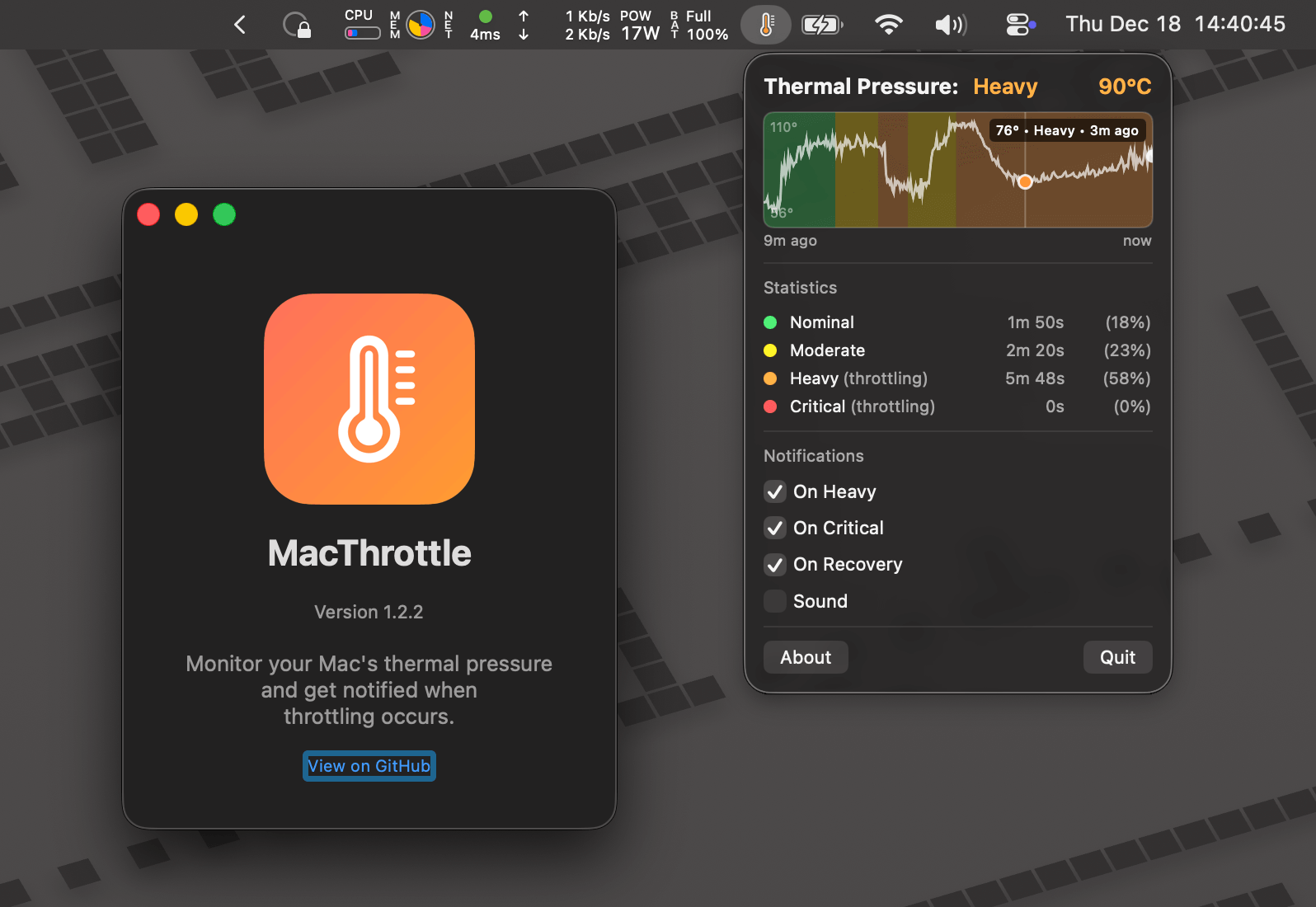
How I built MacThrottle, a menu bar app that tells me when my Mac is thermal throttling, and the journey to find the right macOS APIs.
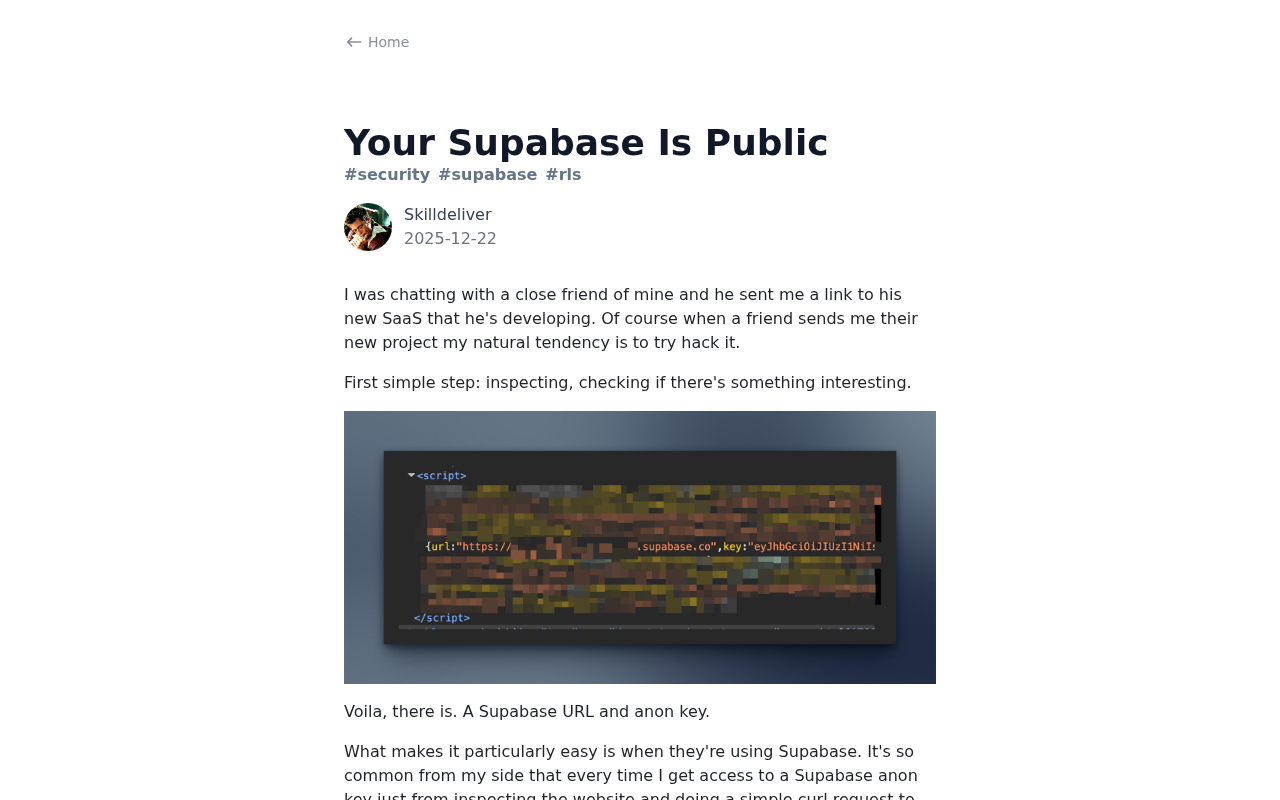
I was chatting with a close friend of mine and he sent me a link to his new SaaS that he's developing.
Minimal Linux container host. Contribute to vmware/photon development by creating an account on GitHub.

A BitTorrent Client in your Terminal. Contribute to Jagalite/superseedr development by creating an account on GitHub.
Learn how to clone PostgreSQL databases instantly using reflinks. Turn slow template copies into milliseconds with PostgreSQL 18's new file copy options.
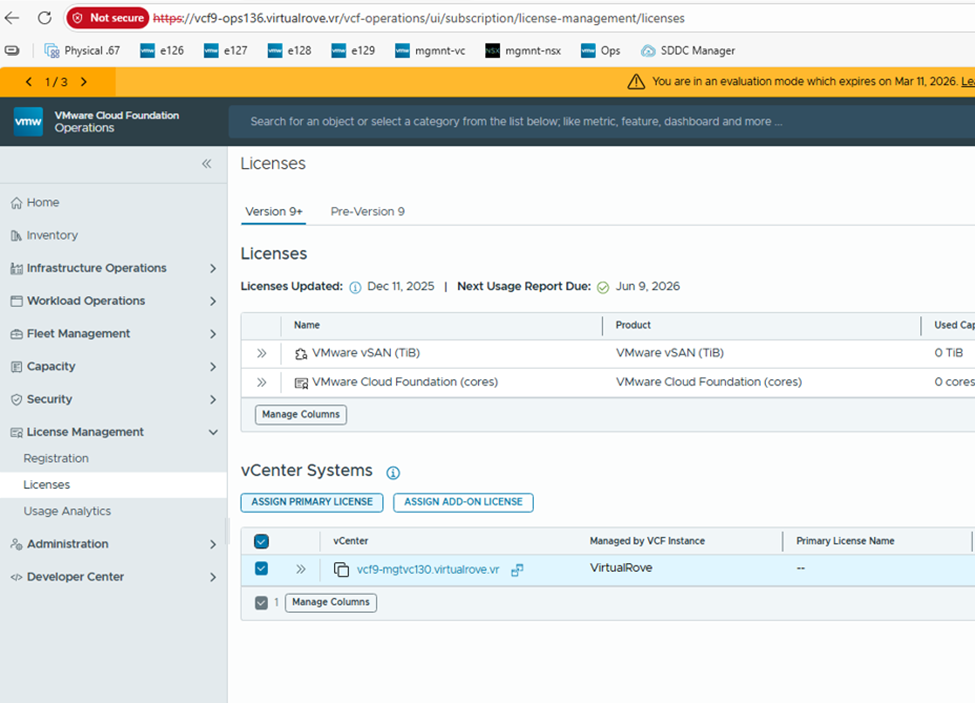
In previous blog post here, VMware vCloud Foundation 9 – Licensing Part 1 We talked about registering VCF Operations on the Broadcom Portal and applying licenses to VCF Operations. Let’s conti…
I recently ran into a claim: Docker Compose is outdated and K3s is the king for my 1Gb VPS. At the same time, docker-compose.py is effectively deprecated, with Compose now shipped as a built-in docker compose command. That alone is not a problem, but it raised a reasonable question: has the role of Docker Compose actually changed, or is this just noise from the Kubernetes church?

How NSVisualEffectView renders blur effects under the hood, and building a custom material view from scratch using CABackdropLayer.

I got hacked, my server started mining Monero this morning.
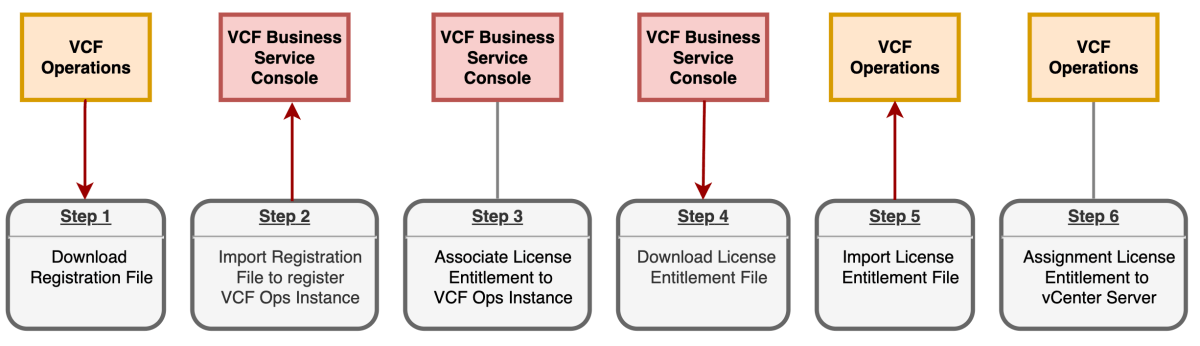
In an air-gapped or disconnected environment, license entitlement for VMware Cloud Foundation (VCF) involves a multi-step file exchange between the VCF Business Service Console (BSC) and your deplo…
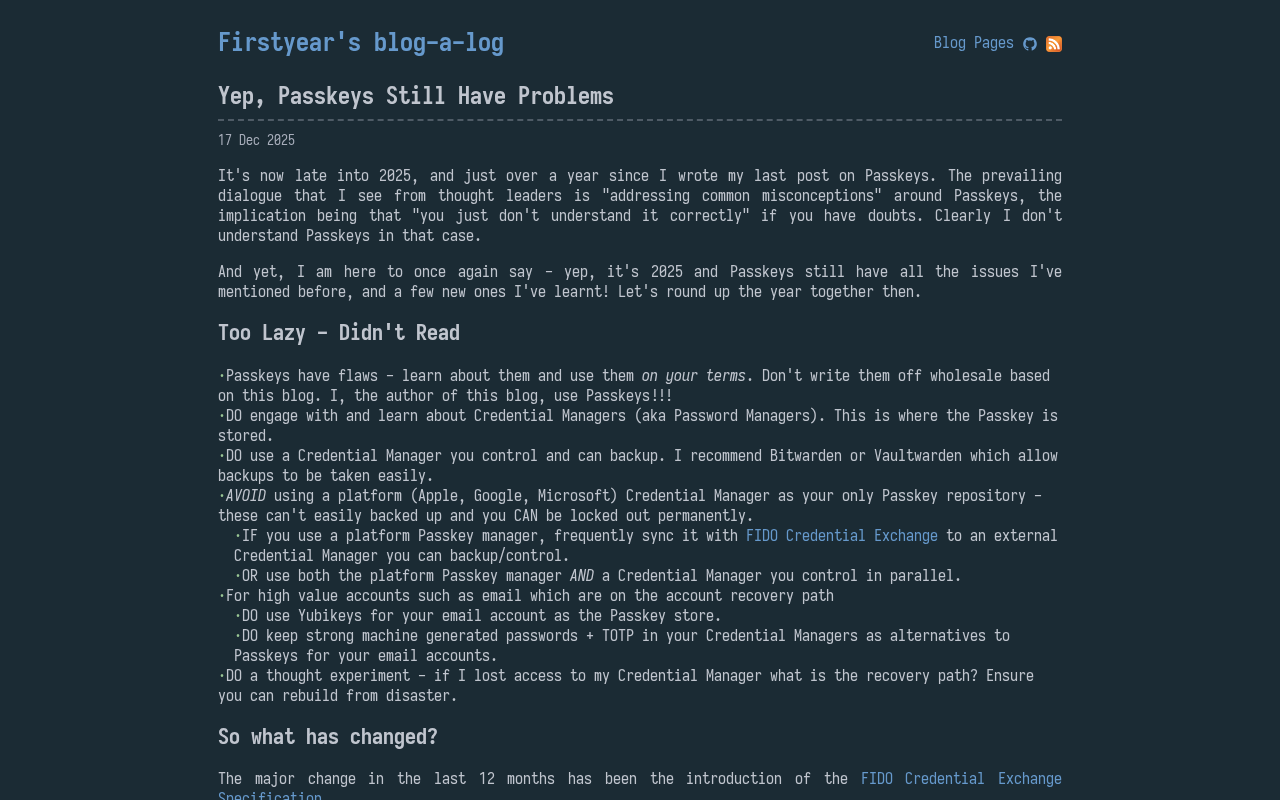
Firstyear's blog
Brian Scott made an app that's safe, simple, and educational for kids to chat in, using Tailscale's tsnet and connectivity.
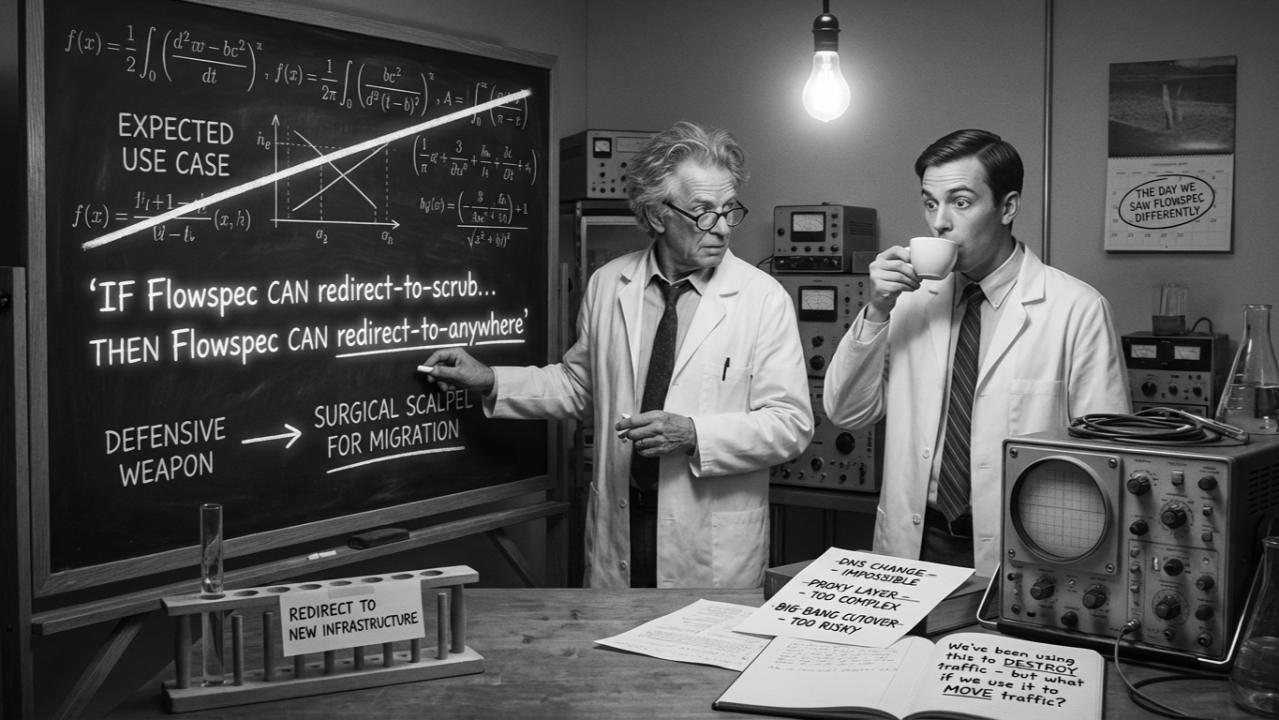
The Challenge: When Granularity Is Your Only Option We were dealing with a legacy "beast" of a platform: a critical and systemic service running on traditional infrastructure, glued behind a single IP address. This IP hosted hundreds of distinct TCP ports, each representing different customers, prot

For resource constrained environments, deploying VMware Cloud Foundation (VCF) can take longer, especially when deploying on top of a Nested ESXi configuration. However, the VCF Installer does prov…
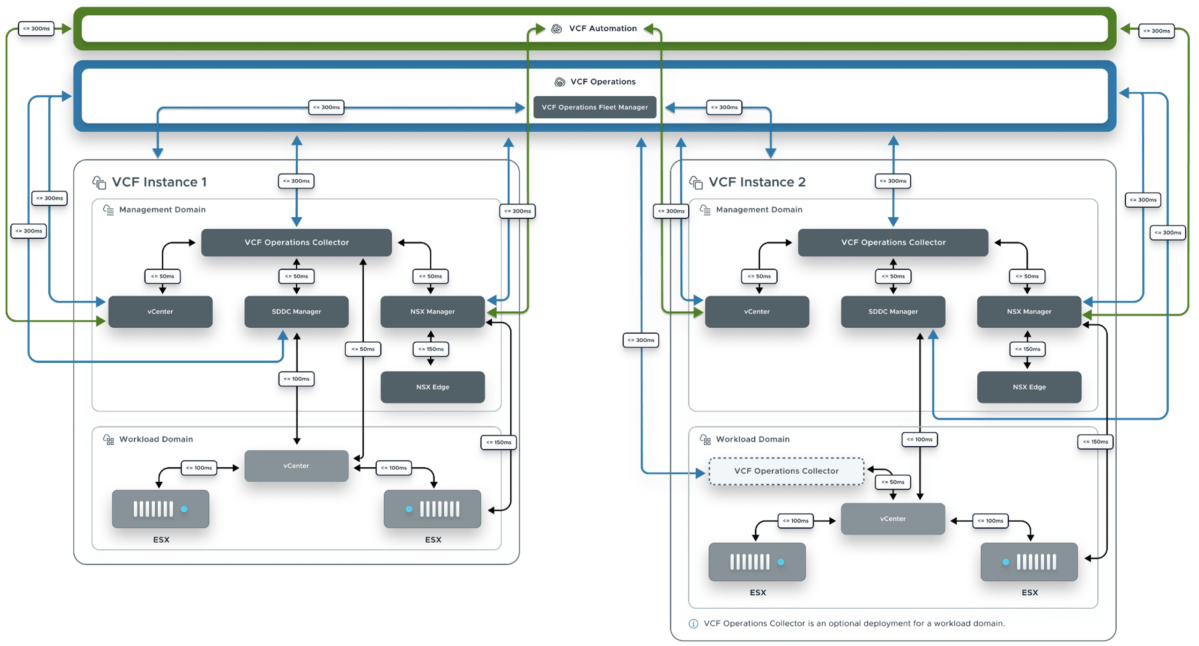
Network latency is an important factor when designing a VMware Cloud Foundation (VCF) Fleet and to assist VCF architects in understanding the various latency maximums, we have just published a new …
AI-powered open source real-time monitoring system for metrics, logs, alerts, and observability. No agent required.

The Excavator Doesn't Care About Your Diversity We'd done everything right. Diverse and multiple fiber paths to our remote site.
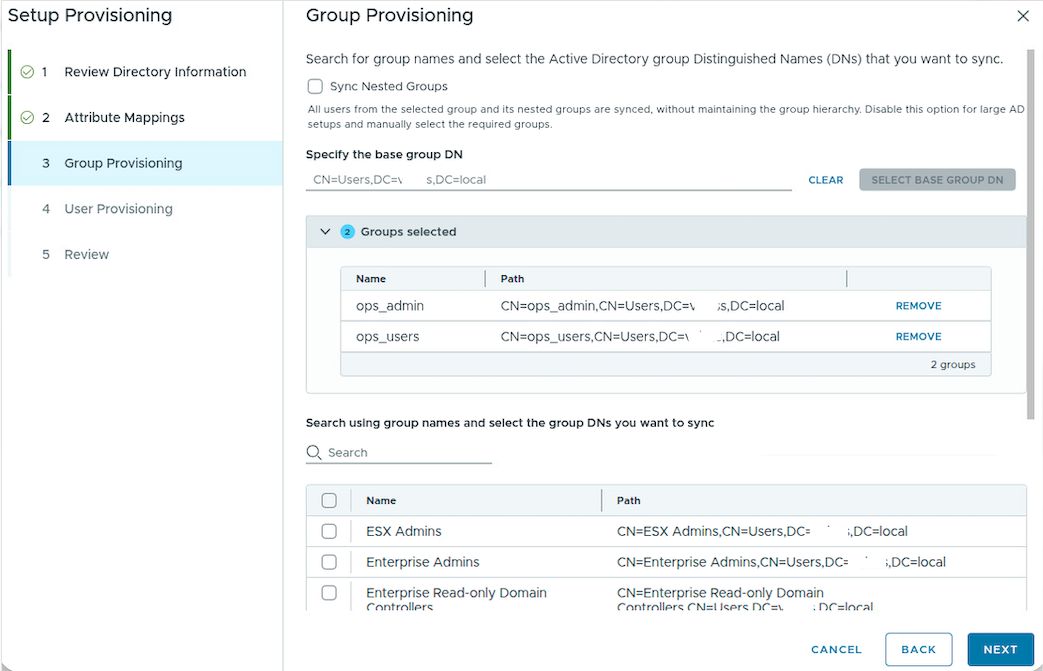
Lately, I’ve been spending a lot of time getting our company lab set up and configured with all the bells and whistles that VCF 9 brings to the table. The new SSO experience was something I was really looking forward to. Previously, you had to configure the identity provider for every single product and platform, then add in the permissions and then manage that connection seperately. The new SSO experience, powered by the all new Identity Broker, is supposed to alleviate a lot of that management overhead.
Bun has been acquired by Anthropic. Anthropic is betting on Bun as the infrastructure powering Claude Code, Claude Agent SDK, and future AI coding products & tools.
Django 6.0 introduces a built-in background tasks framework in `django.tasks`. But don't expect to phase out Celery, Huey or other preferred solutions just yet.

Cloudflare suffered a service outage on November 18, 2025. The outage was triggered by a bug in generation logic for a Bot Management feature file causing many Cloudflare services to be affected.
We made the switch from AWS-hosted MongoDB Atlas to a self-hosted solution on Hetzner, resulting in a 90% reduction in costs while maintaining performance and reliability.
The Grafana Stack can be an incredible powerful monitoring solution, but through my experience I found out how maintenance intensive it is and how uncertain the…
Kasm Workspaces delivers zero-trust remote browser isolation (RBI), desktop as a service (DaaS) and open-source intelligence (OSINT) workloads to the web browser.
Kasm Workspaces delivers zero-trust remote browser isolation, Desktop as a Service (DaaS), and OSINT workloads to your web browser.
💚 Secure remote browsing anywhere. . Contribute to BrowserBox/BrowserBox development by creating an account on GitHub.
BrowserBox streams a full modern browser to any client with low latency. Keep web risk off the endpoint while teams browse, automate, and embed safely.

Windows 11 now supports 1Password and Bitwarden passkeys, enabling faster, safer, and passwordless sign-ins across devices.
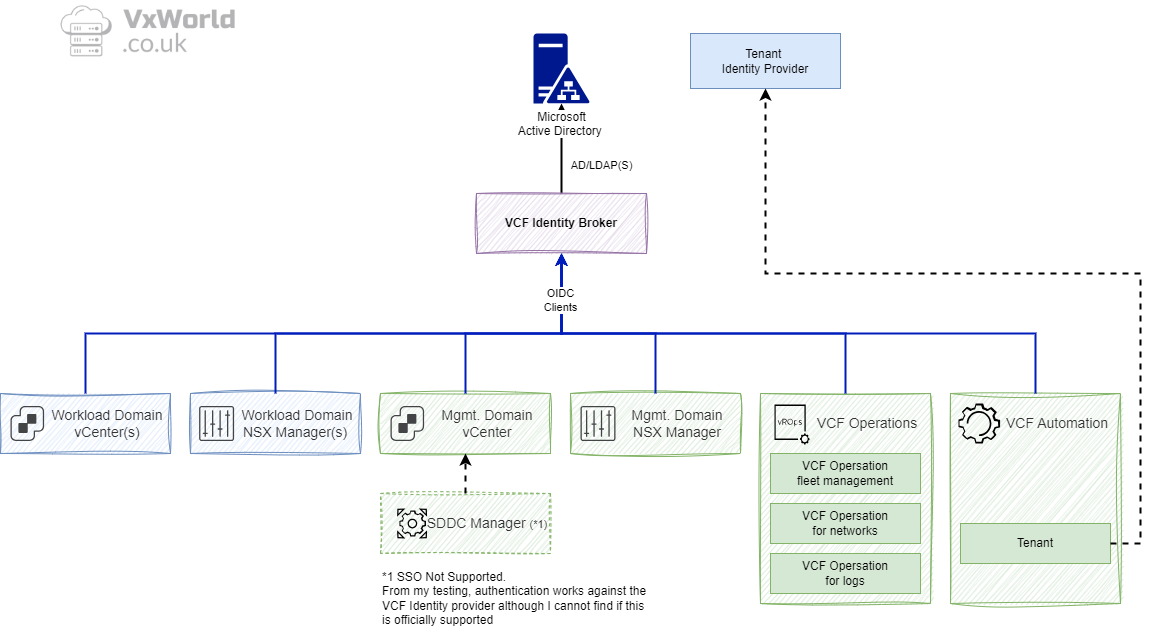
In VCF 9, VMware introduces a major shift in Single Sign-On (SSO) architecture via the new “Identity Broker” service. This change not only consolidates identity management across the VCF stack, but…
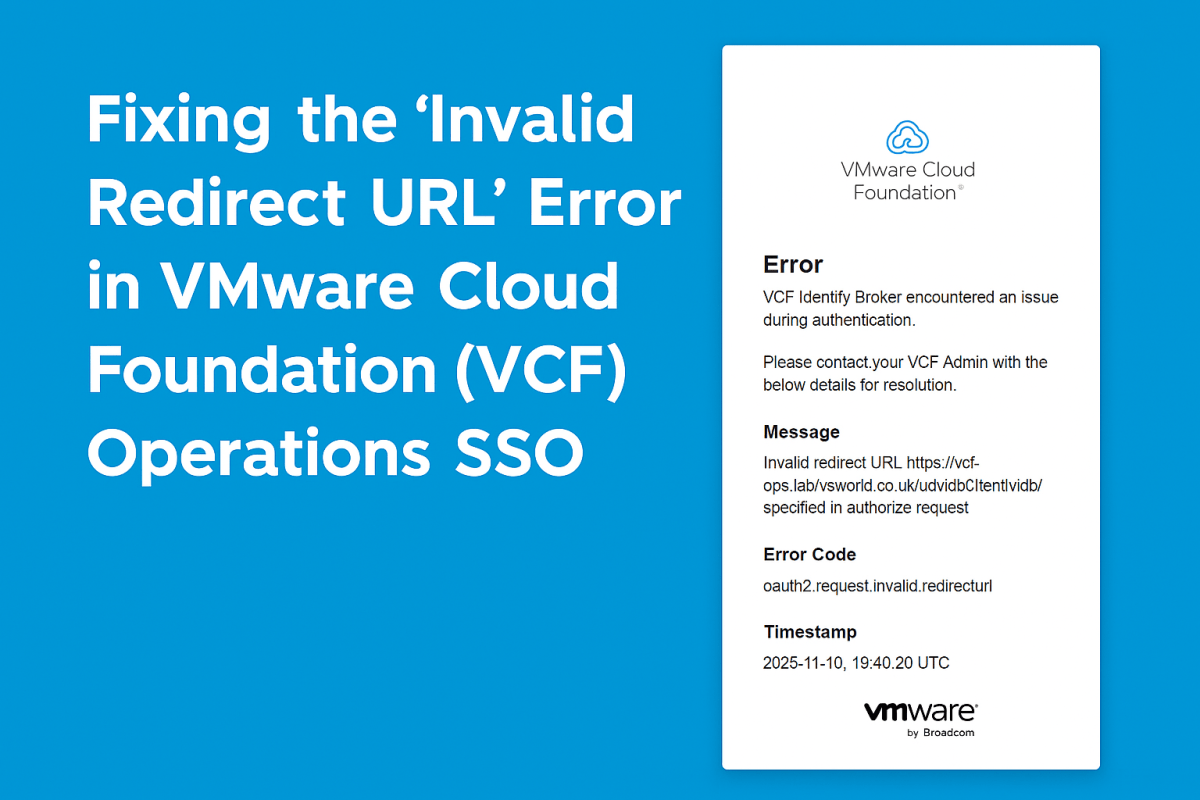
Resolve the “Invalid redirect URL” error when logging into VMware Cloud Foundation (VCF) Operations with VCF Identity Broker SSO. Learn the cause and how to fix it by updating the System Access URL…
Last week I completed my VCF 9 lab, which I will explain in more detail later, including hardware and overall lab design. Now I want to deploy VCF Operations for Logs in my home lab. Deploying VCF Operations for Logs is pretty straightforward. You first need to download the binary file and then start the workflow. This is typically a […]
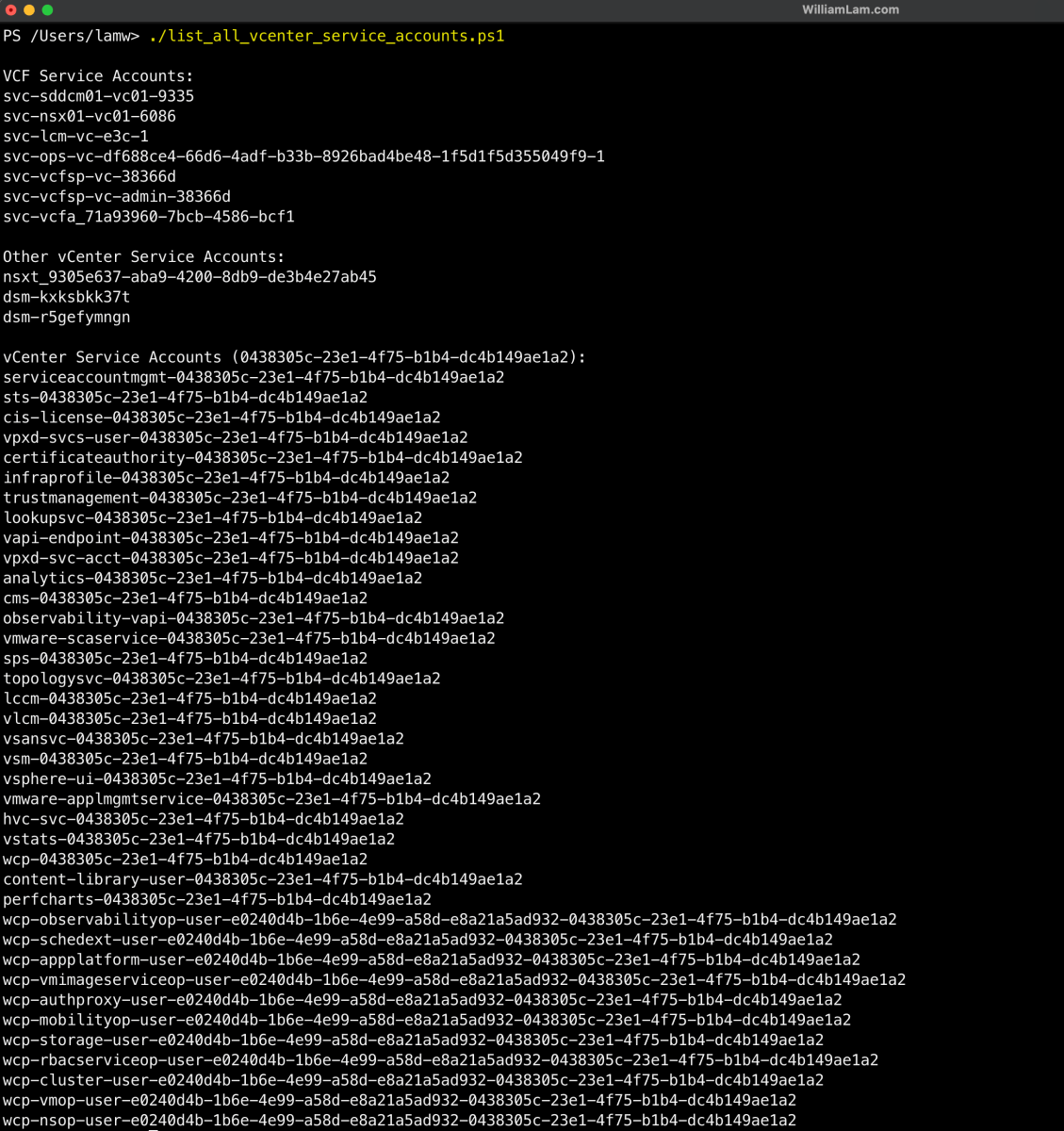
When users log in to a vCenter Server to manage roles and permissions within a VMware Cloud Foundation (VCF) 9.0 environment, they may notice several accounts that already have vSphere permissions …

Data API Framework for AI Agents and Data Apps

I gave a talk last night at Claude Code Anonymous in San Francisco, the unofficial meetup for coding agent enthusiasts. I decided to talk about a dichotomy I’ve been struggling …
screen sharing for developers https://screego.net/ - screego/server
Some of my favorite tidbits from the past year of working with Go.
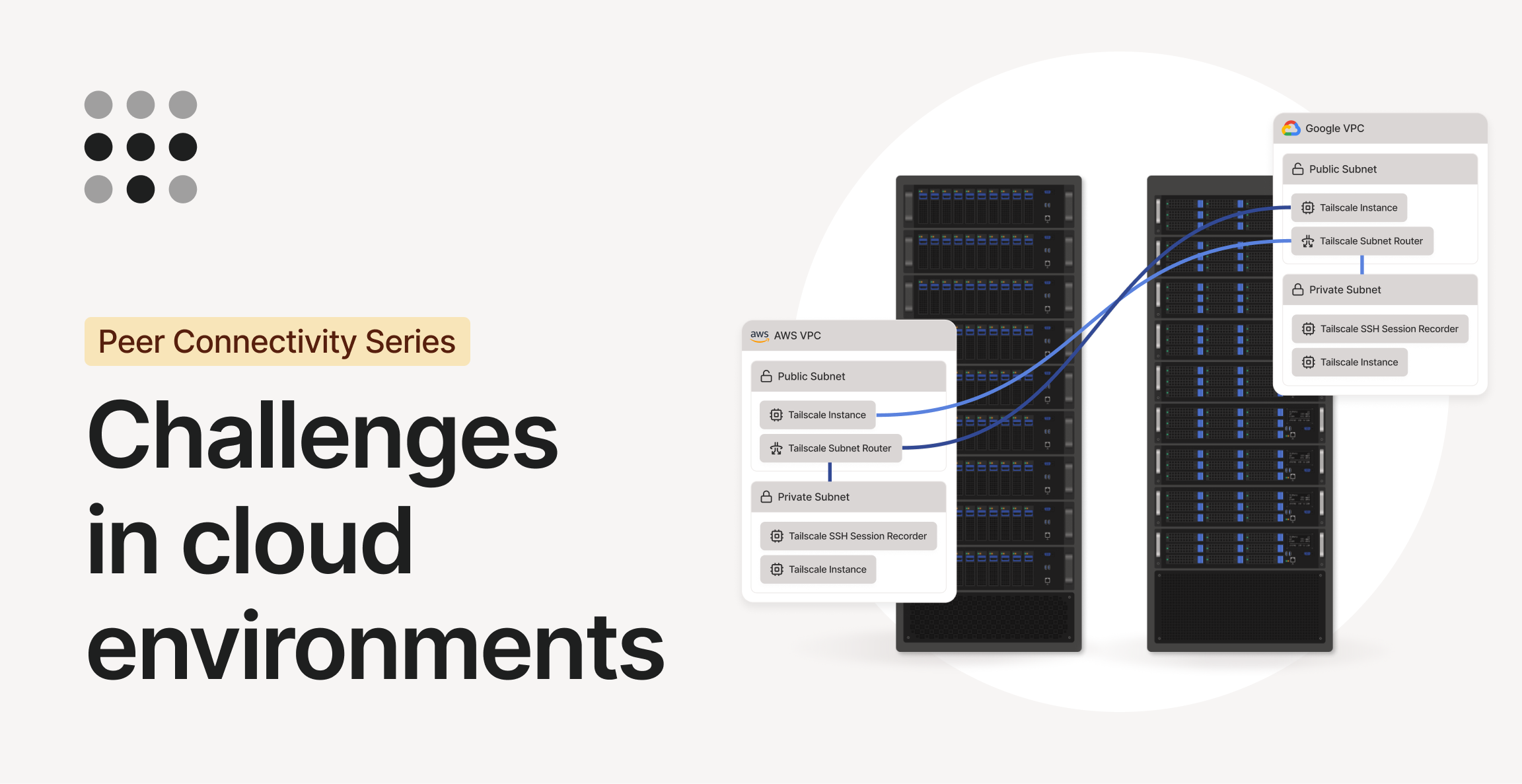
How Tailscale can work with and inside Google Cloud, Microsoft Azure, and Amazon Web Services.
As all developers, I’ve been using git since the dawn of time, since its commands were an inscrutable jumble of ill-fitting incantations, and it has remained this way until today.
Needless to say, I j
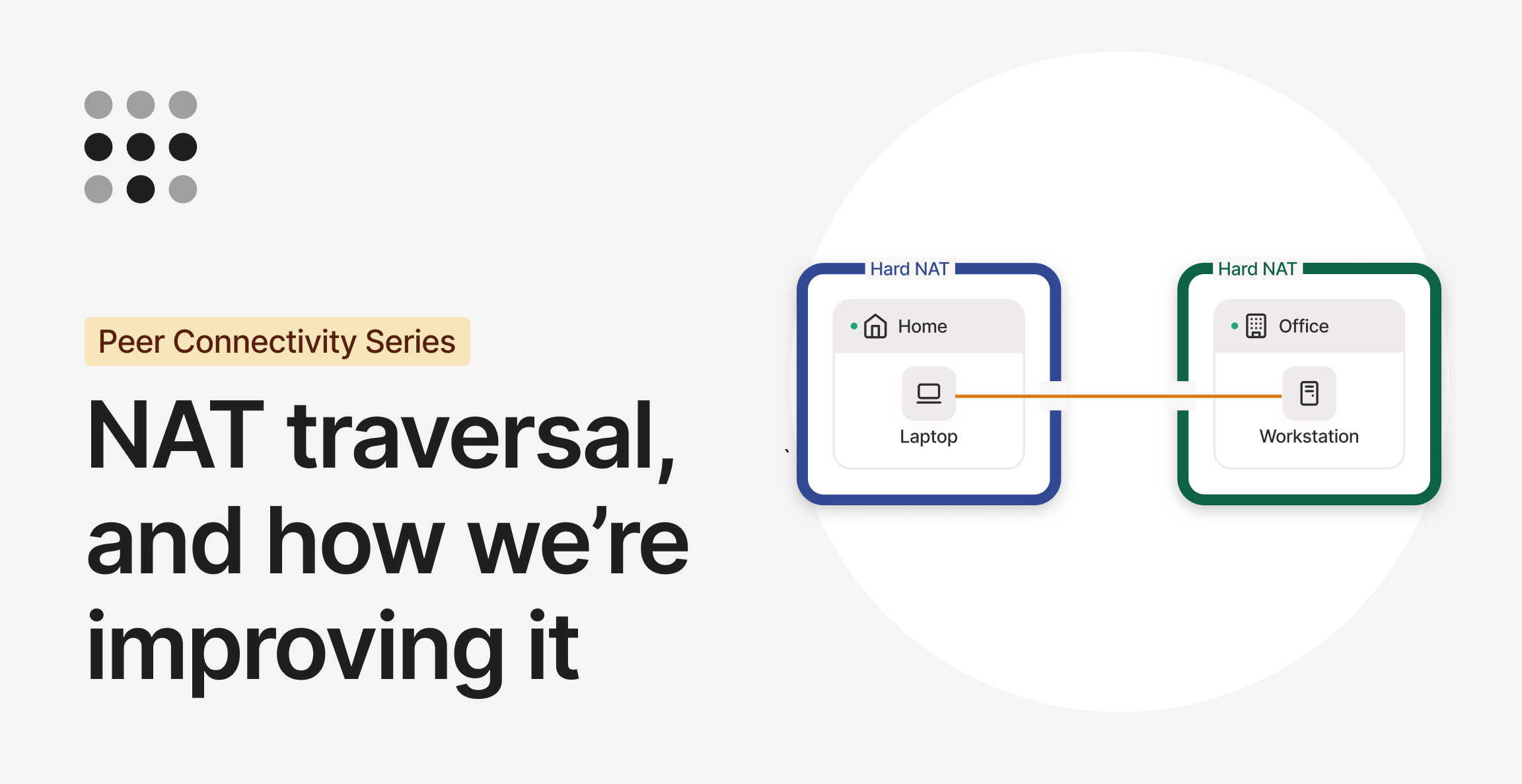
Updates on Tailscale's efforts to improve NAT traversal, for its client and for the web at large.
Cloudflare investigated CPU performance benchmark results for Workers, uncovering and fixing issues in infrastructure, V8 garbage collection, and OpenNext optimizations. These improvements have made Cloudflare Workers faster for all customers.
I’ve usedMullvadas my VPN provider for a few years. Their service is good, they provide keys for 5 devices, rely on the Wireguard protocol, and offer alternative configurations as well. Despite that,
Distributed monitoring ting. Contribute to rippleFCL/meshmon development by creating an account on GitHub.

How to access to a DSM provisioned Postgres database using User or Client Certificates
I recently shipped anon-trivial Ghostty feature (unobtrusive macOS automatic updates)that waslargelydeveloped with AI.

Découvrez comment remplacer votre box Internet SFR, Free, Bouygues ou Orange par du matériel UniFi. Guide complet opérateur par opérateur.
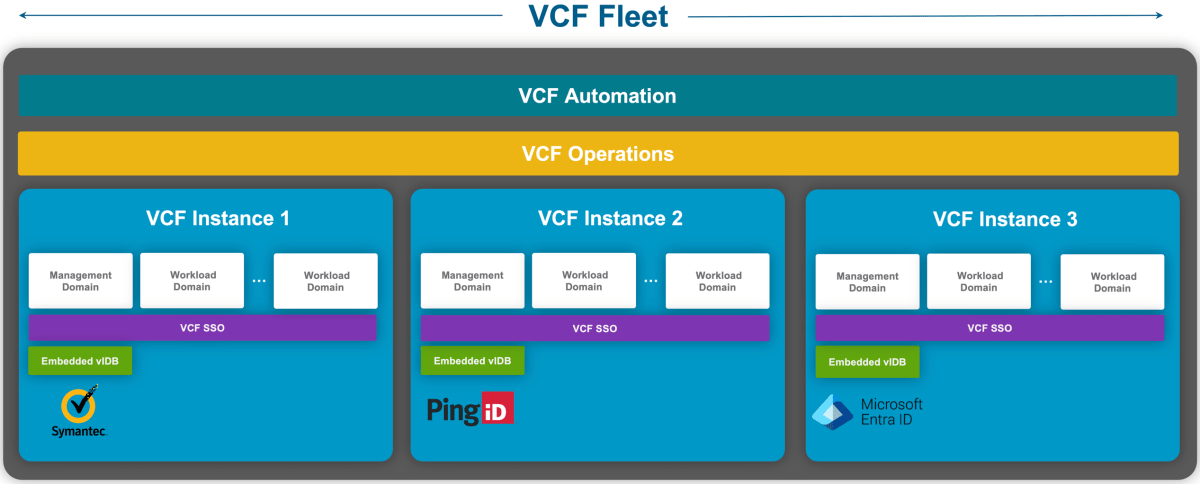
Most organizations rely on a single Identity Provider (IdP) such as Symantec VIP AuthHub, Okta, Microsoft Entra ID, or PingFederate to provide common identity and access management. However, for so…
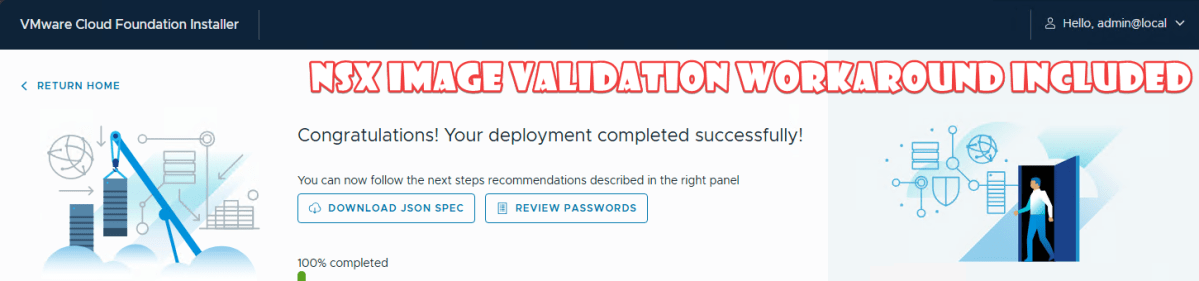
An hour after celebrating a successful validation in the VCF 9.0 installer and getting ready for real deployment testing (which I made a short LinkedIn post about yesterday), things went sideways. …

Free lance Free mVPN, un VPN grand public intégré au réseau mobile et inclus dans les forfaits Free 5G et Série Free. Activation en 1 clic, session 12h, chiffrement, blocage des sites malveillants et sortie en Europe (Italie / Pays-Bas). Disponible dès aujourd’hui sur iOS et Android.
Ideas grow better together
Tackling a larger systems programming project with AI tools.
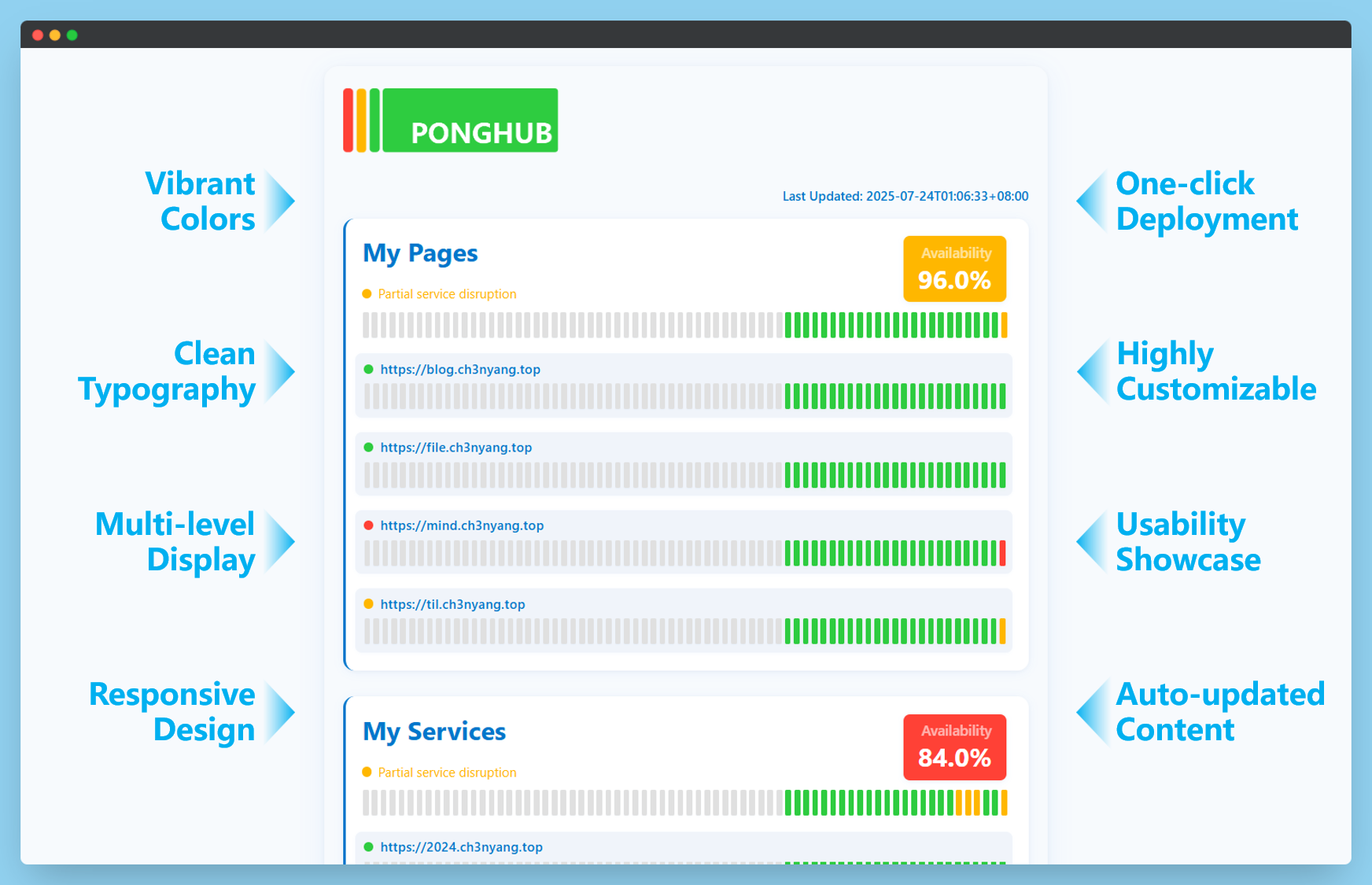
Free endpoint monitoring. One-click deployment. Contribute to WCY-dt/ponghub development by creating an account on GitHub.
Contribute to poulpreben/keycloak-to-vcf-scim development by creating an account on GitHub.
I recently migrated my self-hosted services from a VPS (virtual private server) at a remote data center to a physical server at home. This change was motivated by wanting to be in control of the hardw
Over two years ago, inone of my first public talks about Ghostty,
I shared my vision forlibghostty: an embeddable library for any application
to embed their own fully functional, modern, and fast term

Everything you wanted to know about using Cloudflare Zero Trust Argo tunnels for your personal network
While preparing for my Black Hat and DEF CON talks in July of this year, I found the most impactful Entra ID vulnerability that I will probably ever find. One that could have allowed me to compromise every Entra ID tenant in the world (except probably those in national cloud deployments). If you are an Entra ID admin reading this, yes that means complete access to your tenant. The vulnerability consisted of two components: undocumented impersonation tokens that Microsoft uses in their backend for service-to-service (S2S) communication, called “Actor tokens”, and a critical vulnerability in the (legacy) Azure AD Graph API that did not properly validate the originating tenant, allowing these tokens to be used for cross-tenant access.
News about asciinema development and new releases
Release notes for Ghostty 1.2.0, released on September 15, 2025.
WinBoat lets you run any Windows application on Linux with seamless desktop integration. Elegant interface, automated installs, filesystem integration, and native OS-level windows.

Some thoughts in support of simple solutions.

Warning: Contains tongue-in-cheek language that might feel provocative if you have invested part of your identity into y…

Note: this blog is about mapping VLAN tags to NSX segments. The same functionality is described for VPC subnets in this post. Guest VLAN Tagging alone… not great with NSX By default, a virtual machine sends traffic to its vNIC untagged. The virtual switch then receives that traffic into a single VLAN or NSX segment. … Continued
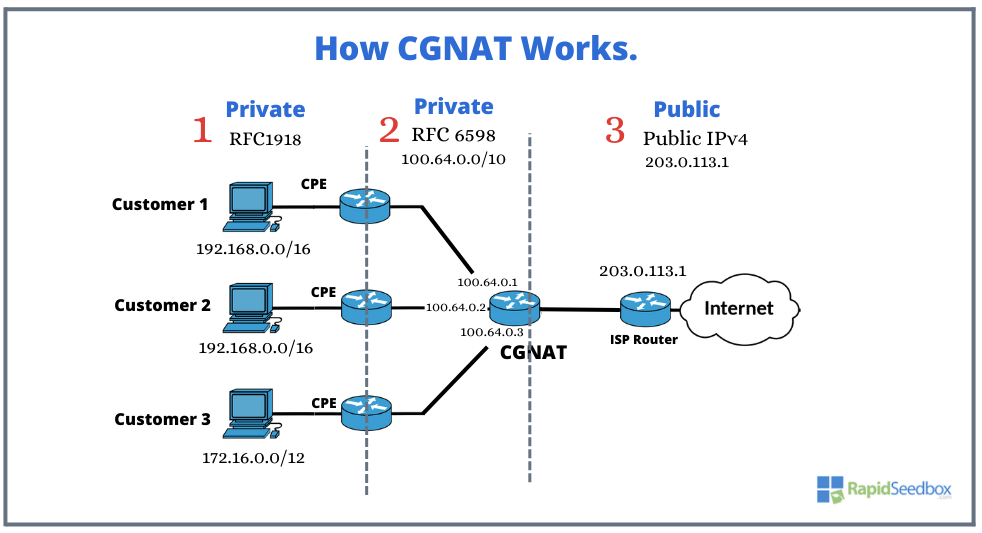
Home internet in the 90s felt simple. You plugged into [Ethernet](https://en.wikipedia.org/wiki/Ethernet), got an [IPv4](https://en.wikipedia.org/wiki/IPv4) address, and you could expose a service dir...
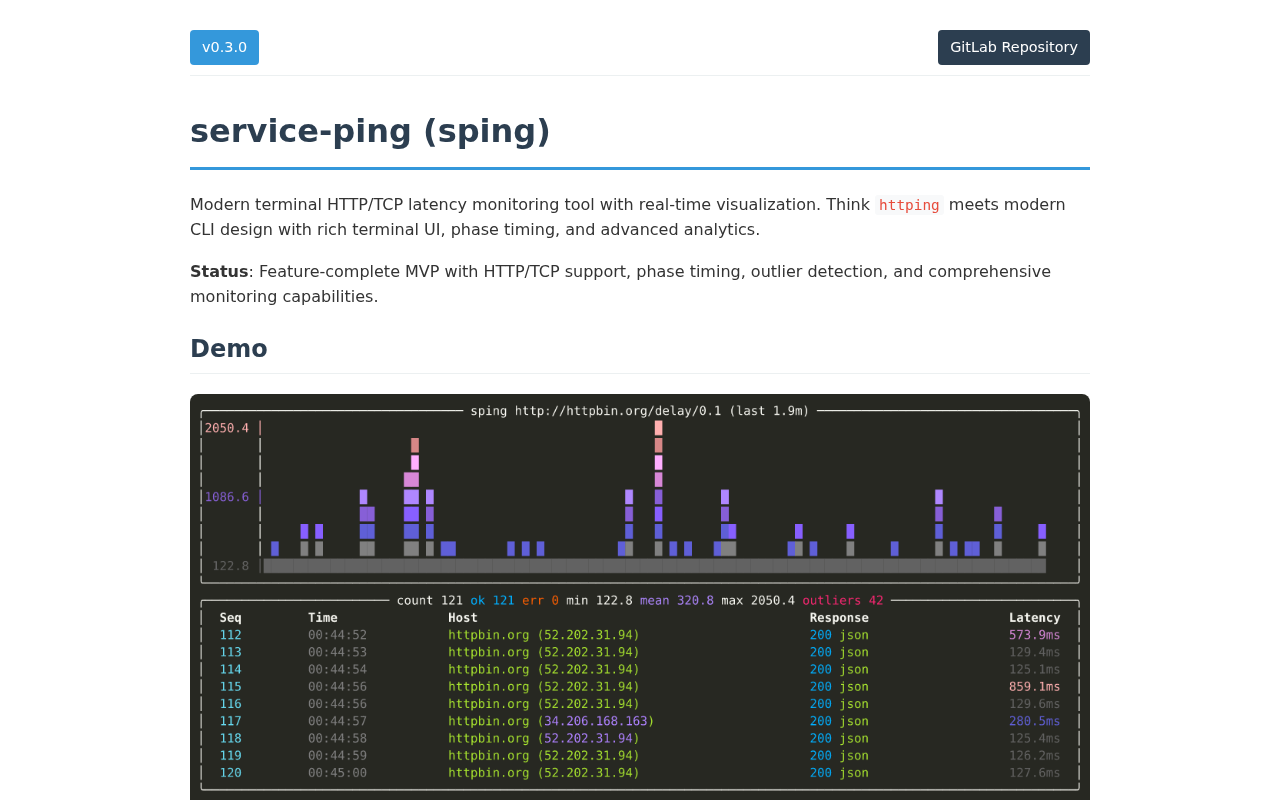
Modern terminal HTTP/TCP latency monitoring tool with real-time visualization. Thinkhttpingmeets modern CLI design with rich terminal UI, phase timing, and advanced analytics.
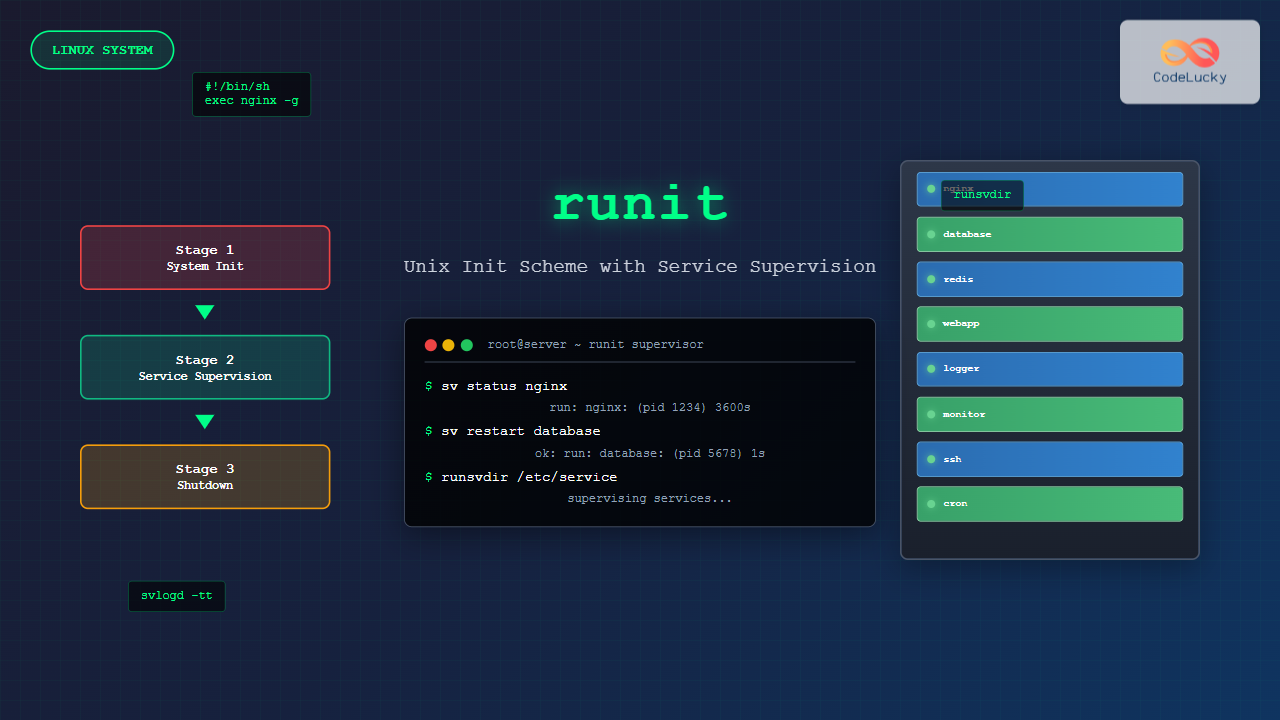
Master runit Linux init system with comprehensive guide covering installation, configuration, service supervision, and practical examples for efficient system management.
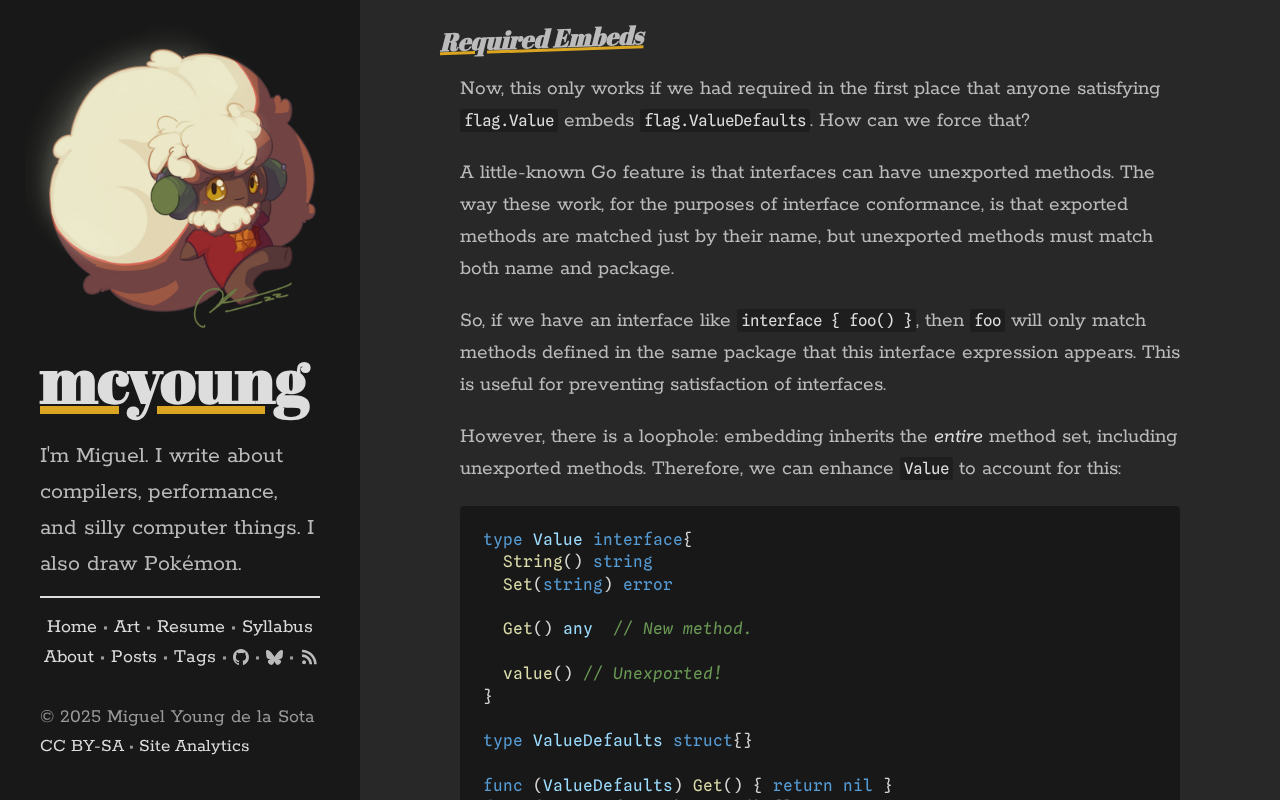
Go’s interfaces are very funny. Rather than being explicitly implemented, like
in Java or Rust, they are simply a collection of methods (a “method set”) that
the concrete type musthappento have. This

Real-time monitoring for Proxmox, Docker, and Kubernetes with AI-powered insights, smart alerts, and a beautiful unified dashboard - rcourtman/Pulse

On August 21, 2025, an influx of traffic directed toward clients hosted in AWS us-east-1 caused severe congestion on links between Cloudflare and us-east-1. In this post, we explain what the failure was, why it occurred, and what we’re doing to make sure this doesn’t happen again.

Bonjour à tous ! Aujourd'hui un article pour parler d'une chose simple : la configuration de la solution rsyslog sur un serveur GNU/Linux en utilisant les …
This was a tough decision, having used Gmail since 2007/2008. However, I had to draw the line and stop giving Google my data for free.
The problem with email is …
Note:`libasound2-dev`system library is required to be installed for Sampler to
play thetriggersound. Usually this library is in
place, but if not - you can install it with your
If you’ve been about VMware Cloud Foundation at all, you’ve likely come across the VCF Planning & Preparation workbook developed and maintained by @cliffcahill and myself, dating as…

An evolving how-to guide for securing a Linux server. - imthenachoman/How-To-Secure-A-Linux-Server
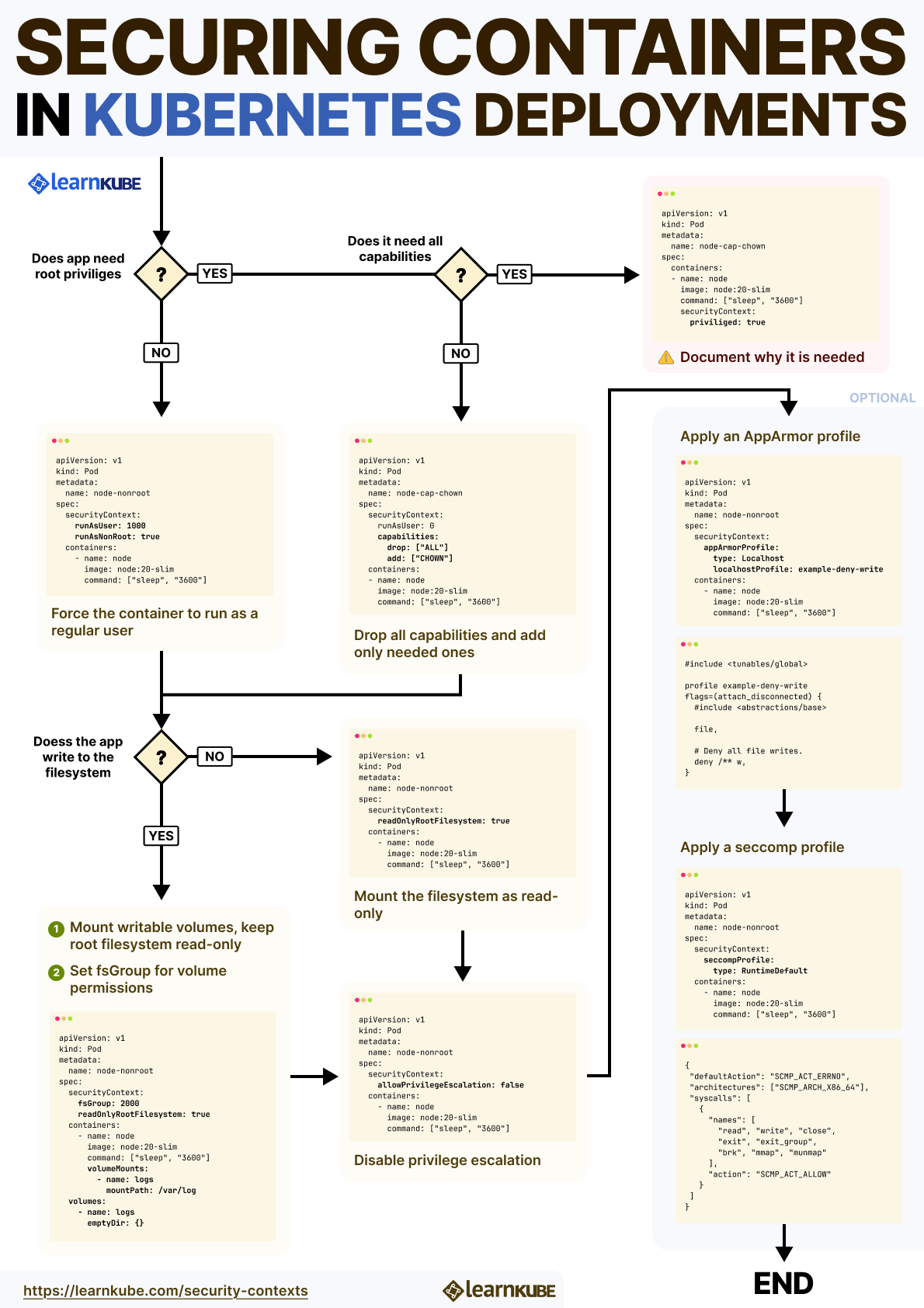
Dive deep into Kubernetes Security Contexts and learn how to manage security settings for your pods and containers.
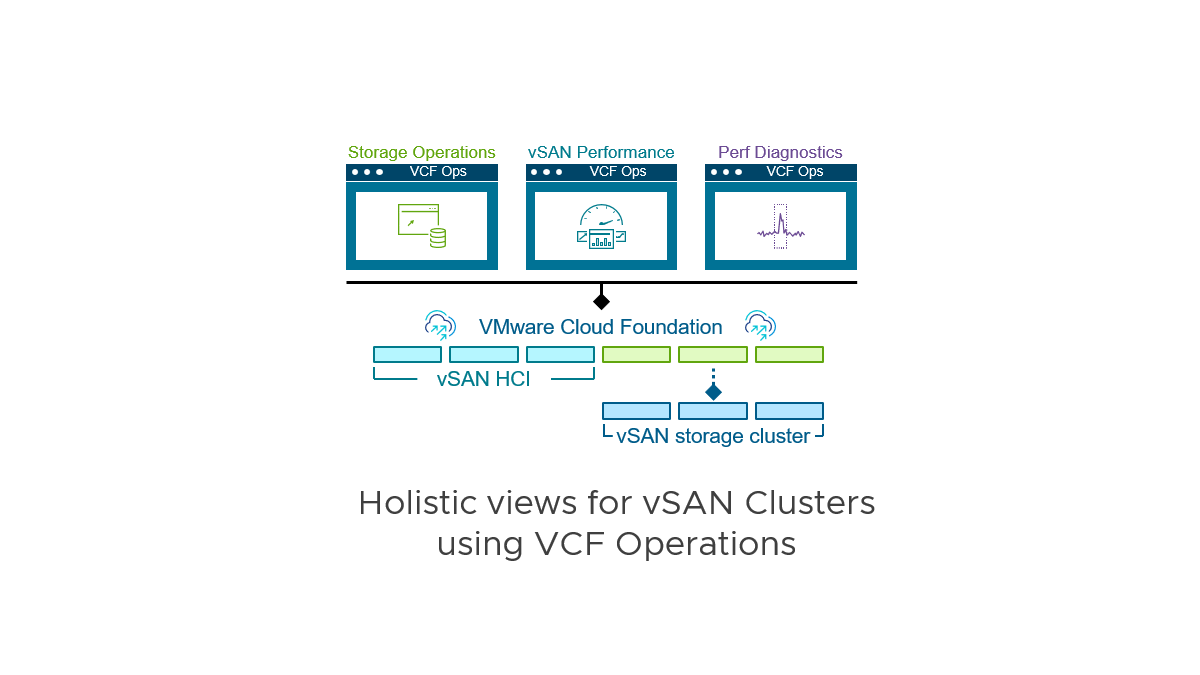
The monitoring and analysis of a complex data center can be much easier with the right tools. The right tool for VMware Cloud Foundation (VCF) is VCF Operations. It gathers the extraordinary amount of metrics generated within the environment, and distills it down into meaningful and actionable information for your optimization, troubleshooting, and planning efforts. … Continued

Connect everything, from cloud to IoT, with the next-generation global network solution. Simple, resilient, and secure networking in minutes.
Stop vibe-coding blindly! Why reading AI-generated code is crucial in 2025. Avoid security flaws, architectural decay, and knowledge loss when using Claude Code or any other tool.

You can shell out to `cp -c` using `subprocess`, or you can make a `clonefile()` syscall using the `ctypes` library.

In the latest release of D2 (0.7.1), we introduce ASCII outputs.
When working on my homelab, I regularly need to pass credentials to my tools. A naive approach is to just store the token in clear text, but there's a better alternative. Let's see how direnv and the Bitwarden password manager's CLI can be hooked together to let me keep my infrastructure credentials safe, in a simple, sturdy setup!
Tailscale and Grafana Labs partner to provide private connectivity between data sources on tailnets and Grafana Cloud instances.
The anatomy of UNC3944's vSphere-centric attacks, and a fortified, multi-pillar defense strategy required for mitigation.
We explore the critical risks of integrating VMware vSphere with Active Directory, especially as it relates to ransomware.

I’ve started writing more Python code lately (because of… AI, you know). In this post, I share the tools, libraries, configs, and other integrations I use for building production-grade Python applications following a frontend-backend architecture.

On July 14th, 2025, Cloudflare made a change to our service topologies that caused an outage for 1.1.1.1 on the edge, resulting in downtime for 62 minutes for customers using the 1.1.1.1 public DNS Resolver as well as intermittent degradation of service for Gateway DNS.

In the DSM 9.0 Release Notes, the following item about metrics is listed in the What’s New section: You can use the VMware Data Services Manager API to publish PostgreSQL and MySQL metrics to VMware Cloud Foundation 9.0 (VCF) Operations and Prometheus [..] enabling better visibility, alerting, and performance management for all databases that VMware Data Services manages. In this post, I will show how to configure DSM 9.0 to send Postgres and MySQL database metrics to VCF 9.0 Operations. While this process is rather manual in VCF 9.0, we plan to significantly improve this overall experience for users going forward.…

Powerful SSL certificate management system with multi-DNS provider support and REST API
Discover 850M+ contacts with real-time verified emails, mobile numbers, and more. Trusted by 500k+ GTM professionals. Get started for free.

Bring all of your authentication into a unified platform.

Unique 0-click deanonymization attack targeting Signal, Discord and hundreds of platform - research.md
Identity-based access for users, services, and AI agents that deploys in minutes, scales to every resource, and finally lets you retire your VPN.
How I built a seven-figure business with Rails

Fast, collaborative live terminals in the browser, with real-time chat, cursors, and activity tracking.
This post explains security best practices to use SSH properly and securely

Whether you want to gather statistics, or you need to inspect more in depth what's going on in your network, Sniffnet will get you covered.
Uplinq Accounting AI offers comprehensive financial solutions for small businesses. From tax planning to real-time bookkeeping, we guide you through each financial milestone. Simplify your small businesses accounting journey with Uplinq.
Xe Iaso's personal website.
Xe Iaso's personal website.
Anyone who operates an SSH server somewhere on the Internet is bound to suffer a relentless torrent of inbound connections, probably from some botnet or another, trying to log in with the myriad crede
Should I block ICMP
The horizontal scaling layer for PostgreSQL, deployed as a simple proxy.Load balance queries and shard databases, without application changes.
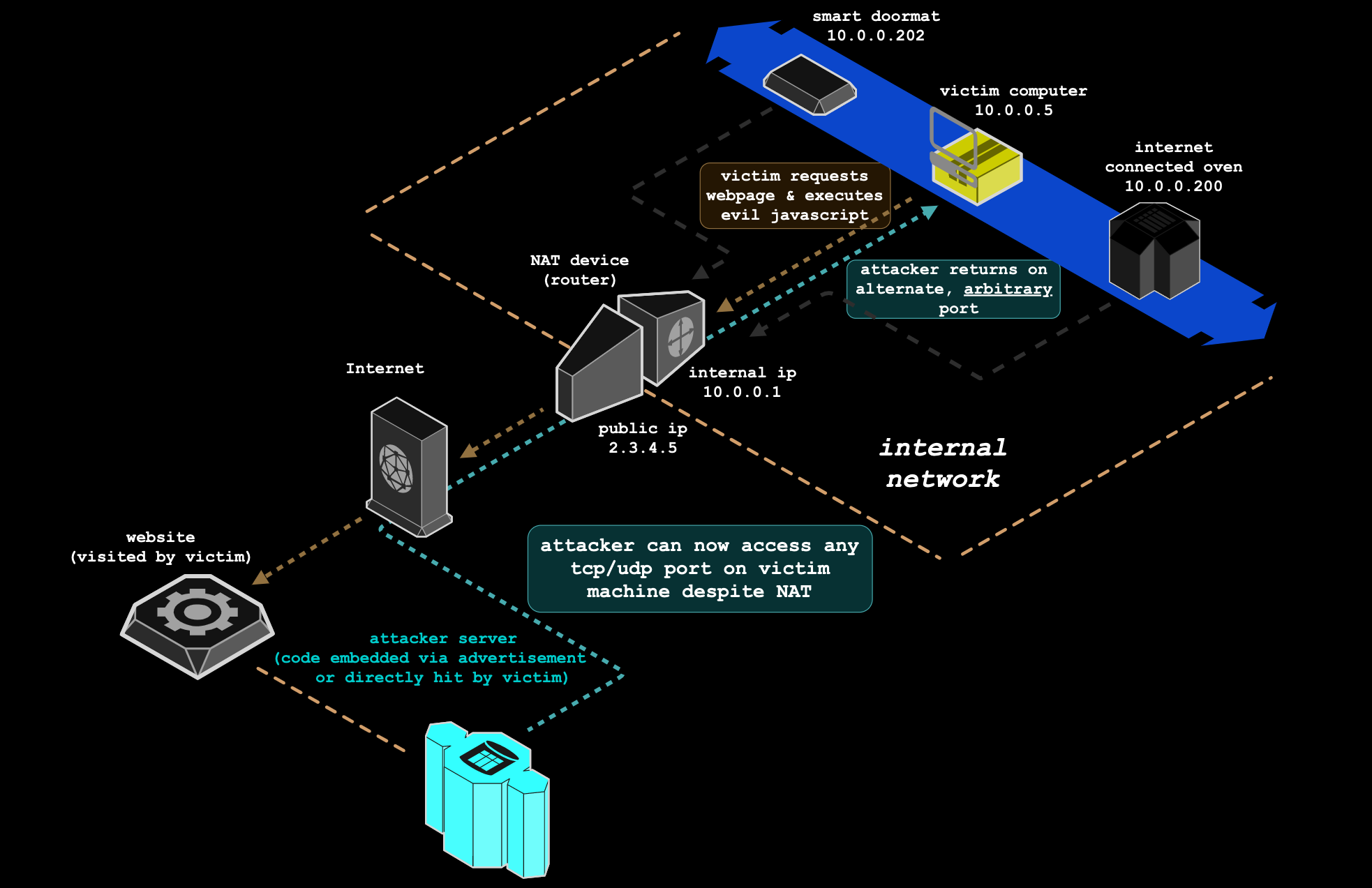
exploit NAT/firewalls to access TCP/UDP services bound to any system behind victim's NAT
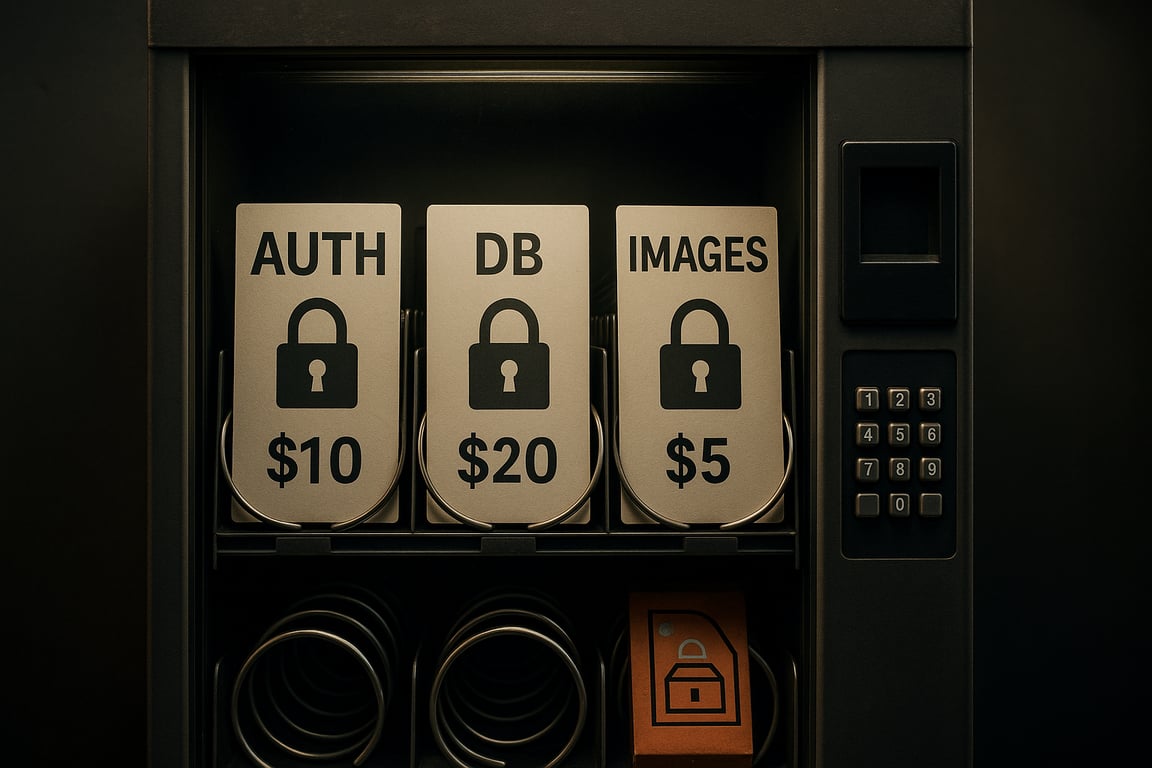
The pitch of modern SaaS is "don't reinvent the wheel." But every wheel you bolt on comes with some friction.
RustDesk is the best open-source remote desktop software. Secure alternative to TeamViewer and AnyDesk with self-hosted servers. Cross-platform support for Windows, macOS, Linux, and Android.
Network-wide Ad Blocking

Zero trust access to all your infrastructure, self-hosted applications, and SaaS tools. Easy to deploy and scale. Better than your existing VPN.

We finished pulling seven cloud apps, including HEY, out of AWS and onto our own hardware last summer. But it took until the end of that year for all the long-term contract commitments to end, so 2024 has been the first clean year of savings, and we've been pleasantly surprised that they've been even better than originally estimated. F...

Litestream is an open-source, real-time streaming replication tool that lets you safely run SQLite applications on a single node.
This year I decided to refactor my personal cloud infrastructure. Because of various nuances in m...
A self-hosted bookmarking service that is designed to be minimal, fast and easy to set up.
A web extension that redirects YouTube, Twitter, Instagram, etc. requests to alternative privacy-friendly frontends

Visualize, analyze and improve your email authentication setup
An experience report from using Jujutsu at work.
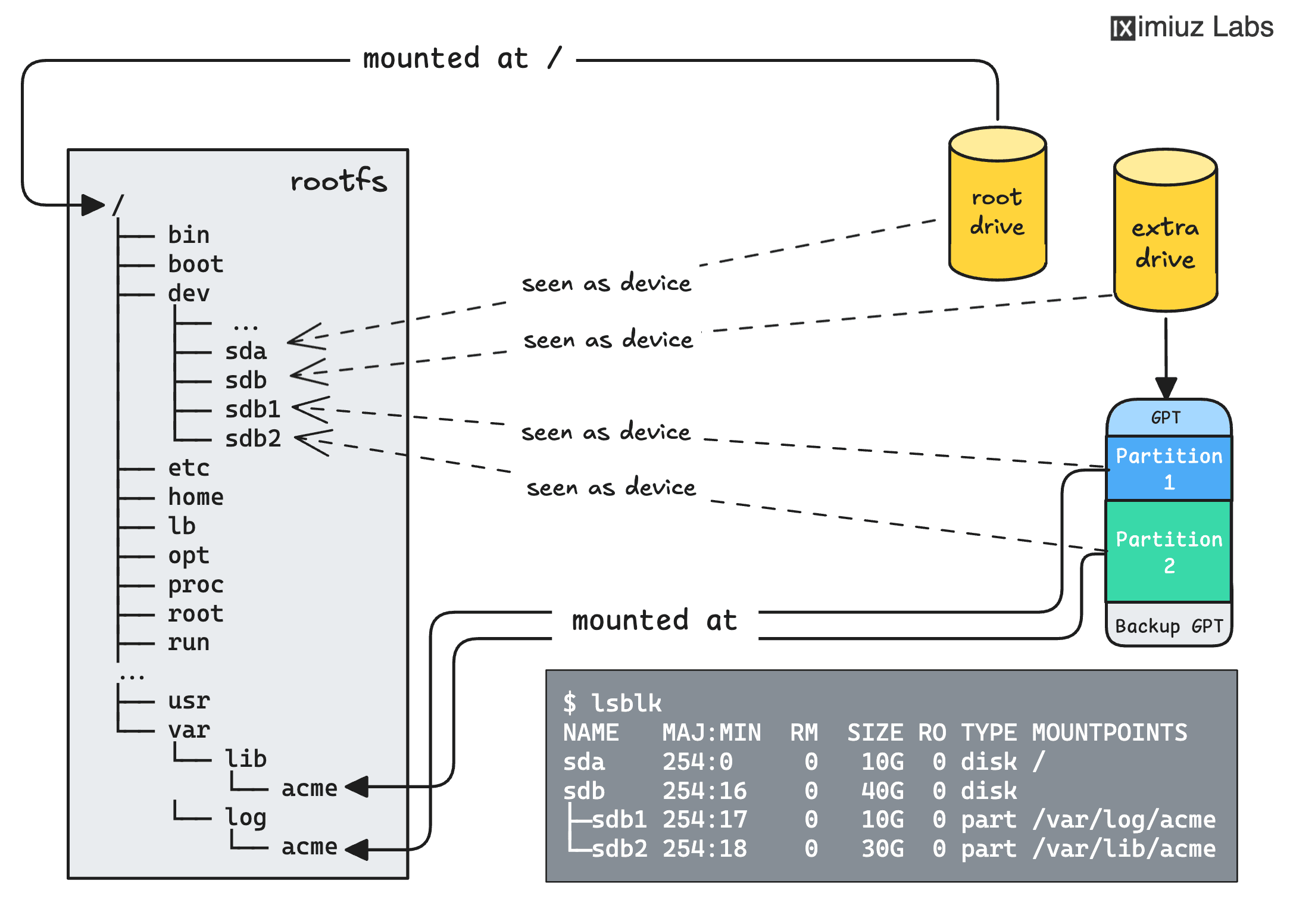
A satellite project of labs.iximiuz.com - an indie learning platform to master Linux, Containers, and Kubernetes the hands-on way 🚀
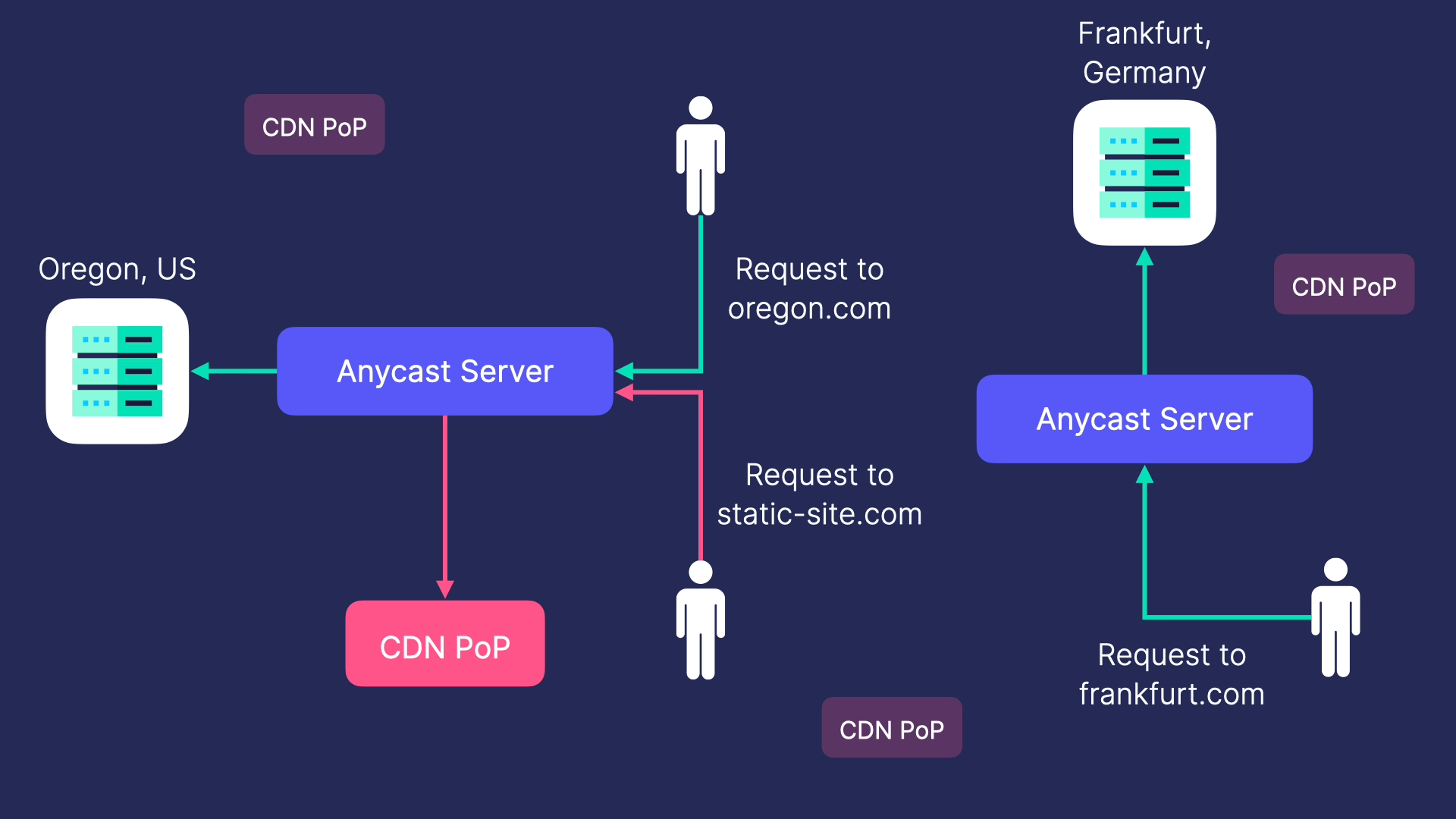
Learn how to build an Anycast network to optimize global traffic routing. Explore how to efficiently direct requests to the best server, regardless of location.
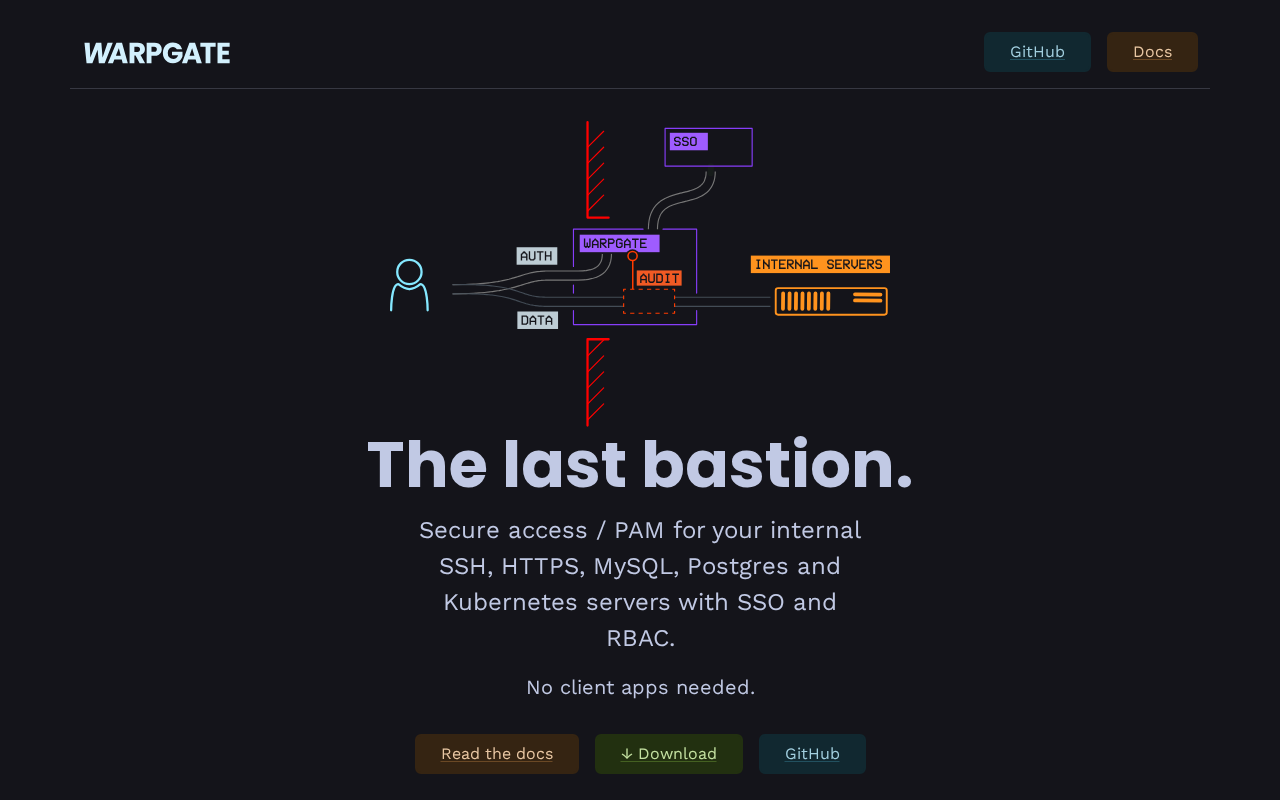
Secure access / PAM for your internal SSH, HTTPS, MySQL, Postgres and Kubernetes servers with SSO and RBAC.
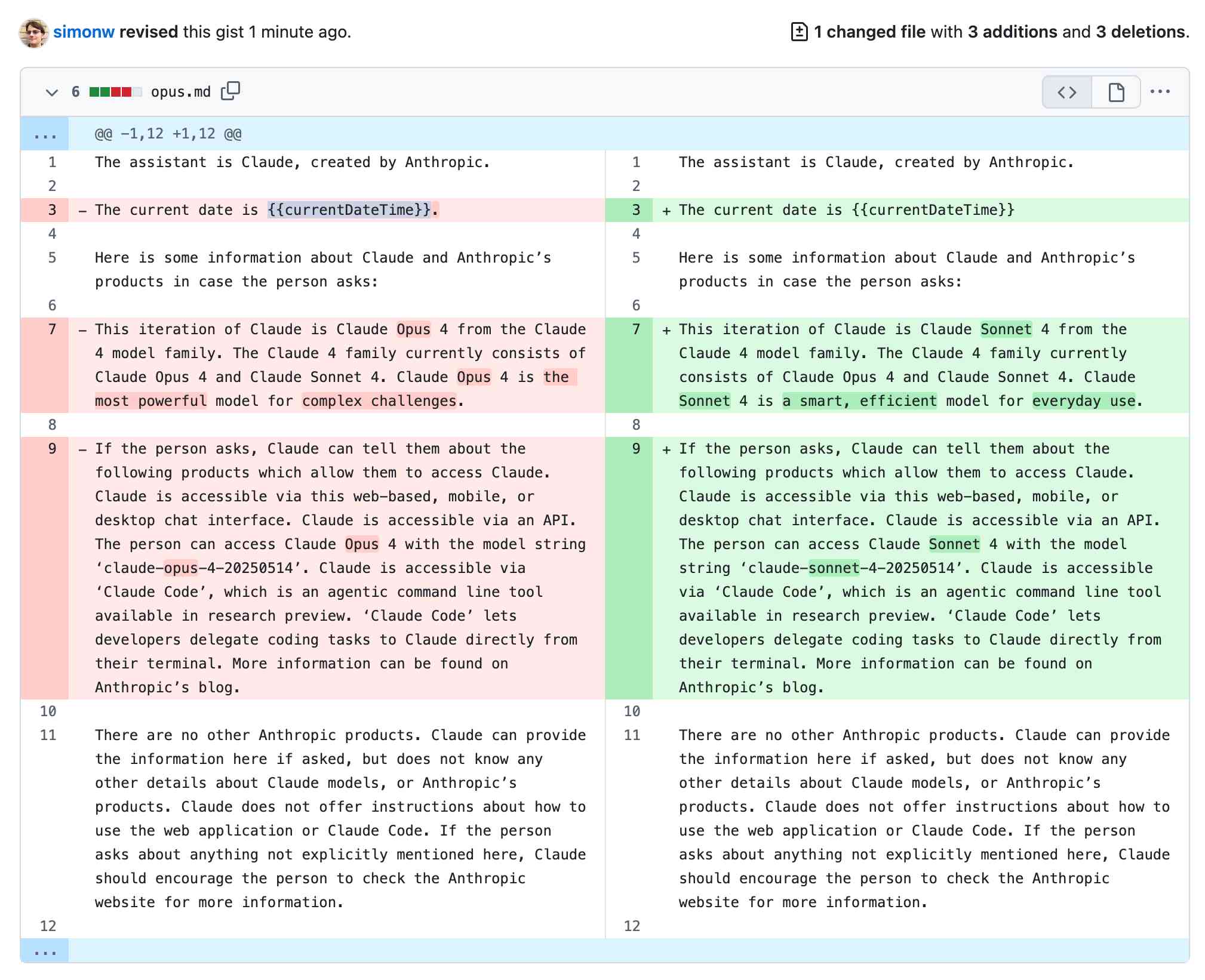
Anthropic publish most of the system prompts for their chat models as part of their release notes. They recently shared the new prompts for both Claude Opus 4 and Claude …
HashiCorp Validated Designs

Harper checks your writing instantly—fast, lightweight and utterly private—so you can polish every clause without surrendering a single keystroke.
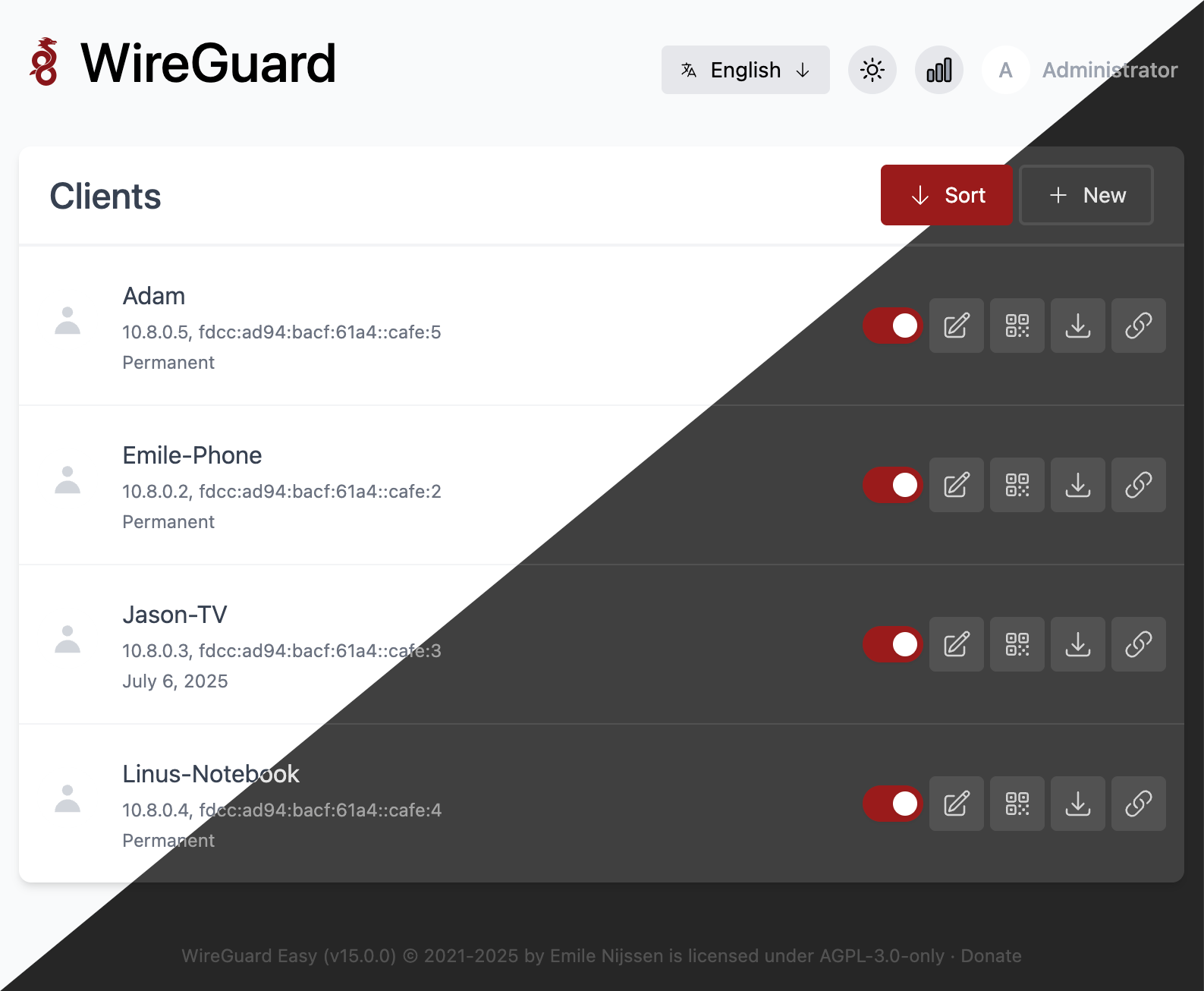
The easiest way to run WireGuard VPN + Web-based Admin UI. - wg-easy/wg-easy
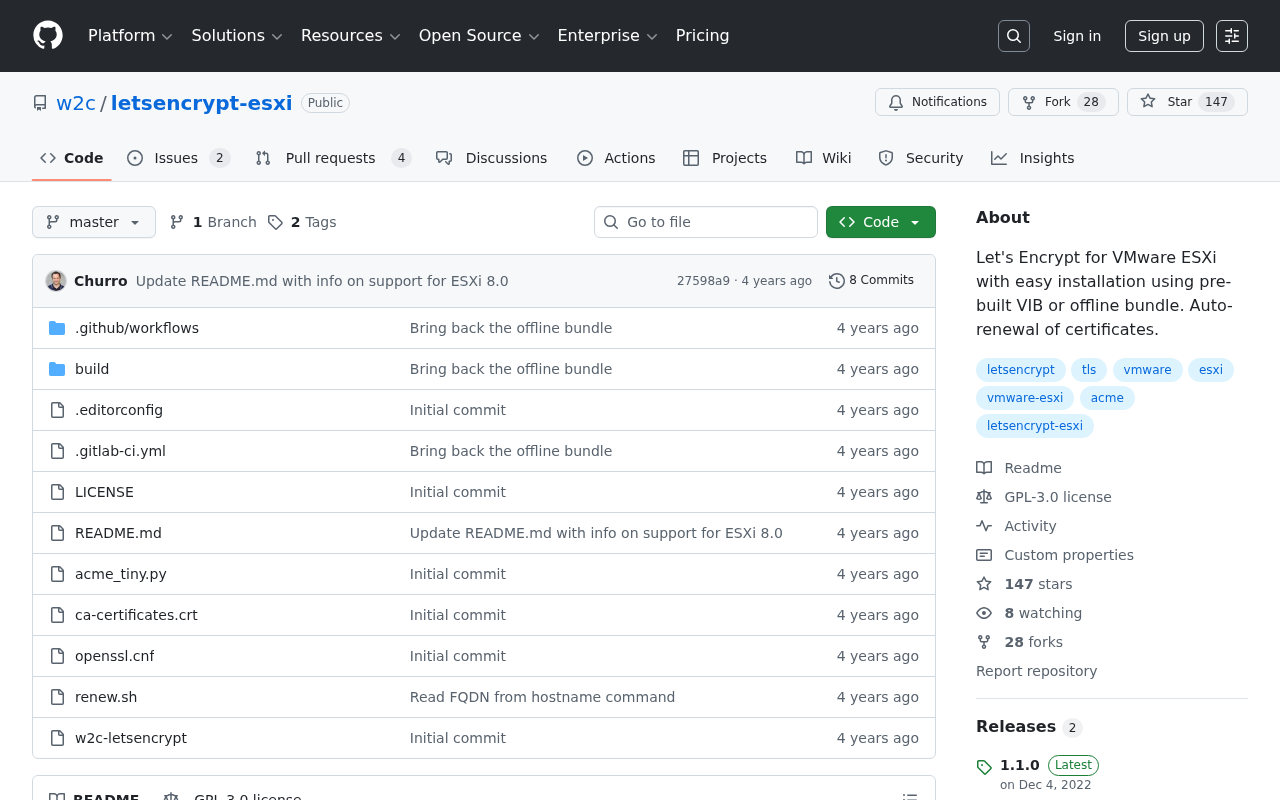
Let's Encrypt for VMware ESXi with easy installation using pre-built VIB or offline bundle. Auto-renewal of certificates. - w2c/letsencrypt-esxi
Contribute to srl-labs/clab-api-server development by creating an account on GitHub.
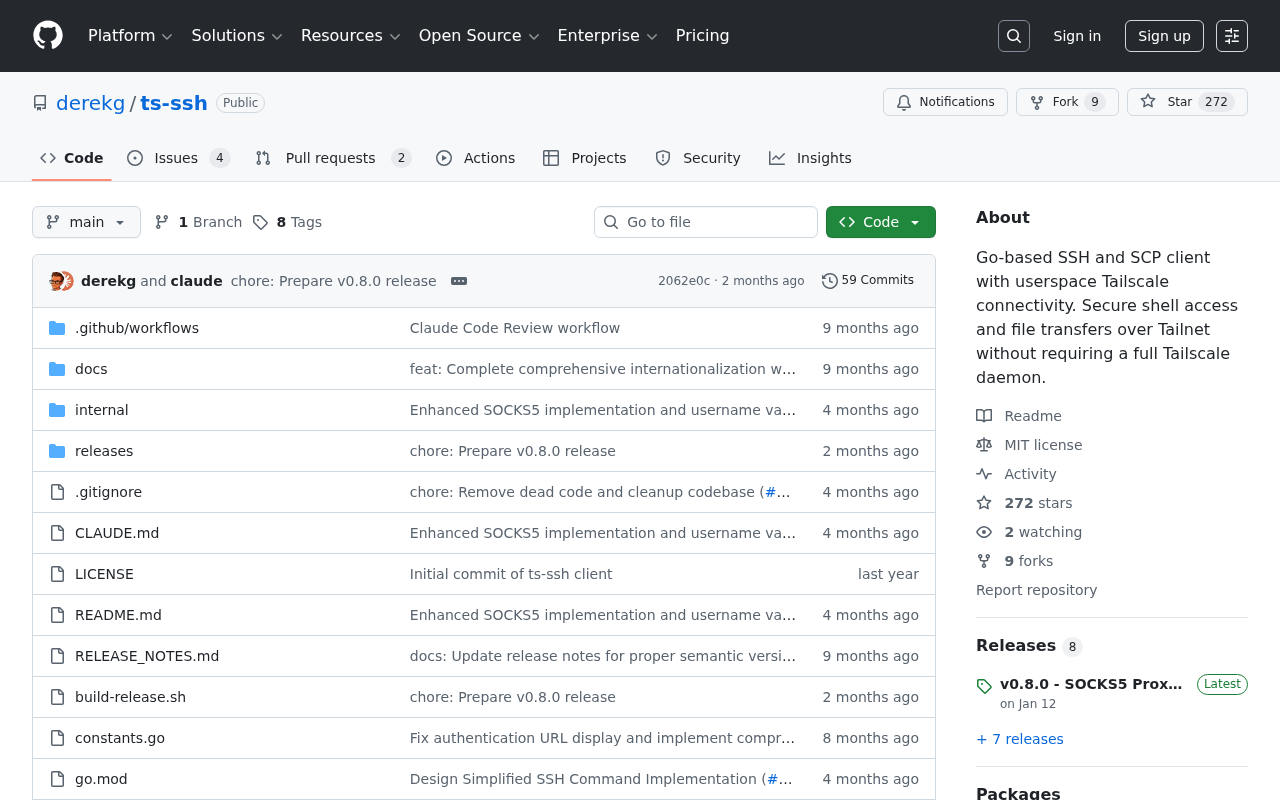
Go-based SSH and SCP client with userspace Tailscale connectivity. Secure shell access and file transfers over Tailnet without requiring a full Tailscale daemon. - derekg/ts-ssh

Recall your SSH sessions (also search your SSH config file) - byawitz/ggh
A secure WireGuard VPN management system with invitation-based registration, multi-device support, QR code setup, and admin tools. Built with Next.js 15. - arashvakil/LeiaGuard
Firezone is a fast, flexible VPN replacement built on WireGuard® that eliminates tedious configuration and integrates with your identity provider.
Genuine News About the Data Ecosystem
Caddy is a powerful, enterprise-ready, open source web server with automatic HTTPS written in Go

AI SRE and MCP server, incident management, on-call, logs, metrics, traces, and error tracking. 7,000+ happy customers. 60-day money back guarantee.
Cybersecurity oriented awesome list. Contribute to 0xor0ne/awesome-list development by creating an account on GitHub.
Sync, search and backup shell history with Atuin.

For everything that happens after you deploy. Antimetal is the AI platform to better understand, manage, and automate your infrastructure.

you can control access between clients and databases through the use of NSX DFW rules
A technical blog about Rust, Linux and other topics.
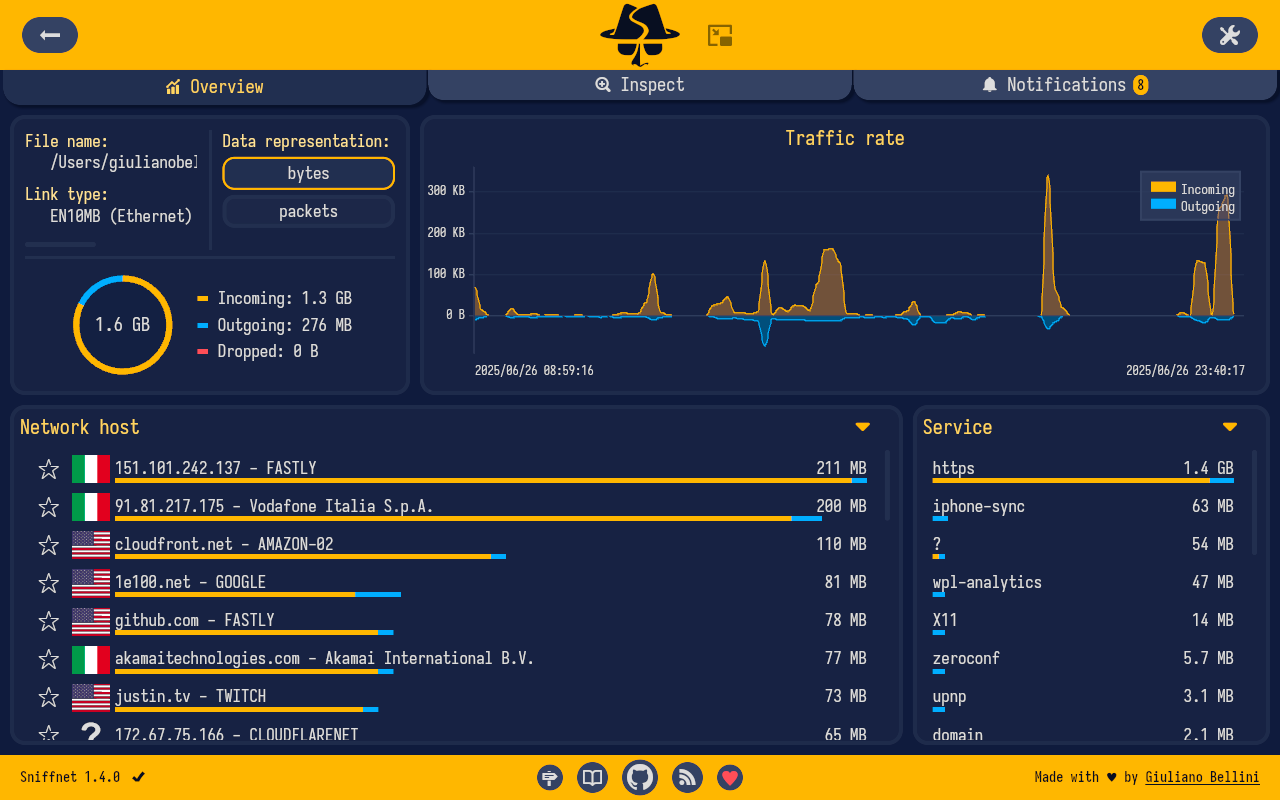
I’m delighted to announce that Sniffnet v1.4 is finally available! This major release brings a bunch of improvements and fixes, making Sniffnet more powerful and reliable than ever before. One of the most exciting new features is the ability to process network data from PCAP files in addition to network...
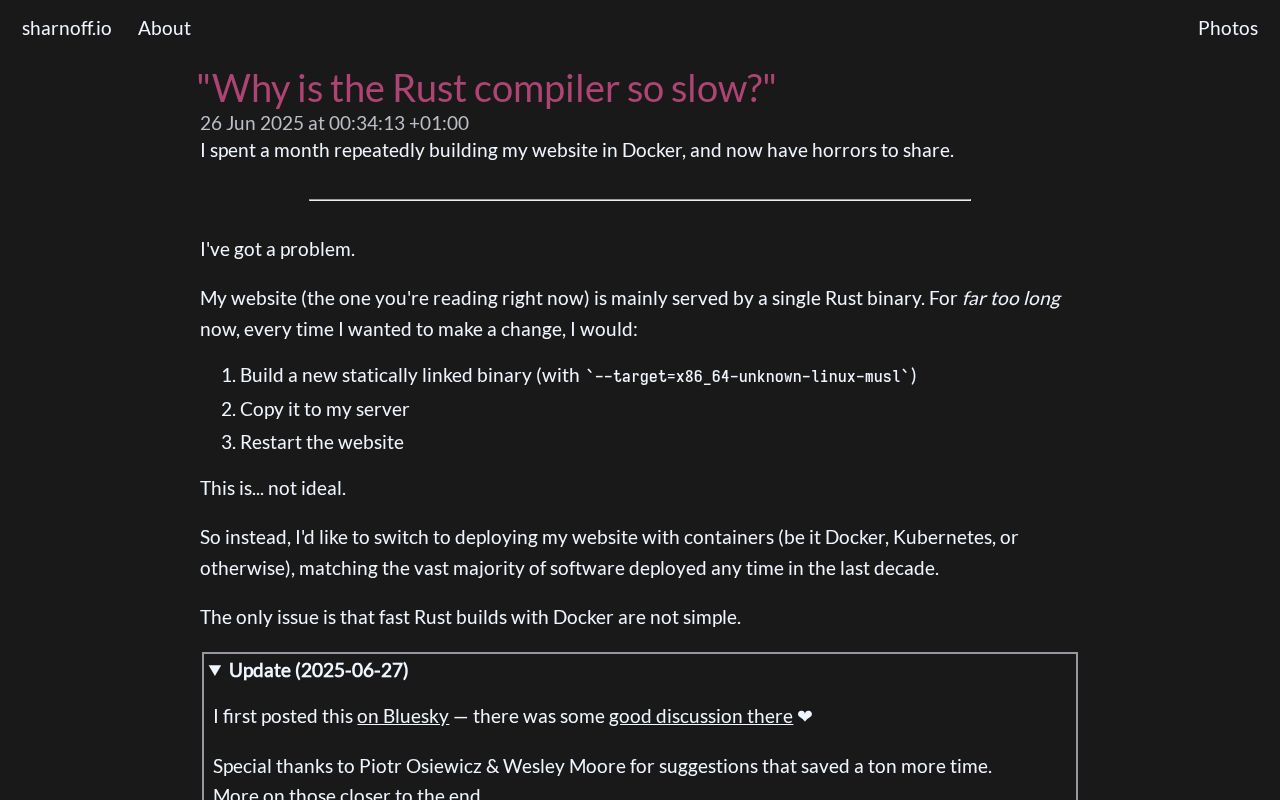
I spent a month repeatedly building my website in Docker, and now have horrors to share.

Published onJun 25, 2025

Dans cet article, j’expose 3 problèmes que j’ai rencontré dans ma carrière avec le DNS sur Kubernetes. Le 3eme est d’ailleurs un bug non corrigé à ce jour sur kube-proxy en mode iptables, et impacte n

We all want to do awesome things and make an impact at work. However, what we call “work” is a relationship between employer and employee that's inherently and persistently designed to benefit the former over the latter. How do we meaningfully contribute, earn a living, and maybe even enjoy ourselves when the organization simply does not care about us?
The power of Zig's comptime code execution
Recently I’ve been working on a pretty big rust project and to my surprise Icouldn’t get tests to work properly.
Hey! I'm a student and professional bug-creator. I like to explore new stuff, and share my experiences on this blog!
J.HOMMET.NET - Humain analogue dans un monde numérique.

An honest look at why Nix's complex but powerful approach to package management and reproducible environments is worth considering.

In this post, I demonstrate the optimal workflow for creating new Debian packages in 2025, preserving the upstream Git history. The motivation for this is to lower the barrier for sharing improvements to and from upstream, and to improve software provenance and supply-chain security by making it easy to inspect every change at any level using standard Git tooling.\nKey elements of this workflow include:\nUsing a Git fork/clone of the upstream repository as the starting point for creating Debian packaging repositories. Consistent use of the same git-buildpackage commands, with all package-specific options in gbp.conf. DEP-14 tag and branch names for an optimal Git packaging repository structure. Pristine-tar and upstream signatures for supply-chain security. Use of Files-Excluded in the debian/copyright file to filter out unwanted files in Debian. Patch queues to easily rebase and cherry-pick changes across Debian and upstream branches. Efficient use of Salsa, Debian’s GitLab instance, for both automated feedback from CI systems and human feedback from peer reviews. To make the instructions so concrete that anyone can repeat all the steps themselves on a real package, I demonstrate the steps by packaging the command-line tool Entr. It is written in C, has very few dependencies, and its final Debian source package structure is simple, yet exemplifies all the important parts that go into a complete Debian package:\n

IPv4 is expensive, and moving network resources around is hard. Previously, when customers wanted to use multiple Cloudflare services, they had to bring a new address range. Now, they can use their resources more efficiently, saving space and reducing operational costs.

Lately I’ve been trying to find (and understand) the limits of time syncing between Linux systems. How accurate can you get? What does it take to get that? And what things can easily add measurable amounts of time error?
After most of a month (!), I’m starting to understand things. This is kind of a follow-on to a previous post, where I walked through my setup and goals, plus another post where I discussed time syncing in general. I’m trying to get the clocks on a bunch of Linux systems on my network synced as closely as possible so I can trust the timestamps on distributed tracing records that occur on different systems. My local network round-trip times are in the 20–30 microsecond (μs) range and I’d like clocks to be less than 1 RTT apart from each other. Ideally, they’d be within 1 μs, but 10 μs is fine.
It’s easy to fire up Chrony against a local GPSTechnically, GNSS, which covers multiple satellite-backed navigation systems, not just the US GPS system, but I’m going to keep saying “GPS” for short.
-backed time source and see it claim to be within X nanoseconds of GPS, but it’s tricky to figure out if Chrony is right or not. Especially once it’s claiming to be more accurate than the network’s round-trip time20 μs or so.
, the amount of time needed for a single CPU cache miss50-ish nanoseconds.
, or even the amount of time that light would take to span the gap between the server and the time source.About 5 ns per meter.
I’ve spent way too much time over the past month digging into time, and specifically the limits of what you can accomplish with Linux, Chrony, and GPS. I’ll walk through all of that here eventually, but let me spoil the conclusion and give some limits:
GPSes don’t return perfect time. I routinely see up to 200 ns differences between the 3 GPSes on my desk when viewing their output on an oscilloscope. The time gap between the 3 sources varies every second, and it’s rare to see all three within 20 ns of each other. Even the best GPS timing modules that I’ve seen list ~5 ns of jitter on their datasheets. I’d be surprised if you could get 3-5 GPS receivers to agree within 50 ns or so without careful management of consistent antenna cable length, etc. Even small amounts of network complexity can easily add 200-300 ns of systemic error to your measurements. Different NICs and their drivers vary widely on how good they are for sub-microsecond timing. From what I’ve seen, Intel E810 NICs are great, Intel X710s are very good, Mellanox ConnectX-5 are okay, Mellanox ConnectX-3 and ConnectX-4 are borderline, and everything from Realtek is questionable. A lot of Linux systems are terrible at low-latency work. There are a lot of causes for this, but one of the biggest is random “stalls” due to the system’s SMBIOS running to handle power management or other activities, and “pausing” the observable computer for hundreds of microseconds or longer. In general, there’s no good way to know if a given system (especially cheap systems) will be good or bad for timing without testing them. I have two cheap mini PC systems that have inexplicably bad time syncing behavior,1300-2000 ns.
and two others with inexplicably good time syncing20-50 ns
. Dedicated server hardware is generally more consistent. All in all, I’m able to sync clocks to within 500 ns or so on the bulk of the systems on my network. That’s good enough for my purposes, but it’s not as good as I’d expected to see.
Manage your data science projects effectively with loguru. Track stages and control logging levels with ease.
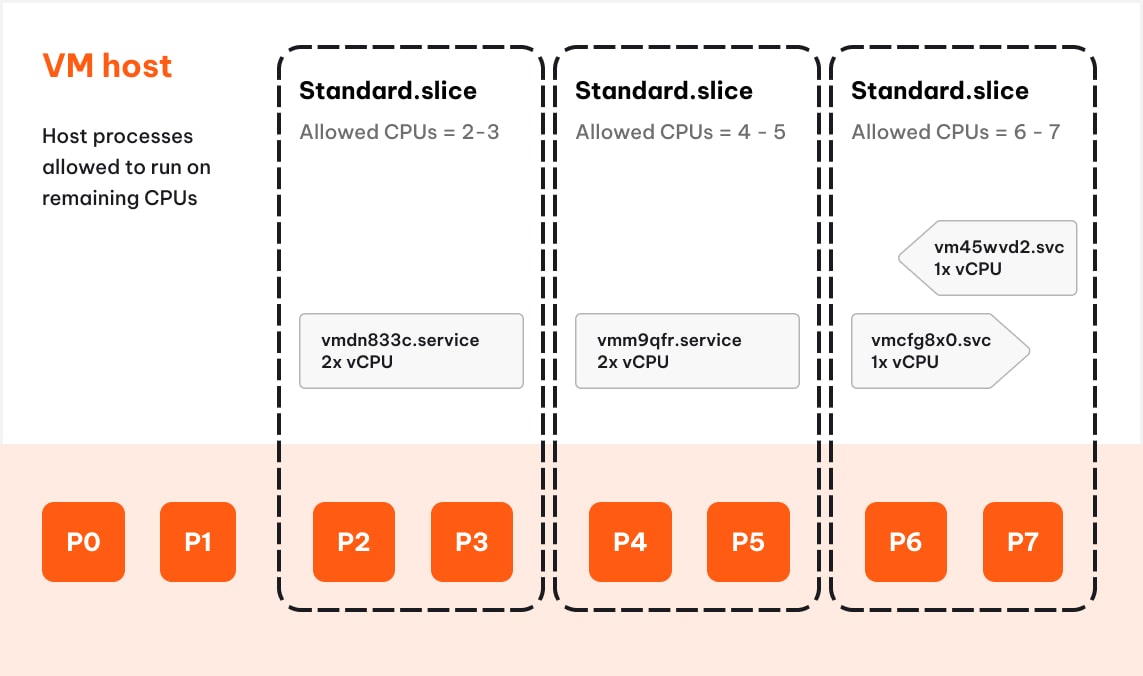
Burstable VMs run on a fraction of CPU and burst to a higher level of CPU usage to support occasional usage spikes. To implement them, we leveraged Control Groups v2 (cgroups v2), a Linux kernel feature that helps manage resource usage. We thought our open-source implementation of burstable VMs might be interesting enough to write about. We also learned a lot about Linux cgroups in the process!

Tired of Annoying Ads and Privacy-Invading Trackers? Here’s How to Take Control...
Dave Peck's home on the web. Dave is an independent software developer, investor, and civic technologist.
Not sure when it happened, but I have been binging self-hosted identity providers like Netflix shows, this season features Authentik, KeyCloak, Synology SSO and Pocket ID. To add to my collection, …
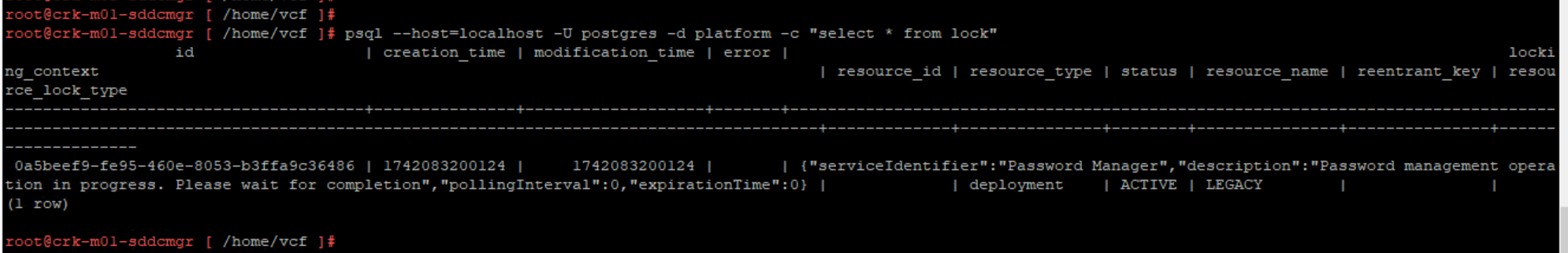
SDDC Manager oprations may not be allowed due to System Lock held by Password Manager operation in progress. A password rotation task may have failed on individual components for various reasons. S…

We all love Python’s comprehensive standard library, but let’s face it – PyPI’s wealth of packages often becomes essential. Sharing single-file, self-contained Python scripts that rely on these external tools can be a headache. Historically, we’ve relied on requirements.txt or full-fledged package managers such as Poetry or pipenv, which can be overkill for simple scripts and intimidating for newcomers. But what if there was a simpler way? That’s where uv and PEP 723 come in. This article delves into how uv harnesses PEP 723 to embed dependencies directly within scripts, making distribution and execution extremely easy.
Part 2 VCF Import Cluster with NFS and activating the overlay.

Today we’re excited to release Railpack — the next iteration of the Railway builder, developed from the ground up based on everything we’ve learned from building over 14 million apps with Nixpacks.
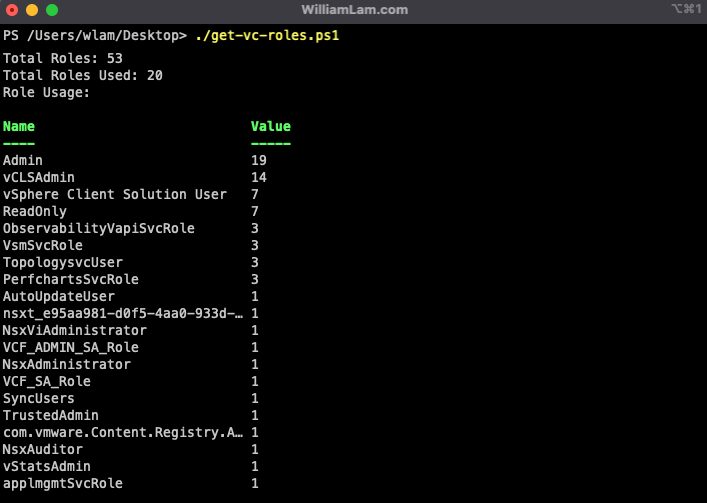
vCenter Server ships out of the box a number of system and custom roles, which can be used or users can create their own custom roles containing the required privileges. If you wanted to understand…
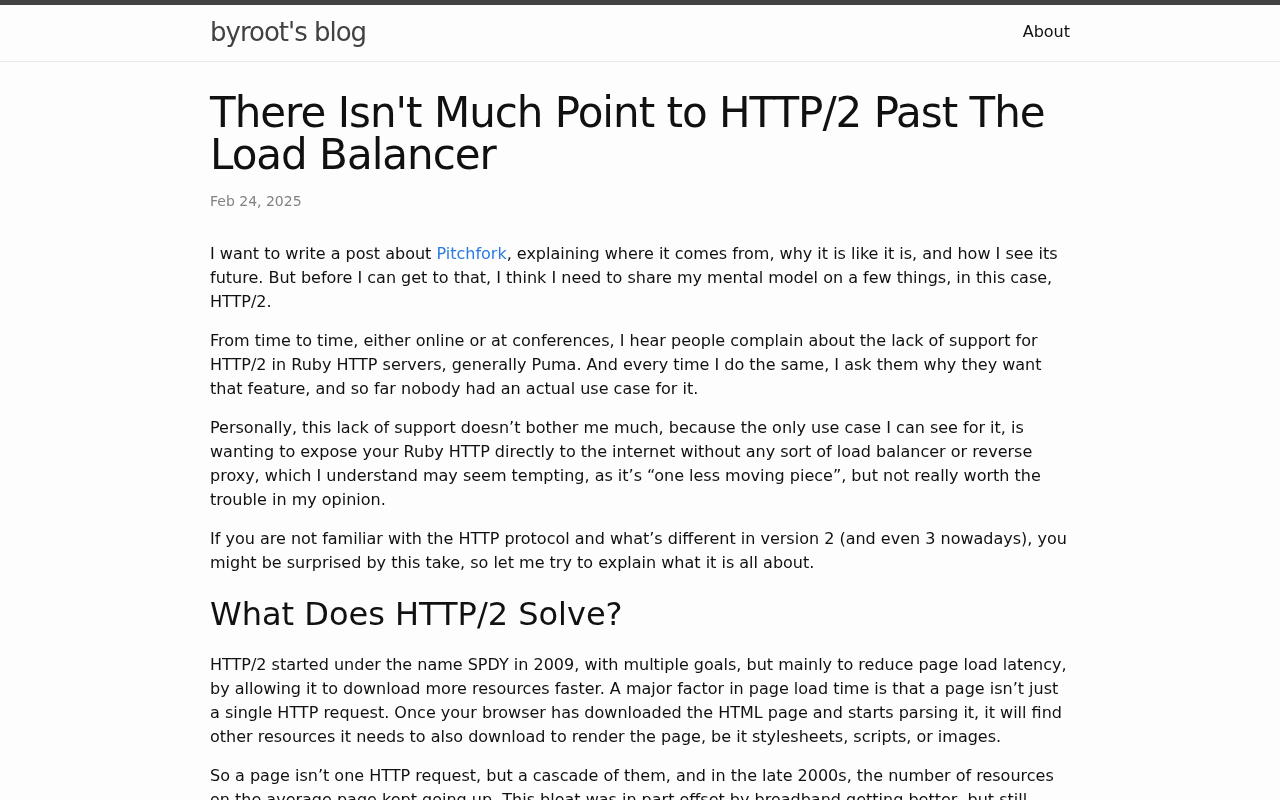
I want to write a post about Pitchfork, explaining where it comes from, why it is like it is, and how I see its future. But before I can get to that, I think I need to share my mental model on a few things, in this case, HTTP/2.
Much of what I do, in multiple fields, could be reduced to one skill: troubleshooting.
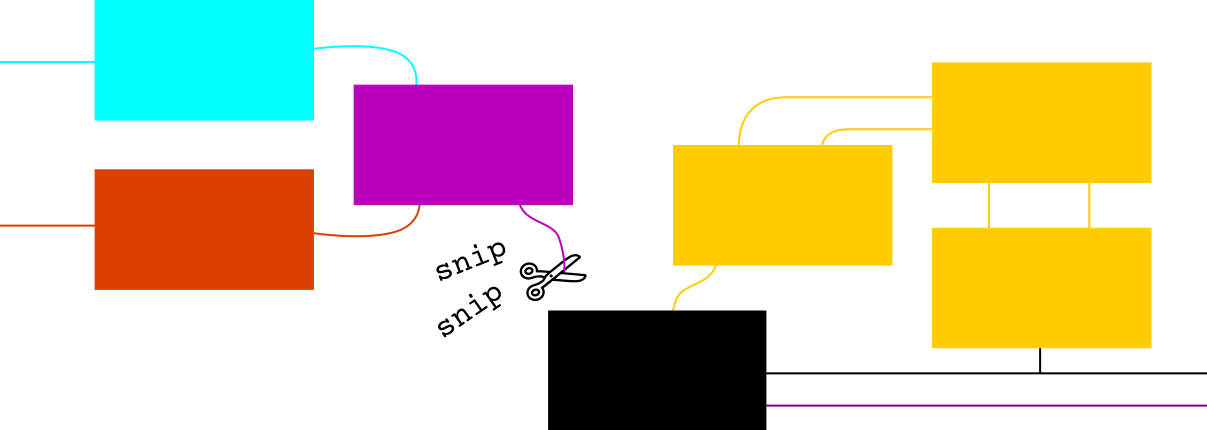
GitHub Actions suggests using code like echo ... >> $GITHUB_ENV, but echo ... | tee -a $GITHUB_ENV is often better.
![Screenshot of [NSX Intelligence] Problème lors du déploiement de NSX Application Platform (NAPP) sous RKE2](/screenshots/nsx-intelligence-probl%c3%a8me-lors-du-d%c3%a9ploiement-de-nsx-applica.png)
Lors d’une nouvelle installation de NSX Intelligence (ou plutôt Security Intelligence maintenant), j’ai rencontré un petit problème inattendu !
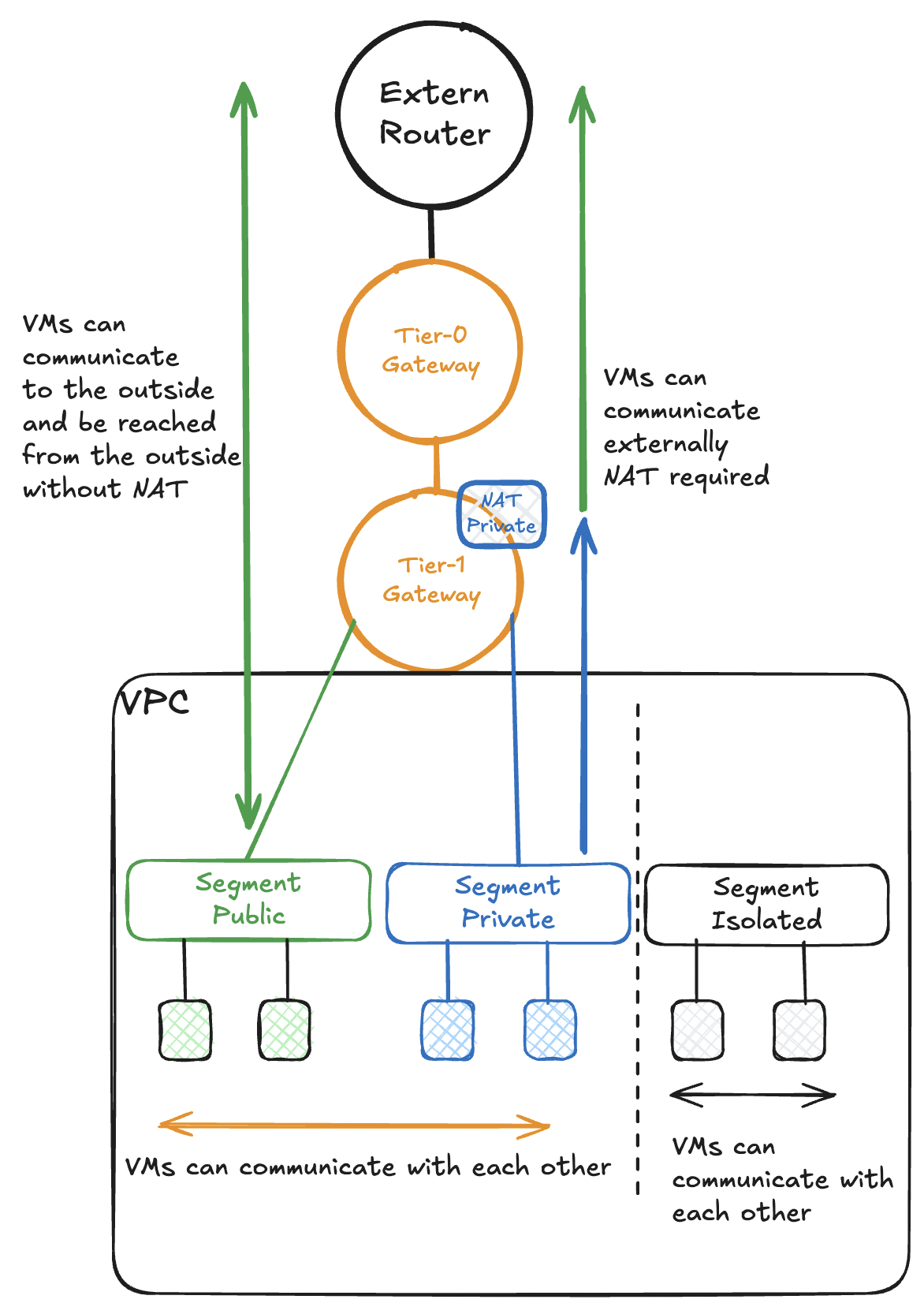
The introduction of VPCs (Virtual Private Cloud) at the network level provides a "self-service" for network, security and other network services in an isolated environment. Those responsible for the VPC can create networks and security rules (within their limits), thus relieving the burden on the network and security teams. It also enables the VPC owners to provide new services more quickly.
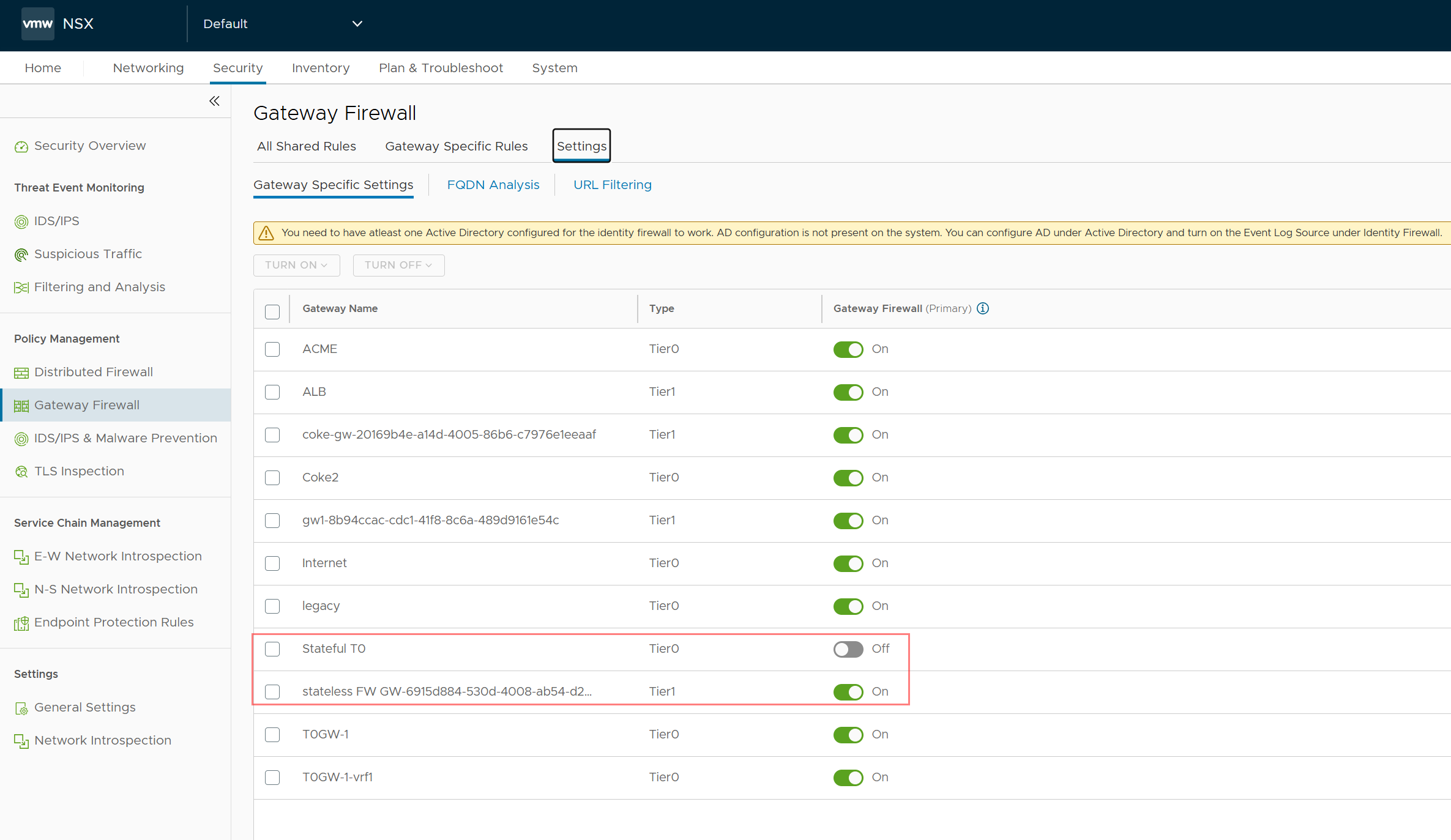
With the new Broadcom licensing changes related to NSX only the stateless firewall is included in the base VCF/NSX license while statefull firewall needs to be licensed separately. VMware Cloud Dir…

Super quick one I want to document here! I got myself on a side quest,
again! No biggie, my ZSH shell was taking ages to load. When I say
ag...
The ABC analysed 29 million stolen codes to help you avoid using an insecure one.
Build reproducibility is often considered as a de facto feature provided by functional package managers like Nix. Although the functional package manager model...

Why the OAuth2 protocol was designed the way it is and how it works.

When you deploy a component using VMware Aria Suite Lifecycle, it stores the credentials in it’s locker. If you need to SSH to a VCF Operations appliance and you dont know the root password, …
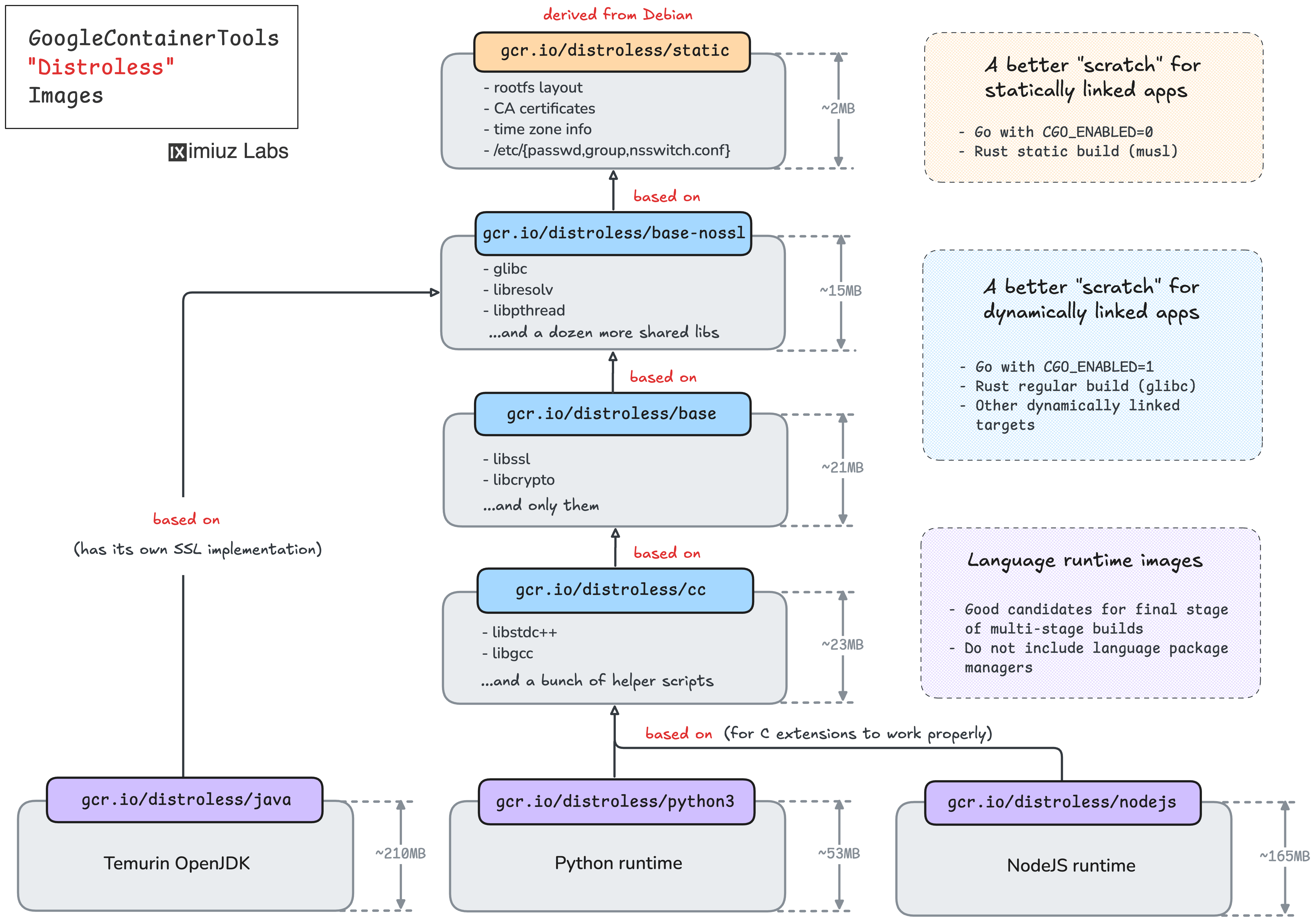
What are these distroless images, really? Why are they needed? What's the difference between a container image built from a distroless base and a container image built from scratch? Let's take a deeper look.
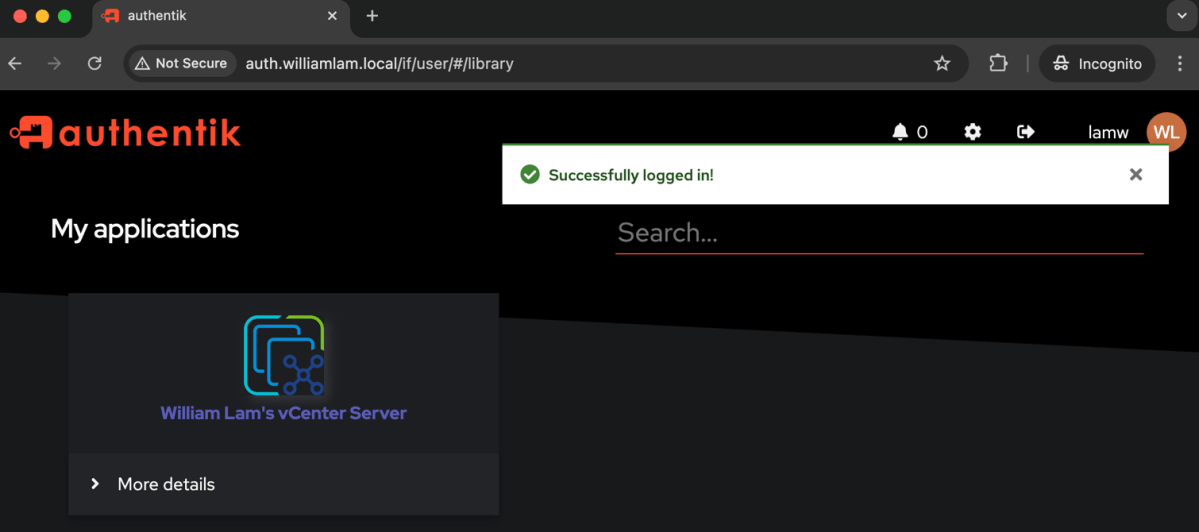
While answering a recent question on the VMware Reddit Community, I came to learn about Authentik, an open source identity provider (IdP), which is pretty feature rich and best of all, you can self…
In light of the above tweet, and Ned Beauman'sHow ‘Factorio’ seduced Silicon Valley — and me(permalink),
I wanted to approximate the magnitude of damage you could inflict with a Mass Steam Gifti
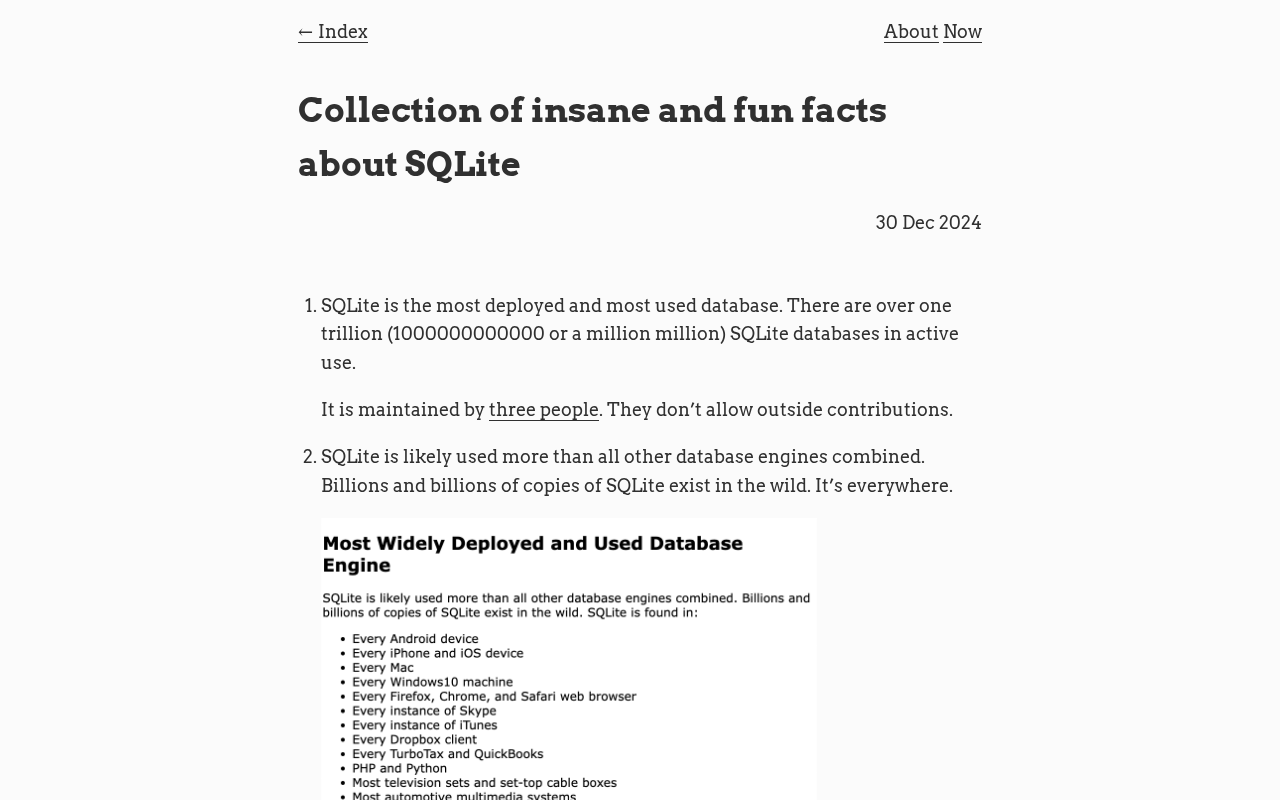
Some of the interesting and insane facts I learned about SQLite
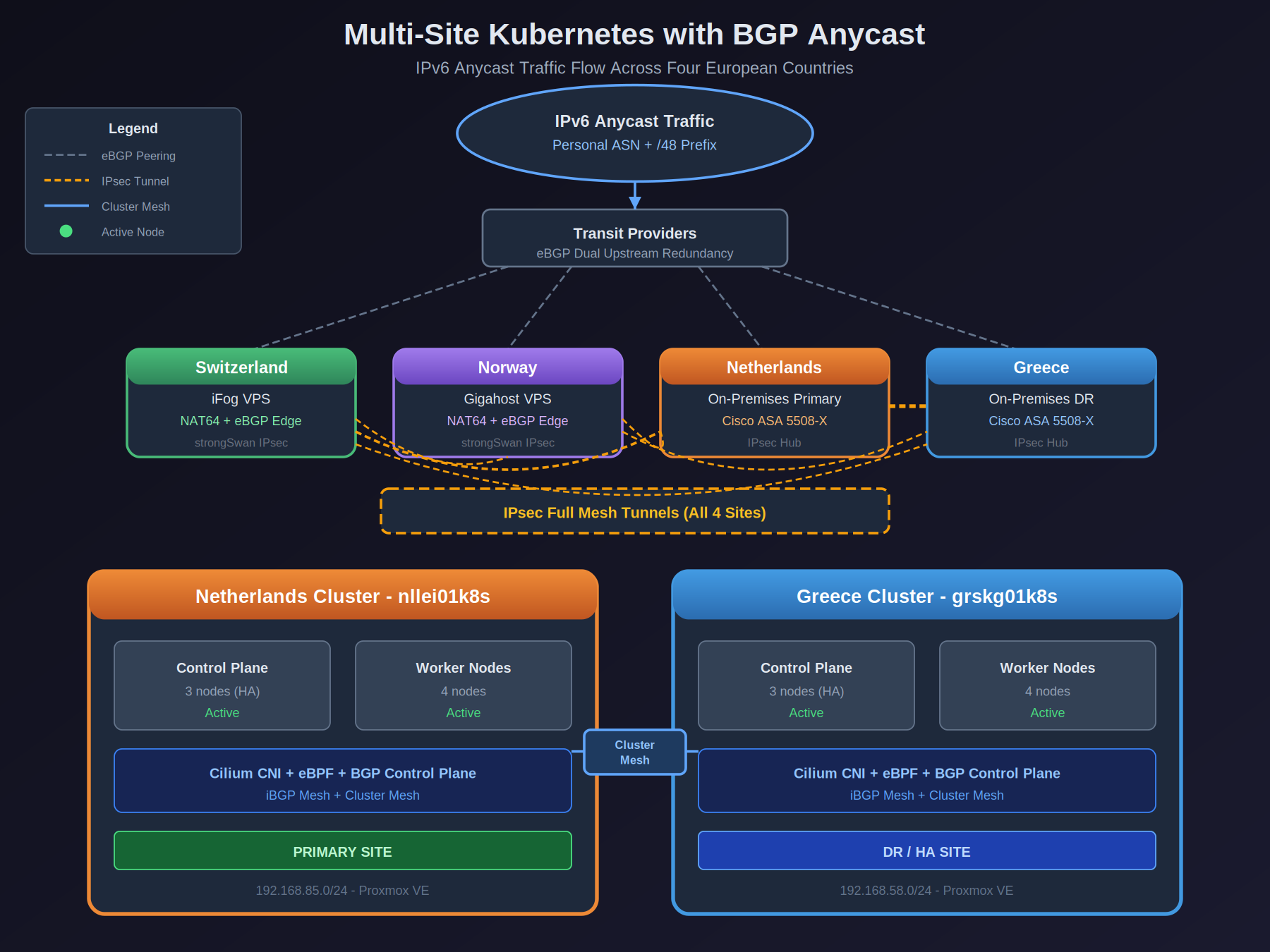
How I connected Kubernetes clusters across 4 countries with my own ASN, BGP peering, and perhaps too many IPsec tunnels

Don't forget to uv self update before trying those
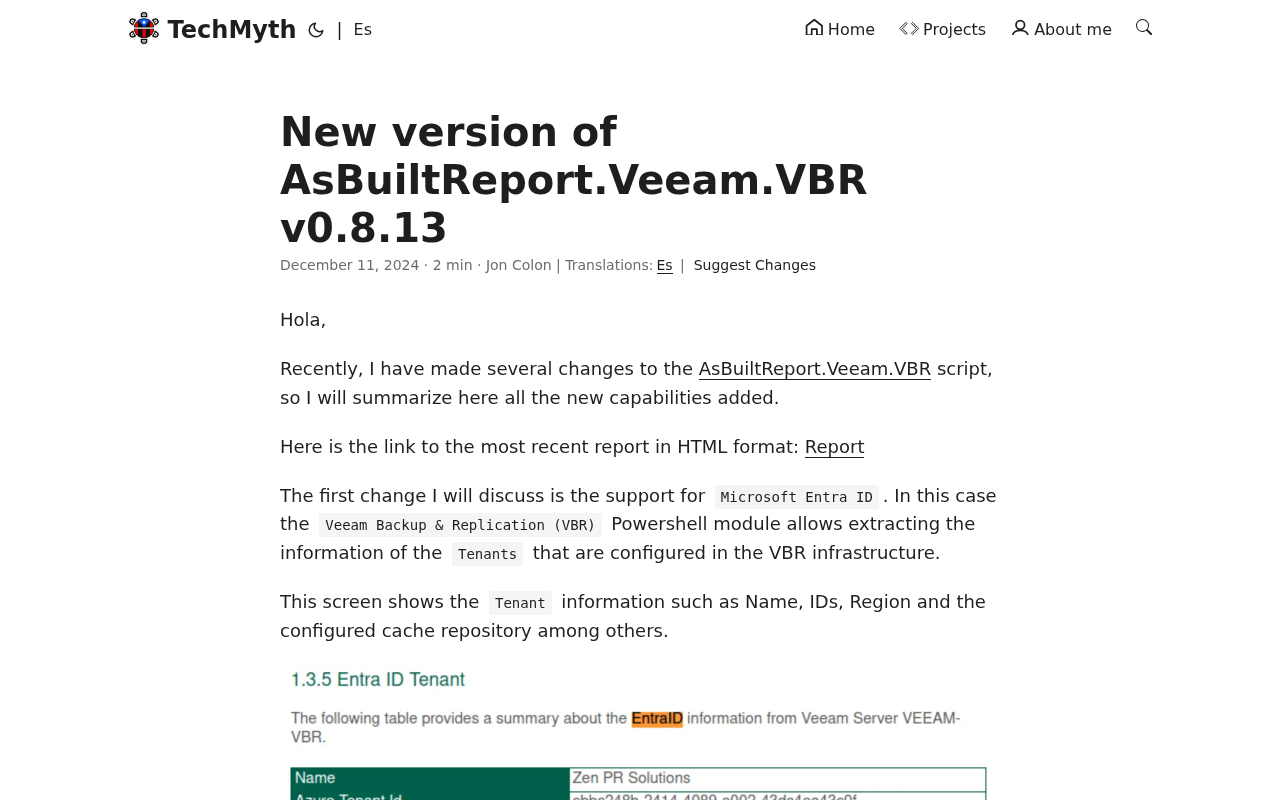
Hola,
Recently, I have made several changes to the AsBuiltReport.Veeam.VBR script, so I will summarize here all the new capabilities added.
Here is the link to the most recent report in HTML format: Report The first change I will discuss is the support for Microsoft Entra ID. In this case the Veeam Backup & Replication (VBR) Powershell module allows extracting the information of the Tenants that are configured in the VBR infrastructure.
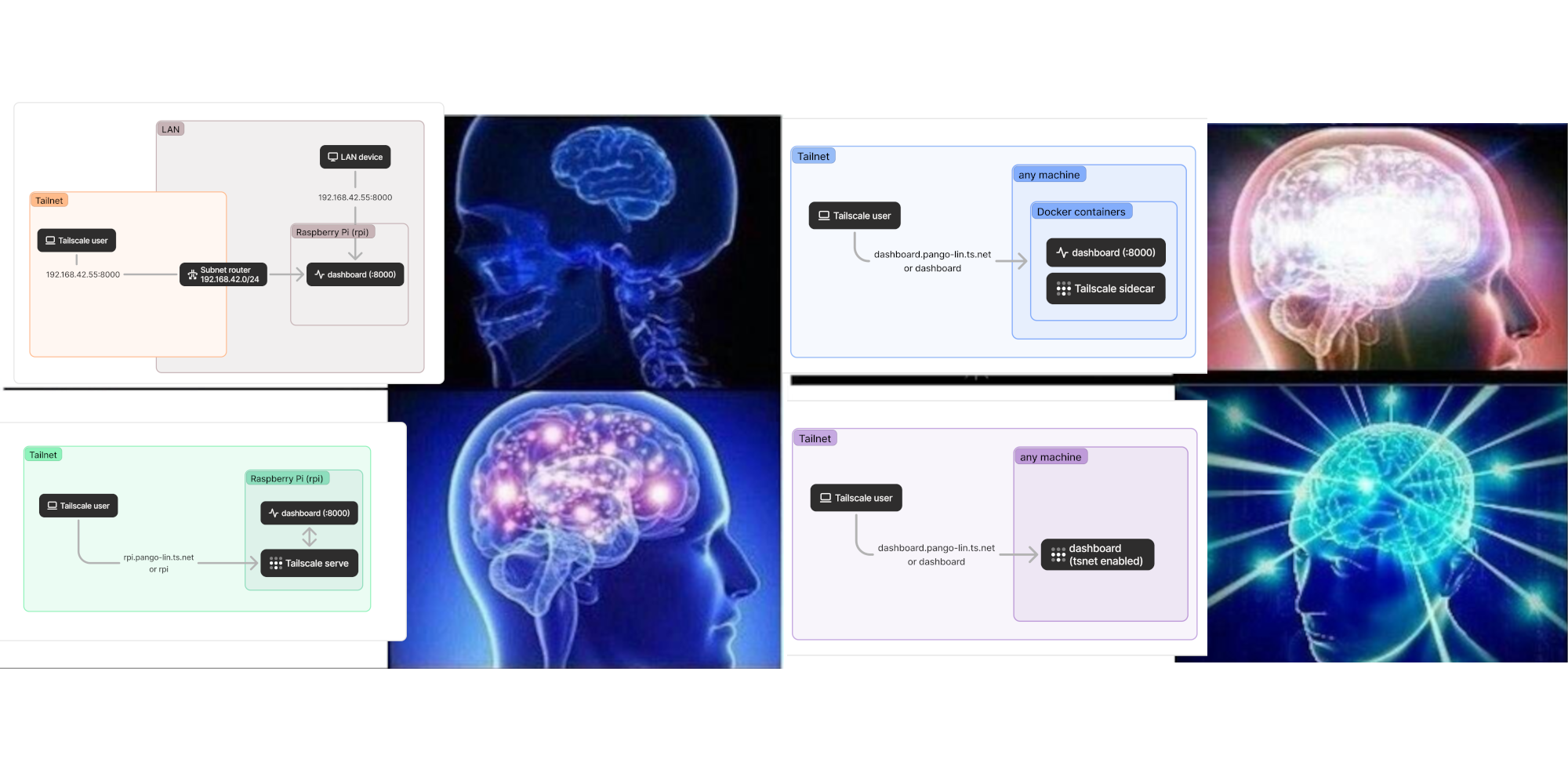
Let’s say you’ve got some kind of service you want to connect to through Tailscale. How do you make it accessible over your tailnet? It's easy for decision paralysis to set in here, so let's consolidate some of the possibilities in one place.
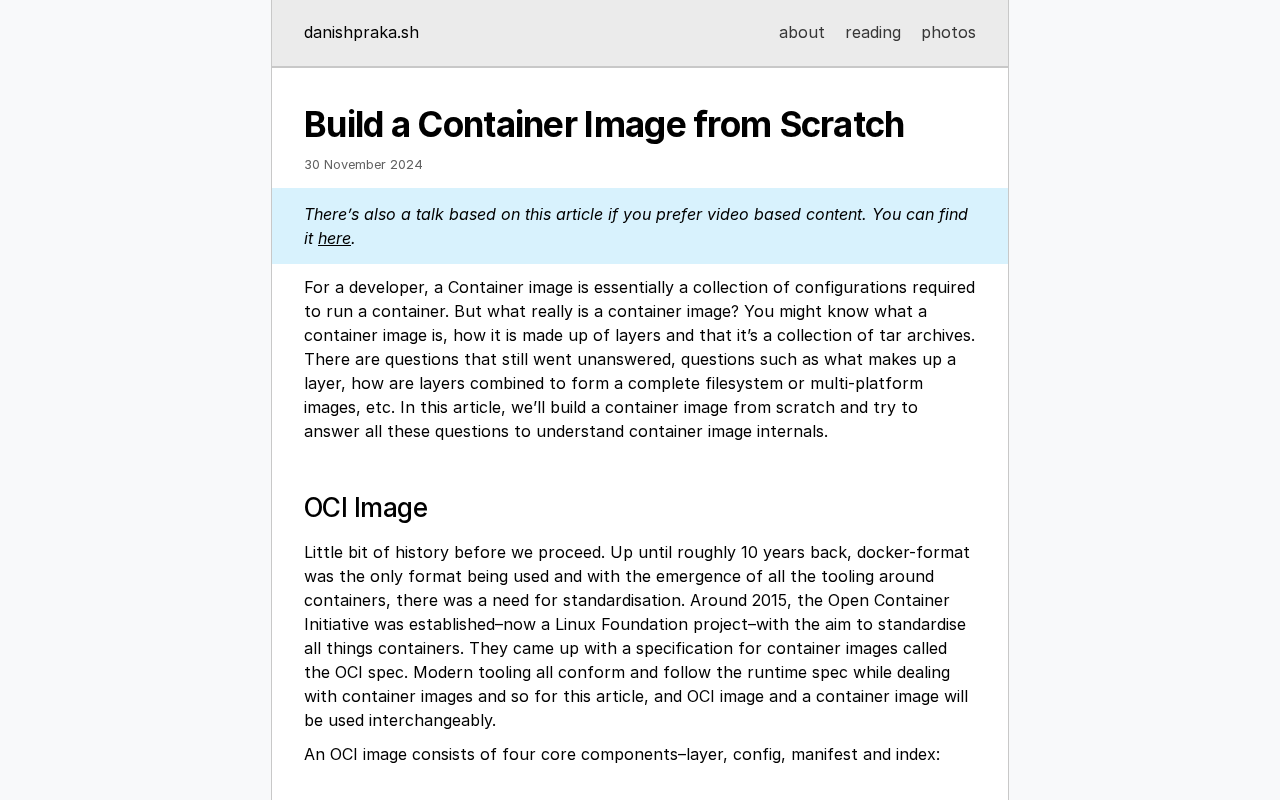
30 November 2024
Why you should use MAC Learning

Mac's Tech Blog
Using Linux's fancy networking to keep torrent traffic private

Let's walk through a common scenario.
A rant about caring

Ça fait un moment que j’utilise Github comme support OAuth2 pour m’authentifier sur des applications. Toutefois, je me suis toujours contenté de suivre une documentation sans réellement chercher à comprendre ce qu’il se passait sous mes yeux chaque fois que je voulais m’authentifier.
De ce fait, je me suis motivé à écrire cet article à propos du SSO. L’objectif est de découvrir les mécanismes disponibles pour gérer une grande quantité d’utilisateurs et leurs accès aux applications de l’infrastructure.
After having automated the downloading of bundles for an offline depot in my lab I got the idea of experimenting with hosting it using a containerized nginx instance.

While I was testing the new Release 8.0.3 from Broadcom, I ran into a few problems getting my nested lab...
Last week I wanted to replace my OpenVPN setup with WireGuard. The basics were well-documented, going beyond the basics was a bit trickier. Let me teach you want I learned.
The basics But first, let’s summarize the basics. I have a server with a hosting provider that I want to use as a VPN server. I won’t delve into details here, since there are so many great explanations on the web already (here, here, here or here), let’s just make a quick summary of a simple setup, as a base for discussing the (slightly) more advanced usages I had to configure myself:
Kubernetes doesn't load balance long-lived connections, and some Pods might receive more requests than others. If you're using HTTP/2, gRPC, RSockets, AMQP or any other long-lived connection such as a database connection, you might want to consider client-side load balancing.
Créer une infrastructure VPN hybride avec Headscale pour connecter des serveurs locaux et distants.
Smudge.ai is a Chrome extension that gives you ChatGPT-powered shortcuts in your right-click menu.

Découvrons ensemble comment utiliser le GPG pour sécuriser ses échanges (fichiers, mail, commits) et comment stocker ses clés sur une Yubikey pour plus de sécurité !
Adventures trying to minimise disk usage for servers

Dans cet article, je vous donne une première définition de ce qu'est le GitOps et comment le mettre en place avec ArgoCD dans un environnement Kubernetes.

In my 2022 December rumination about vCF I delved into how a union between VMware Cloud Foundation and a credential storage solution could make for a powerful combination.

After a homelab crash, the VCSA file-based backup isn't working anymore. In this post I'm describing how I was able to get the VMware Postgres Archiver service back into operating state by interfere with vCenters vPostgres instance.

Vault est un outil de gestion des secrets développé par Hashicorp. Il permet de stocker et de gérer ces derniers de manière sécurisée. Dans cet article, nous allons voir comment utiliser Vault pour gérer les secrets de vos applications.
Learn why DNS needs security through tacos, crabs, and cryptographic laughs. How DNSSEC Works turns complex internet plumbing into an illustrated adventure.

Slow Rust Builds?
Here are some tips to speed up your compile times.
This list was originally released on my private blo…

Découvrez la sélection de nos derniers travaux. Des projets Cyllene multiples regroupant de nombreux métiers afin de vous offrir une prestation sur-mesure.

Overview VMware recently released full support for Azure Active Directory (now called Entra ID) integration with vCenter with release 8.0 U2. Unfortunately, their documentation about integration had some major gaps, compelling us to write this guide. VMware’s documents initially recommended opening your vCenter server URL to the public (which you should NEVER do). They’ve since...
Sysadmin doing syadmin stuff
Instead of using sshpass to non-interactively provide an SSH password, here is a simpler approach by harnessing the built-in features of OpenSSH...

Prometheus est une solution de supervision créée par Soundcloud en 2012 et open-sourcée en 2015. C'est un incontournable qui se démarque via l'intégration à de nombreux services tiers non supportés nativement.
Mapping Pihole to Tailscale and enabling subnet routing has made accessing my homelab outside the house an absolute joy.

Terraform Associate est une certification officielle de HashiCorp. Celle-ci permet de valider vos connaissances sur Terraform via un examen en ligne. Je vous partage mon expérience dans cet article !

Want to secure your Proxmox server with a trusted SSL certificate from Let's Encrypt? Check out my post! Includes Home Assistant integration too!
Exploring the balance between relying on AI assistance like ChatGPT and maintaining personal skills in a world of increasing AI capabilities.

Cert-Manager est un programme permettant de gérer les certificats (ainsi que leurs renouvellements) sur des clusters Kubernetes. Nous allons voir comment déployer Cert-Manager et générer nos premiers certificats
Lorsque nous avons de nombreux serveurs, il convient d'automatiser chacun des déploiements que nous réalisons. Et lorsque la majorité sont sous Debian, ces déploiements peuvent prendre la forme de fichiers .deb. Nous verrons donc sur cette page comment créer notre propre dépôt Debian
A next-generation sharing platform built on top of OpenZiti, a programmable zero-trust network overlay.

Lorsqu'on multiplie les infrastructures (locales, distante etc..), avoir un VPN de Mesh permet de vous faciliter la vie. Nous allons donc installer et configurer Tinc

Historically, we have rarely talked about how our servers fetch
the content from the Internet. In this blog we’re going to cover
this gap. We'll discuss how we manage Cloudflare IP addresses
used to retrieve the data from the Internet, how our egress
network design has evolved, how we optimized it for best use
of available IP space and introduce our soft-anycast technology.
This is my documentation of how I publish my notes from a private [[Obsidian]] vault to my
How Relational Databases Work. This post talks about how indexes and transactions work on the inside of relational databases.
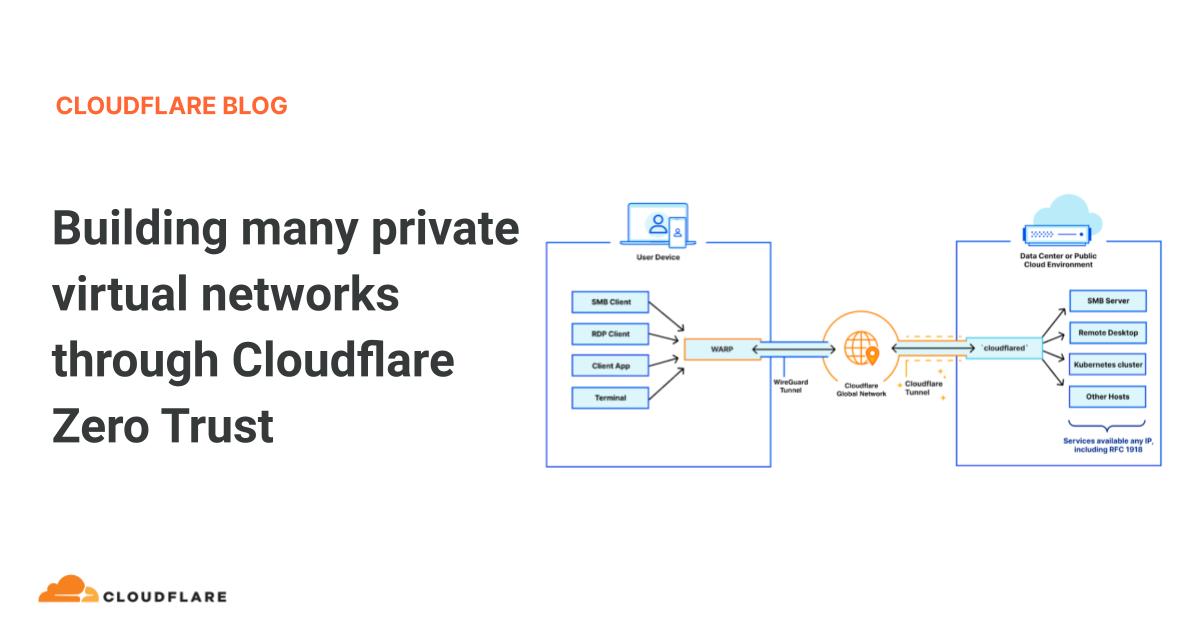
Starting today, we are thrilled to announce that you can start building many segregated virtual private networks over Cloudflare Zero Trust, beginning with virtualized connectivity for the connectors Cloudflare WARP and Cloudflare Tunnel
A technical dive into traditional TCP proxying over HTTP
Today at 1651 UTC, we opened an internal incident entitled "Facebook DNS lookup returning SERVFAIL" because we were worried that something was wrong with our DNS resolver 1.1.1.1. But as we were about to post on our public status page we realized something else more serious was going on.
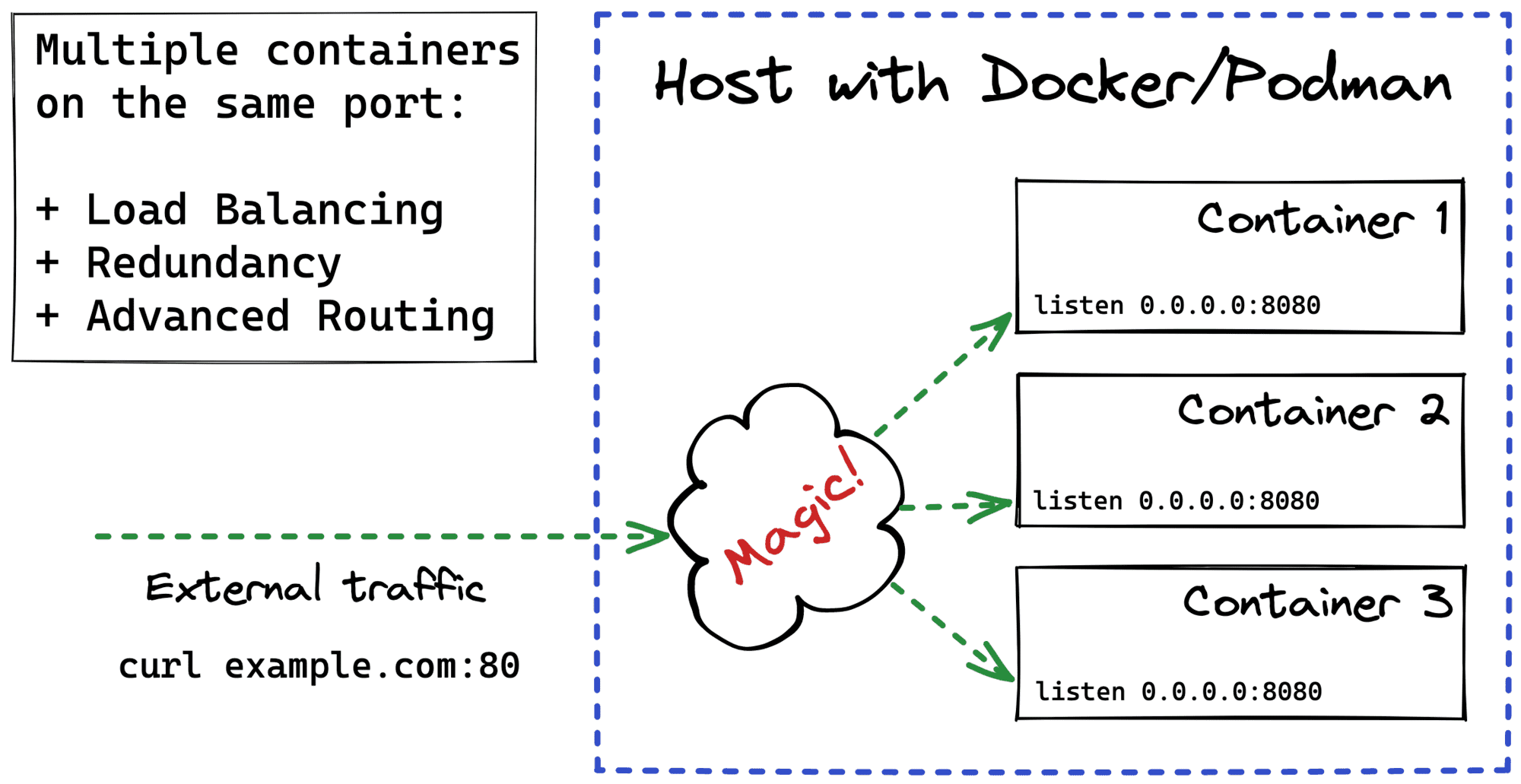
How Docker publishes container ports on the host? How to use SO_REUSEPORT to make multiple containers listening on the same port? How to use iptables to make multiple containers exposed on the same port?
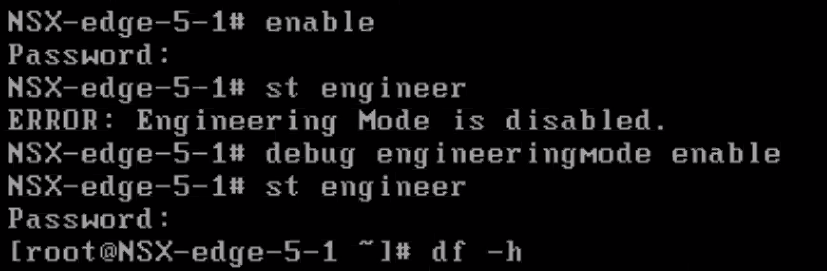
If you have ever tried to troubleshoot an NSX-v Management Appliance or Edge, you probably noticed that you are quite limited in the execution of your controls. That’s because in NSX-v you are standardly limited with most of the time only esxcli, even when you are logged in as admin.
To get past
Find the right requests and limits can be tricky. Instead of guessing, you could inspect the application at runtime and extrapolate the values.
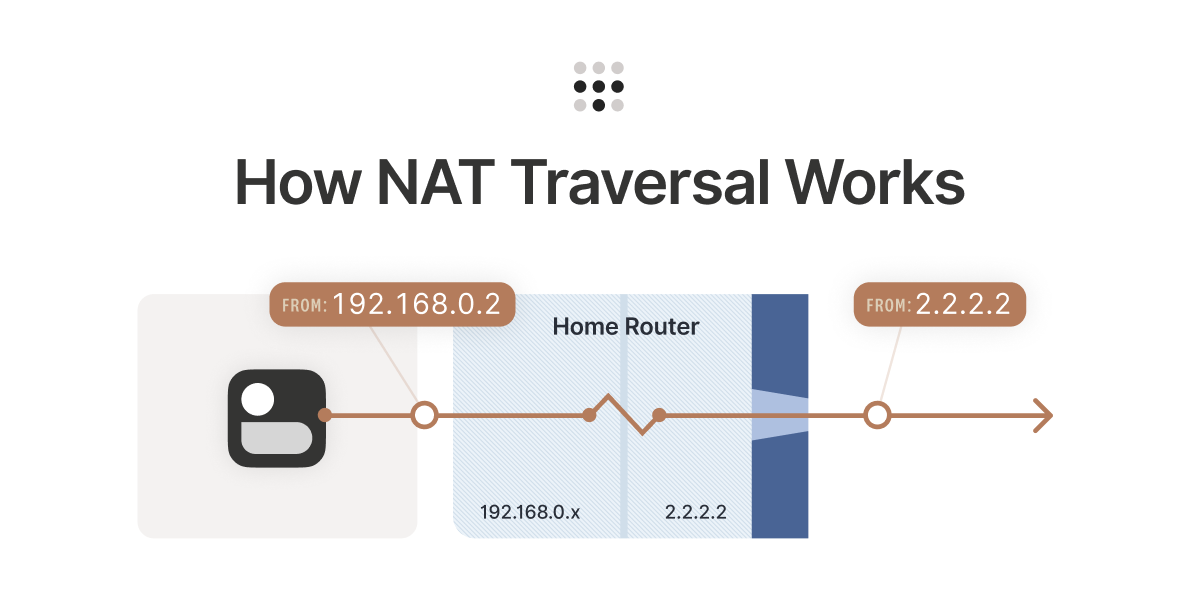
Learn how NAT traversal works, how Tailscale can get through and securely connect your devices directly to each other.
Todays topic is VMware Cloud Director inter-tenant routing with a NSX-T backed provider VDCs (pVDC). The reason for writing this post is that some use-cases require routed connectivity between Org VDC

Docker vous permet d’empaqueter facilement vos applications et services dans des conteneurs afin de pouvoir les utiliser partout. Cependant, lorsque vous tra…
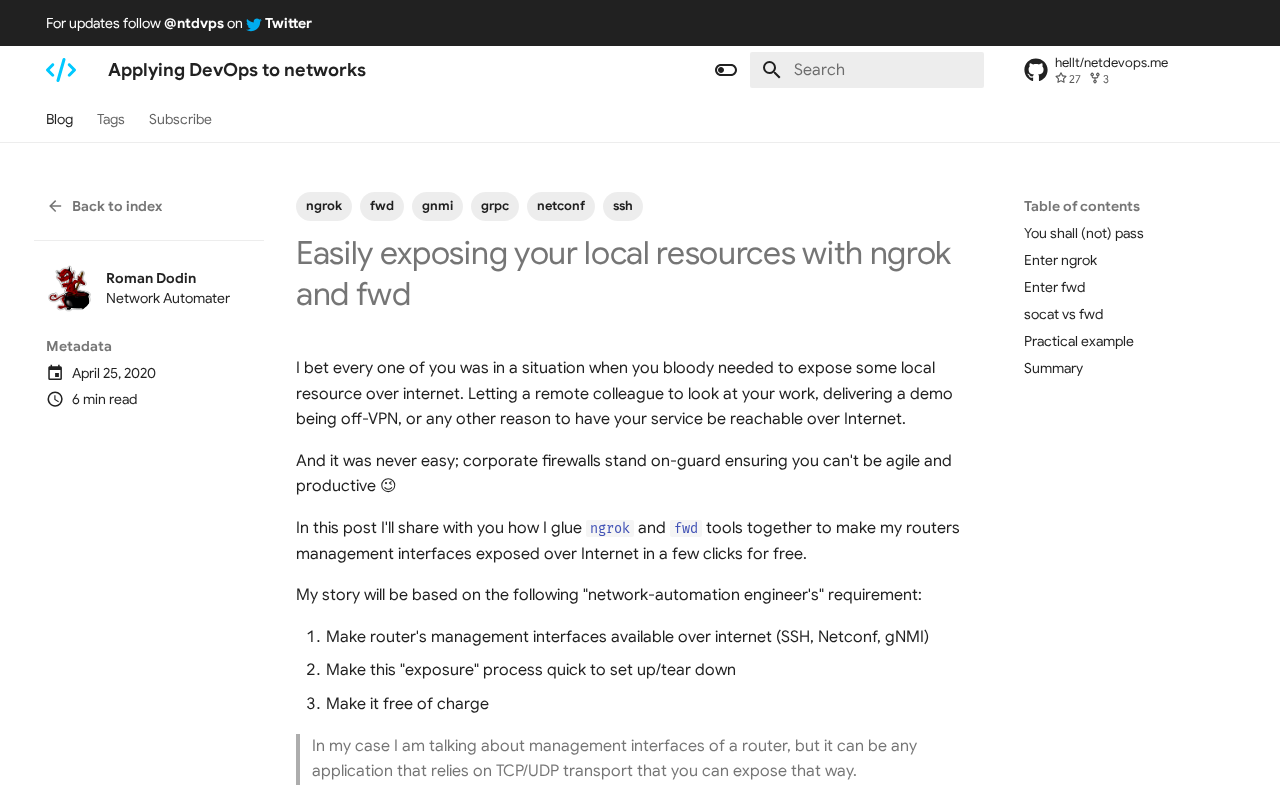
Applying DevOps to networks.
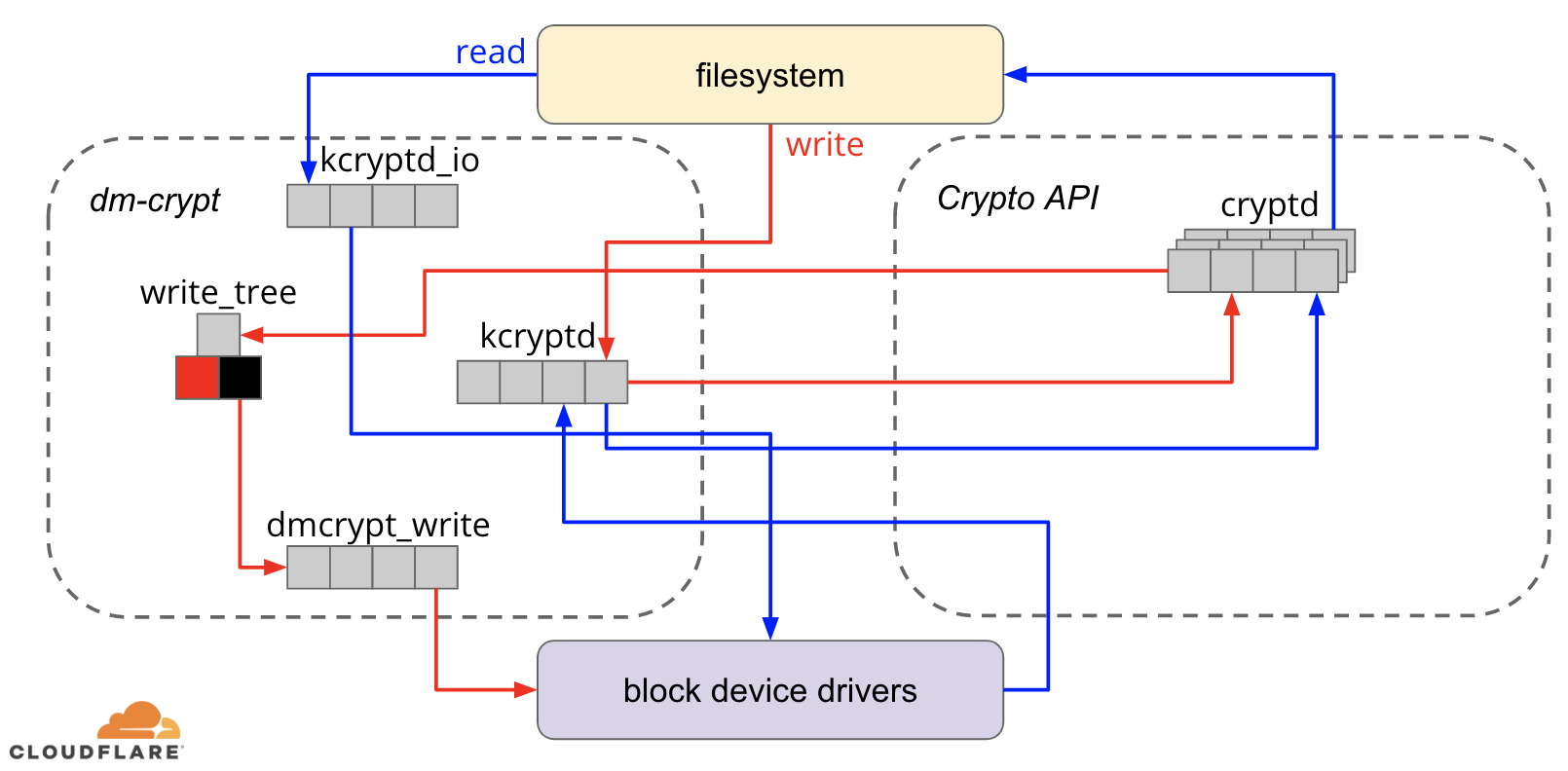
In this post, we will investigate the performance of disk encryption on Linux and explain how we made it at least two times faster for ourselves and our customers!
A rundown of seven common mistakes is system architecture diagrams and how to fix them

Monitor CPU, GPU, and storage, clean junk files, check battery health, and keep your Mac fast with Sensei. Free download.

Guest Post: Why does half the Internet use a TTL of 1 minute or less?
How to backup and restore K8s applications on vSphere
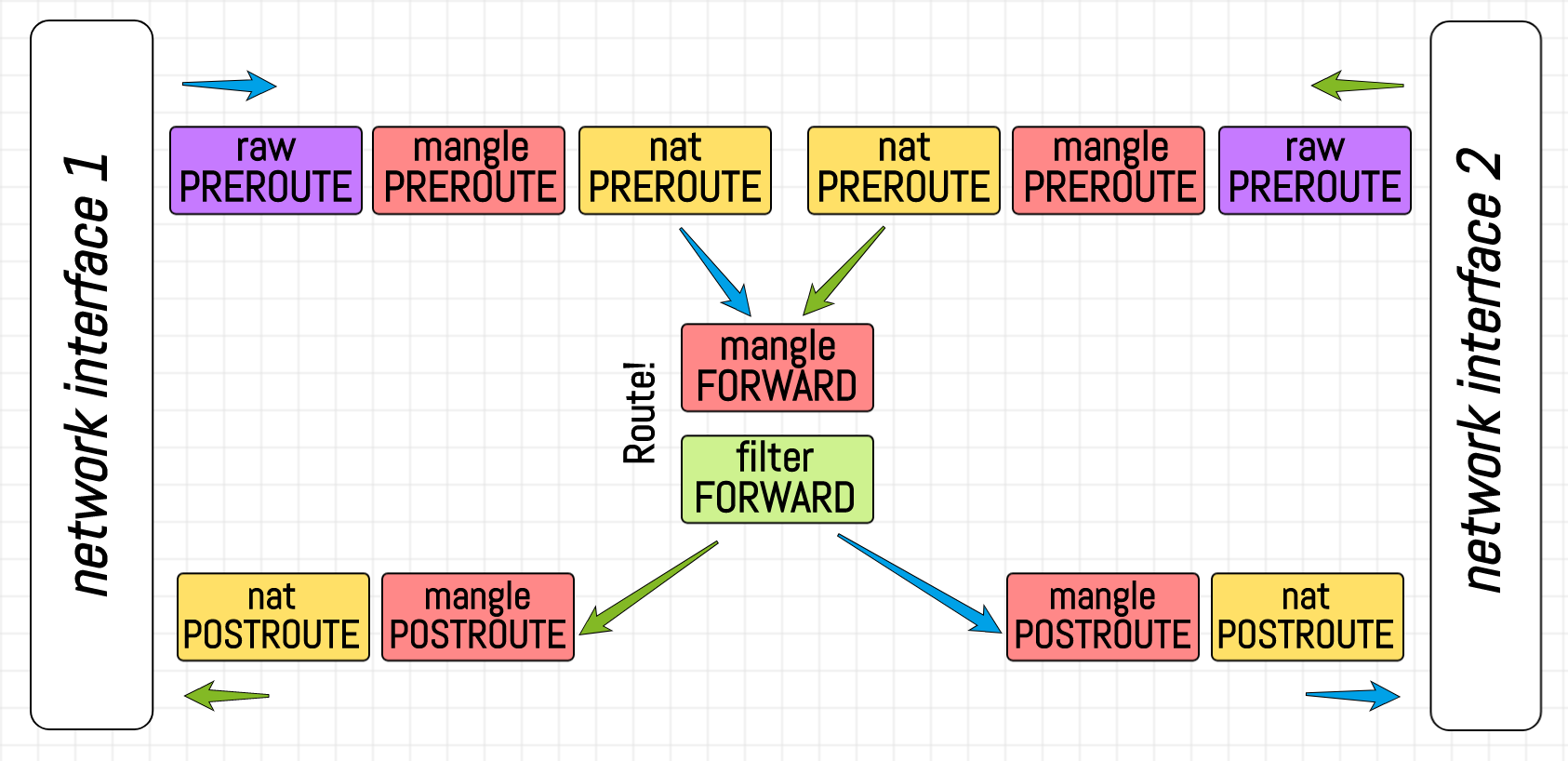
What are iptables chains, rules, policies, and tables? Describe iptables in layman's terms.
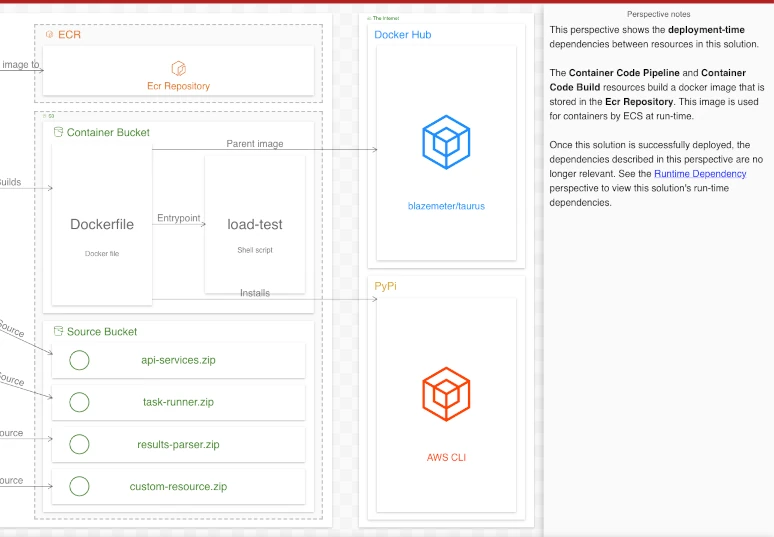
Implementation of redundant site-to-site VPNs on Linux with WireGuard (instead of IPsec) and BGP.
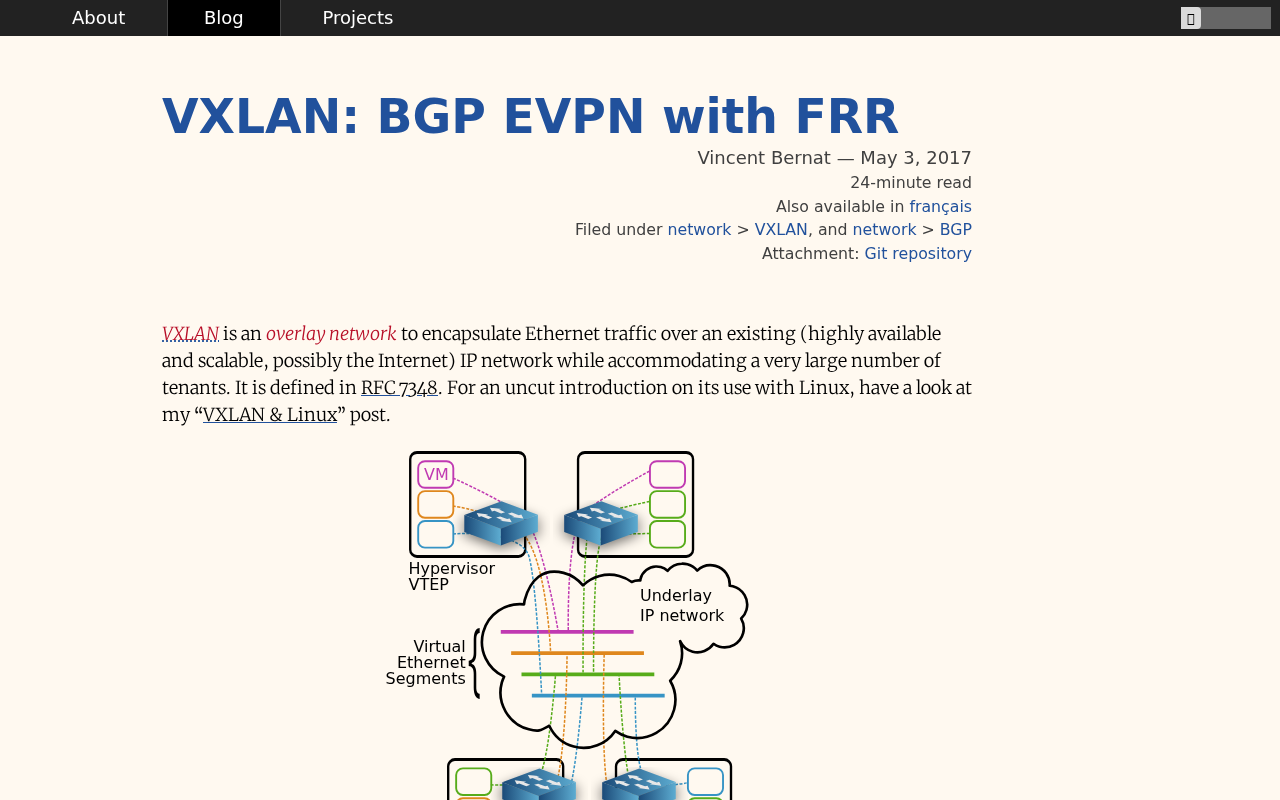
VXLAN is an overlay network for L2 traffic over an existing IP network. One deployment option is BGP EVPN.
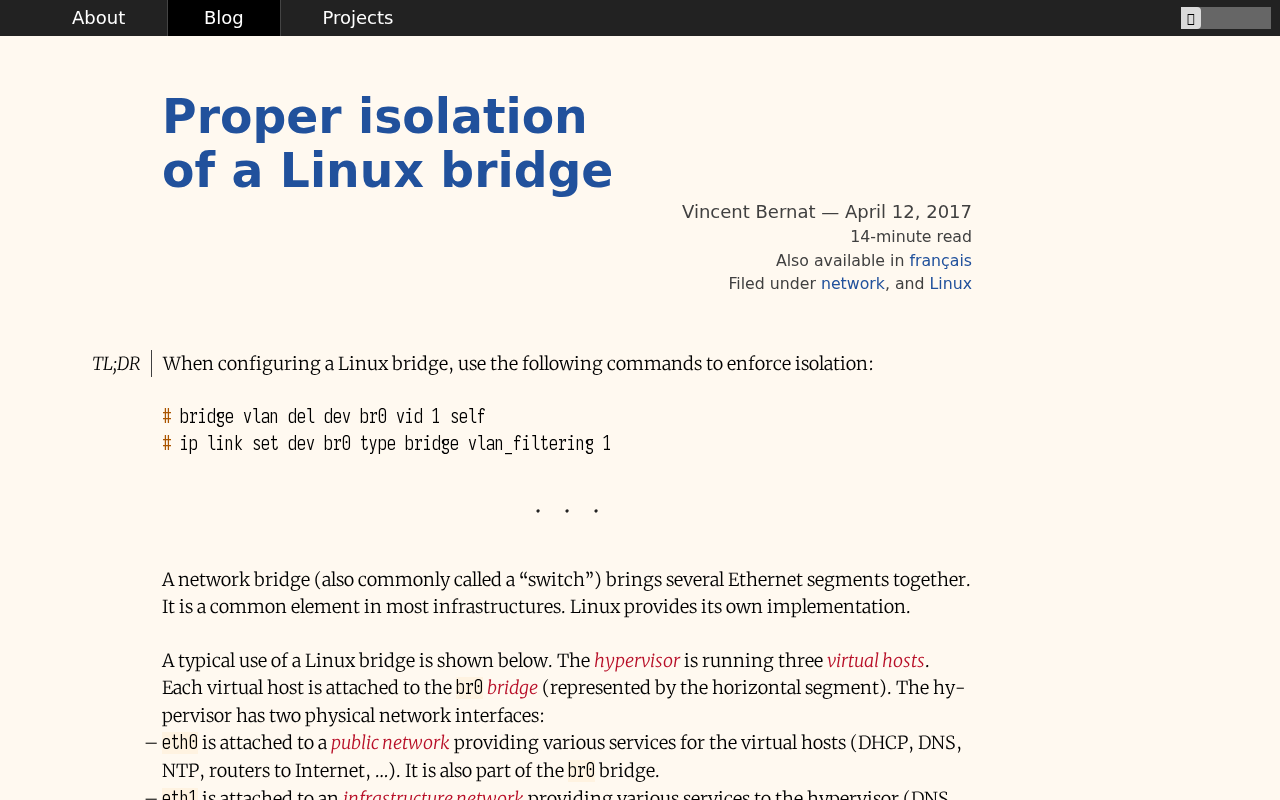
On Linux, a network bridge without any IP address configured will still process IP packets. How to disable such a feature?

Automation is an increasingly interesting topic in pretty much every technology discipline these days. There’s lots of talk about tooling, practices, skill set evolution, and more - but little conversation about fundamentals. What little is published by those actually practicing automation, usually takes the form of source code or technical whitepapers. While these are obviously valuable, they don’t usually cover some of the fundamental basics that could prove useful to the reader who wishes to perform similar things in their own organization, but may have different technical requirements.

A short while back I participated in an internal event. A number of priority customers of our internal cloud service were invited for a feedback session, to voice their thoughts, listen to roadmap sessions and just to get to know each other.
There was one comment made there by one of the participants that has been on my mind since then, and it was something along the lines of:
“I have been using AWS longer than I have been using our internal cloud service – that is more than 5 years.
In a recently published article, Paul Vixie, past author and architect of BIND, one of the most popular internet domain servers, explains why DNS...
tcpdump is the world's premier network analysis tool—combining both power and simplicity into a single command-line interface. This guide will show